What is a Proxy IP?
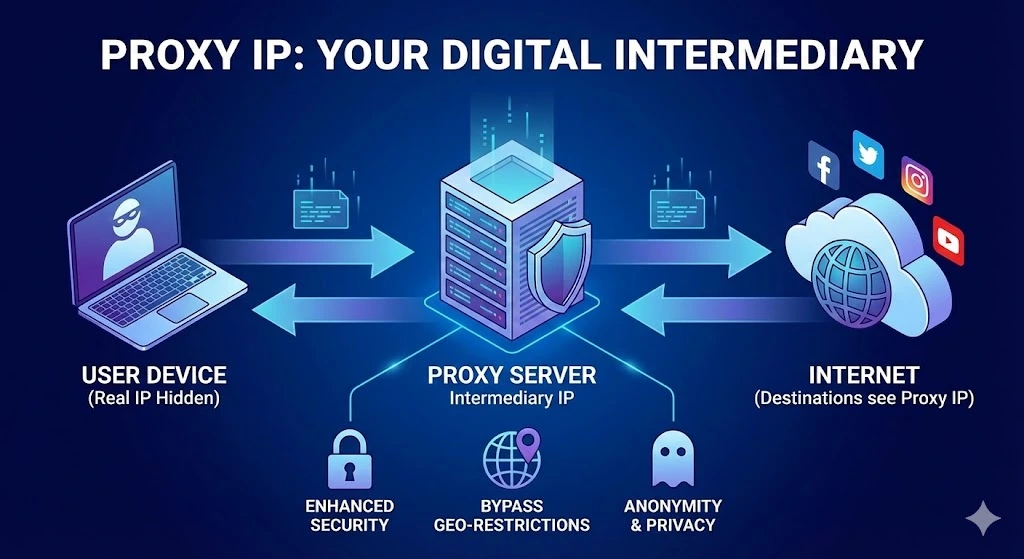
A proxy IP is an intermediary IP address used to mask or relay your original IP address when accessing the Internet. It acts as a gateway between the user and the web. When a request is made to access a website, the proxy server (which uses the proxy IP) forwards that request, hiding the user’s real IP address from the website. This allows for increased privacy and anonymity when browsing online.
Table of Contents
How Proxy IP Works
When you use a proxy, your device sends a request to the proxy server, which forwards it to the target website. The website then sees the request as coming from the proxy server, not your IP. This shields your original identity and location from the website. Afterward, the website’s response is returned to the proxy server, which forwards it to you.
Types of Proxy IPs
HTTP Proxies: These only work for web pages and are great for browsing.
SOCKS Proxies: They handle a wider range of traffic, including emails, torrent files, and FTP.
Transparent Proxies: These identify themselves and pass the original IP address, often used in caching.
Anonymous Proxies: These hide the user’s IP address but identify themselves as proxies.
High Anonymity Proxies: These provide maximum privacy by not identifying themselves as proxies and completely hiding the user’s IP.
Key Functions and Use Cases
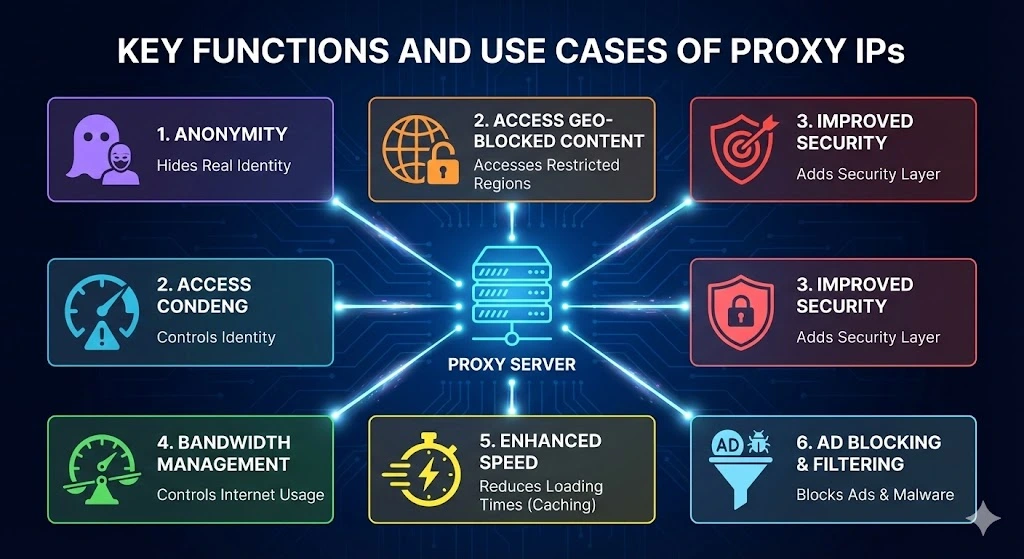
1. Anonymity: Proxy IPs hide your real identity online, allowing you to browse the web without revealing personal information.
2. Access Geo-Blocked Content: Proxies enable users to access content that is restricted in certain regions by assigning IPs from specific locations.
3. Improved Security: By masking the original IP address, proxy servers add a layer of security, making it harder for hackers to target the user directly.
4. Bandwidth Management: Proxies can help organizations manage and control internet bandwidth usage, preventing congestion.
5. Enhanced Speed: Certain proxies can cache web pages, reducing loading times for frequently accessed websites.
6. Ad Blocking and Filtering: Proxy servers can block ads, malware, or filter content to ensure a safer browsing experience.
Common Use Cases for Proxy IPs
1. Businesses: Companies use proxies for security, load balancing, and to prevent unauthorized access to their internal systems.
2. SEO and Marketing: Marketers use proxies to gather competitor data or analyze web traffic from different locations.
3. Streaming: Users rely on proxy IPs to bypass geo-restrictions and access content not available in their regions.
4. Privacy Enthusiasts: Those concerned with online privacy use proxy IPs to hide their real IP address while browsing.
The Difference Between Proxy and VPN
While both proxies and VPNs hide your IP address, a VPN encrypts all your internet traffic, offering a more secure connection. Proxies generally do not encrypt data, but they can be faster than VPNs for some use cases since they don’t handle heavy encryption.
Final Thoughts
Proxy IPs are essential tools for maintaining privacy, accessing restricted content, and improving online security. Whether for personal use, business operations, or marketing analysis, proxies offer a flexible solution to interact with the web more effectively. Some of the most popular proxy providers include Luminati, Smartproxy, and Bright Data, offering a range of services tailored to different needs.
Trusted IPv4 Leasing for Business Growth
Get enterprise-grade IPv4 space quickly, with seamless deployment and end-to-end management.
Get Started with i.leaseArticles connexes

Primauté du code en cours d’exécution : pourquoi la location d’adresses IPv4 doit être jugée sur la base de preuves opérationnelles
La location IPv4 commence souvent par une question simple : Ce fournisseur peut-il nous fournir les adresses ? Mais pour les entreprises qui dépendent de l’IPv4 pour l’hébergement, le VPN, le SaaS, le cloud, les télécommunications, la sécurité, la livraison d’e-mails ou les plateformes destinées aux clients, cette question ne suffit pas. Une meilleure question est : Cette structure IPv4 peut-elle prouver qu’elle fonctionne sur le plan opérationnel ? Related Posts Understanding Operational Risk in IPv4 Address Markets IPv4 has long stopped being a simple technical identifier system. It has become a constrained, priced, and operationally embedded infrastructure Primauté du code en cours d’exécution : pourquoi la location d’adresses IPv4 doit être jugée sur la base de preuves opérationnelles La location IPv4 commence souvent par une question simple :Ce fournisseur peut-il nous fournir les adresses ?Mais pour les entreprises Risques liés au renouvellement d’IPv4 : quand le manque de responsabilisation se transforme en trahison du code en cours d’exécution La plupart des entreprises entrent sur le marché IPv4 avec un objectif simple. Elles ont besoin d’adresses. Peut-être en ont-elles .related-post {} .related-post .post-list { text-align: left; } .related-post .post-list .item { margin: 5px; padding: 10px; } .related-post .headline { font-size: 18px !important; color: #999999 !important; } .related-post .post-list .item .post_thumb { max-height: 220px; margin: 10px 0px; padding: 0px; display: block; } .related-post .post-list .item .post_title { font-size: 16px; color: #3f3f3f; margin: 10px 0px; padding: 0px; display: block; text-decoration: none; } .related-post .post-list .item .post_excerpt { font-size: 13px; color: #3f3f3f; margin: 10px 0px; padding: 0px; display: block; text-decoration: none; } @media only screen and (min-width: 1024px) { .related-post .post-list .item { width: 30%; } } @media only screen and (min-width: 768px) and (max-width: 1023px) { .related-post .post-list .item { width: 90%; } } @media only screen and (min-width: 0px) and (max-width: 767px) { .related-post .post-list .item { width: 90%; } }
Risques liés au renouvellement d’IPv4 : quand le manque de responsabilisation se transforme en trahison du code en cours d’exécution
La plupart des entreprises entrent sur le marché IPv4 avec un objectif simple. Elles ont besoin d’adresses. Peut-être en ont-elles besoin pour l’hébergement. Peut-être en ont-elles besoin pour une infrastructure VPN. Peut-être en ont-elles besoin pour des services cloud, des plateformes SaaS, l’expansion télécom, des systèmes e-mail, des outils de cybersécurité ou des applications destinées aux clients. Elles recherchent donc un fournisseur IPv4. Elles comparent les prix. Elles vérifientRead more Related Posts 企业入站与出站 IPv4 租赁完整指南 租赁 IPv4 地址可以转移部分伴随完全所有权而来的风险。例如,购买地址可能会让组织暴露于价格波动、长期贬值风险以及信誉管理责任之中。通过 i.Lease 进行租赁,企业可以降低这些风险暴露,并在明确期限内维持可预测的成本,从而支持更可靠的预算规划和风险管理实践。这种方式也简化了基础设施管理,因为租赁供应商通常会负责滥用监控、信誉检查和注册机构协调,使承租方能够专注于核心业务功能,而不是 IP 资产管理。IPv4 租赁并不限于单一行业。托管服务商、云平台、电信公司、SaaS 公司和网络安全企业都可以从租赁中受益。例如,托管服务商可以在无需大量前期投资的情况下扩展服务器部署,而网络安全公司则可以根据客户需求灵活增加地址空间,而无需承诺完全购买。在销售、营销和监管测试中,租赁允许组织在特定地区试运行部署,而无需投入大量资本。这种战略灵活性支持创新,同时帮助企业在 IPv4 稀缺持续存在的市场中保持韧性。利用 i.Lease 进行 IPv4 租赁管理的好处非常清楚:具成本效益的访问、快速部署、信誉安全、可扩展性、地理多样性和持续支持。在 IPv4 地址稀缺且直接购买成本高昂的环境中,通过值得信赖的平台进行租赁,使组织能够维持连接、按需扩展基础设施,并高效管理资源。通过将 IPv4 租赁视为基础设施规划的重要组成部分,而不是临时替代方案,企业可以在应对 IPv4 Risques liés au renouvellement d’IPv4 : quand le manque de responsabilisation se transforme en trahison du code en cours d’exécution La plupart des entreprises entrent sur le marché IPv4 avec un objectif simple. Elles ont besoin d’adresses. Peut-être en ont-elles 大多数企业为何会意外面临 IPv4 地址分配失败的风险 IPv4 稀缺性已被广泛理解。许多企业仍然低估的是:地址资源如何被治理和维护所带来的连续性风险。 企业往往在持续使用 IPv4 资源的同时,并没有完全看清支撑这些分配的连续性条件。 对租赁、转让和供应商管理型基础设施的依赖不断增加,正在将 IPv4地址分配 重塑为一个长期治理问题。 IPv4地址分配已悄然成为连续性问题 对许多企业 IT 团队来说,IPv4 地址看起来仍然在运营上保持稳定。 应用程序仍然可以访问。云平台继续扩展。连接服务供应商在没有明显中断的情况下提供服务。从外部看,互联网似乎仍像过去一样运行。 然而,在这种运营稳定性之下,IPv4地址分配的结构已经发生了根本变化。 可自由分配的 IPv4 空间耗尽早已不是新闻。American Registry for .related-post {} .related-post .post-list { text-align: left; } .related-post .post-list .item { margin: 5px; padding: 10px; } .related-post .headline { font-size: 18px !important; color: #999999 !important; } .related-post .post-list .item .post_thumb { max-height: 220px; margin: 10px 0px; padding: 0px; display: block; } .related-post .post-list .item .post_title { font-size: 16px; color: #3f3f3f; margin: 10px 0px; padding: 0px; display: block; text-decoration: none; } .related-post .post-list .item .post_excerpt { font-size: 13px; color: #3f3f3f; margin: 10px 0px; padding: 0px; display: block; text-decoration: none; } @media only screen and (min-width: 1024px) { .related-post .post-list .item { width: 30%; } } @media only screen and (min-width: 768px) and (max-width: 1023px) { .related-post .post-list .item { width: 90%; } } @media only screen and (min-width: 0px) and (max-width: 767px) { .related-post .post-list .item { width: 90%; } }
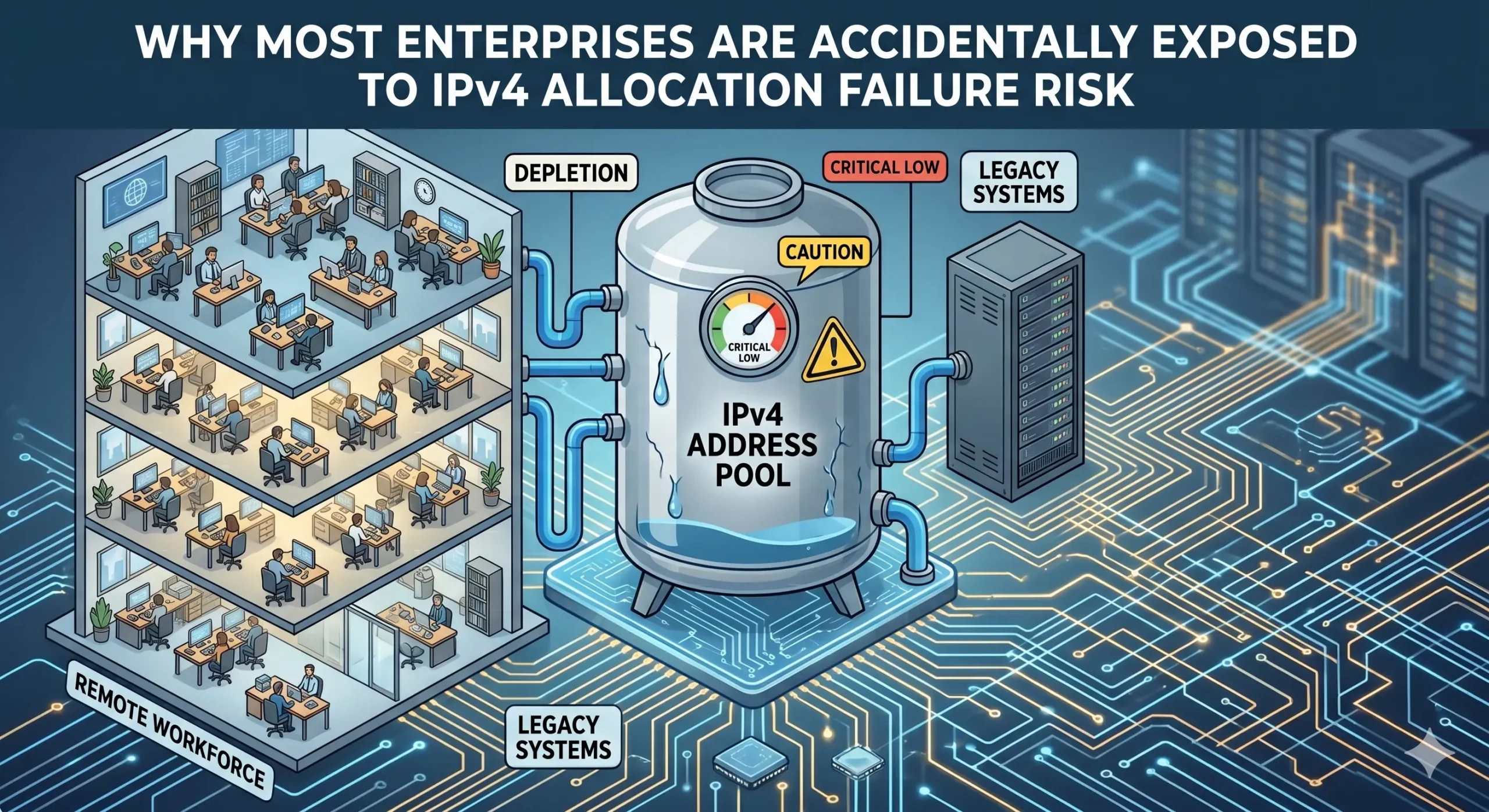
Pourquoi la plupart des entreprises sont exposées accidentellement au risque d’échec d’attribution d’adresse IPv4
La rareté de l’IPv4 est largement comprise. Ce que de nombreuses entreprises sous-estiment encore, c’est le risque de continuité lié à la manière dont les ressources d’adressage sont gouvernées et maintenues. Les entreprises maintiennent souvent une utilisation opérationnelle des ressources IPv4 sans disposer d’une visibilité complète sur les conditions de continuité qui soutiennent ces allocations. La dépendance croissante à la location, aux transferts et aux infrastructures gérées par desRead more Related Posts Primauté du code en cours d’exécution : pourquoi la location d’adresses IPv4 doit être jugée sur la base de preuves opérationnelles La location IPv4 commence souvent par une question simple :Ce fournisseur peut-il nous fournir les adresses ?Mais pour les entreprises Pourquoi la plupart des entreprises sont exposées accidentellement au risque d’échec d’attribution d’adresse IPv4 La rareté de l’IPv4 est largement comprise. Ce que de nombreuses entreprises sous-estiment encore, c’est le risque de continuité lié i.lease 存在的意义:IPv4 连续性并非普通的接入方式 大多数企业进入 IPv4 市场时,目标都很简单。 它们需要地址。 也许是用于托管。 也许是用于 VPN 基础设施。 也许是用于云服务、SaaS 平台、电信扩展、电子邮件系统、网络安全工具,或面向客户的应用程序。 于是,它们开始寻找 IPv4 供应商。 它们比较价格,检查地址块大小,询问交付速度,寻找能够提供所需地址数量的卖方、经纪商或租赁平台。 这种做法可以理解。 但它并不完整。 因为 IPv4 访问不只是供应问题。 它是一个连续性问题。 .related-post {} .related-post .post-list { text-align: left; } .related-post .post-list .item { margin: 5px; padding: 10px; } .related-post .headline { font-size: 18px !important; color: #999999 !important; } .related-post .post-list .item .post_thumb { max-height: 220px; margin: 10px 0px; padding: 0px; display: block; } .related-post .post-list .item .post_title { font-size: 16px; color: #3f3f3f; margin: 10px 0px; padding: 0px; display: block; text-decoration: none; } .related-post .post-list .item .post_excerpt { font-size: 13px; color: #3f3f3f; margin: 10px 0px; padding: 0px; display: block; text-decoration: none; } @media only screen and (min-width: 1024px) { .related-post .post-list .item { width: 30%; } } @media only screen and (min-width: 768px) and (max-width: 1023px) { .related-post .post-list .item { width: 90%; } } @media only screen and (min-width: 0px) and (max-width: 767px) { .related-post .post-list .item { width: 90%; } }
