Comprendre les différents types d’attaques DDoS

Avec l’essor d’Internet dans les opérations commerciales quotidiennes, les menaces de cybersécurité gagnent en complexité et en impact. Parmi les menaces les plus persistantes et destructrices auxquelles les organisations sont confrontées aujourd’hui figurent les attaques par déni de service distribué (DDoS). Ces attaques inondent un système ciblé d’un volume de trafic considérable, rendant les services inaccessibles aux utilisateurs légitimes.
Table of Contents
Pour contrer efficacement les menaces DDoS, il est essentiel de comprendre les différents types d’attaques déployées par les cybercriminels. Chaque type cible une couche spécifique de l’infrastructure réseau ou système, et comprendre leur mode de fonctionnement est la première étape vers l’élaboration d’une stratégie de défense robuste.
Dans cet article, nous explorerons les principaux types d’attaques DDoS, en les classant par catégories et en détaillant comment elles perturbent les services.
1. Attaques basées sur le volume
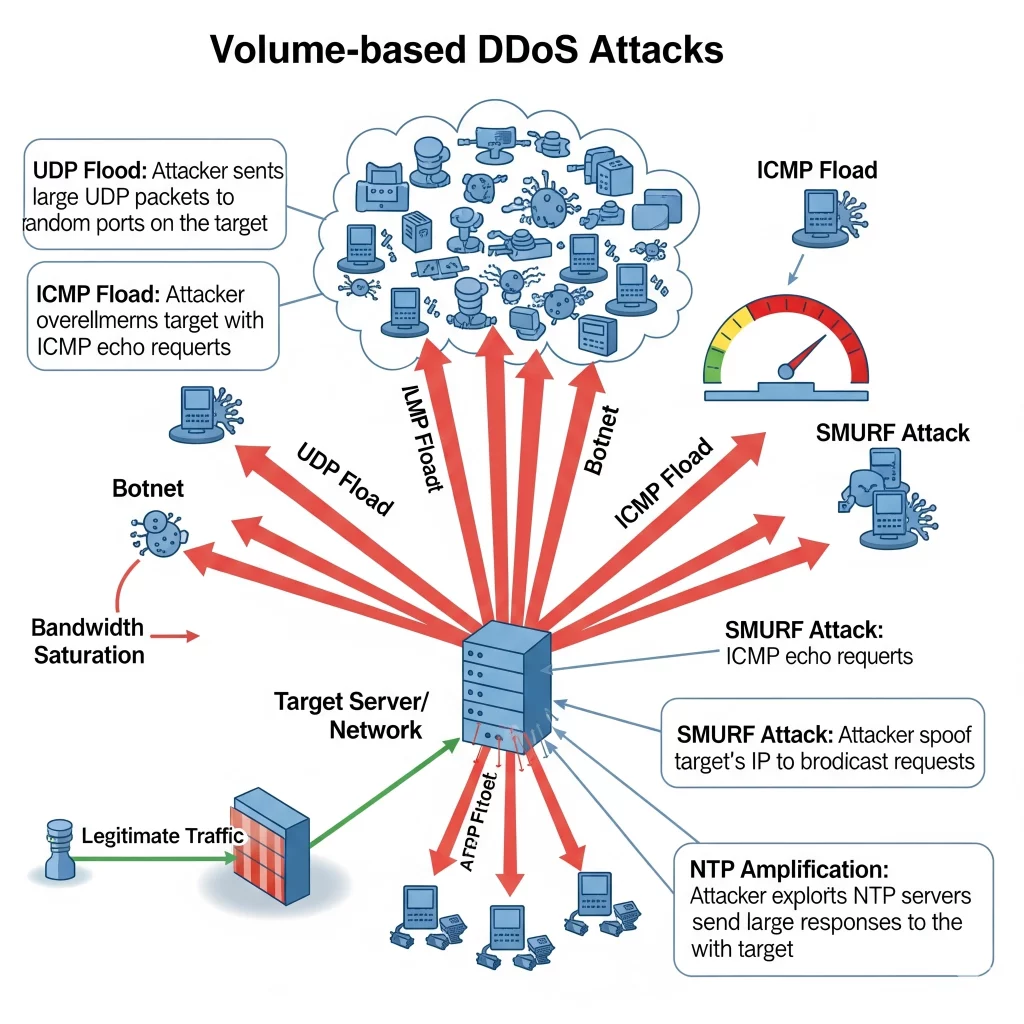
Les attaques DDoS par volume visent à saturer la bande passante du site cible. Ce sont les plus courantes et elles impliquent souvent des botnets envoyant un trafic massif.
Exemples clés :
Inondation UDP : Un grand nombre de paquets UDP sont envoyés à des ports aléatoires de la machine cible, la forçant à répondre en continu.
Inondation ICMP : Cette attaque utilise des requêtes d’écho ICMP (pings) pour saturer la cible, consommant ainsi la bande passante entrante et sortante.
Amplification DNS : Les attaquants usurpent l’adresse IP de la victime et envoient des requêtes DNS à des résolveurs DNS ouverts, qui répondent par une grande quantité de données, amplifiant ainsi le trafic atteignant la cible.
Impact :
Ces attaques sont conçues pour consommer toute la bande passante disponible, rendant la cible inaccessible en épuisant sa capacité.
2. Protocol Attacks
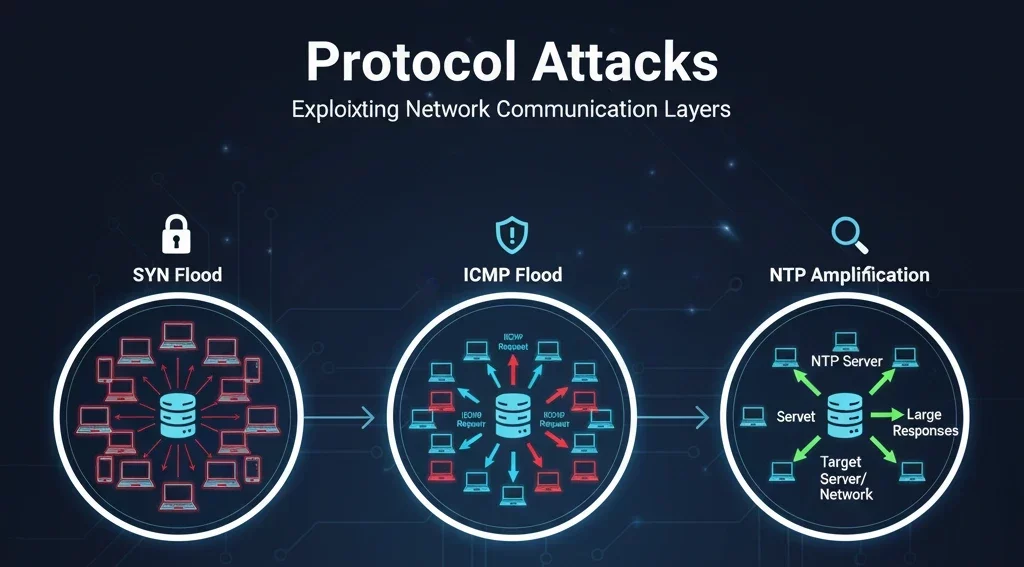
Protocol attacks exploit weaknesses in network layer protocols. These attacks target servers and intermediate resources like firewalls and load balancers.
Key Examples:
- SYN Flood: Exploits the TCP handshake process by sending repeated SYN requests with spoofed IP addresses, never completing the connection.
- Ping of Death: Sends maliciously crafted ping packets that exceed the maximum allowed size, causing systems to crash or reboot.
- Smurf Attack: An attacker sends ICMP requests with a spoofed source address (the victim) to a network’s broadcast address, causing a flood of responses.
Impact:
These attacks consume server resources, and because they target the infrastructure itself, they can be harder to detect and mitigate.
3. Application Layer Attacks
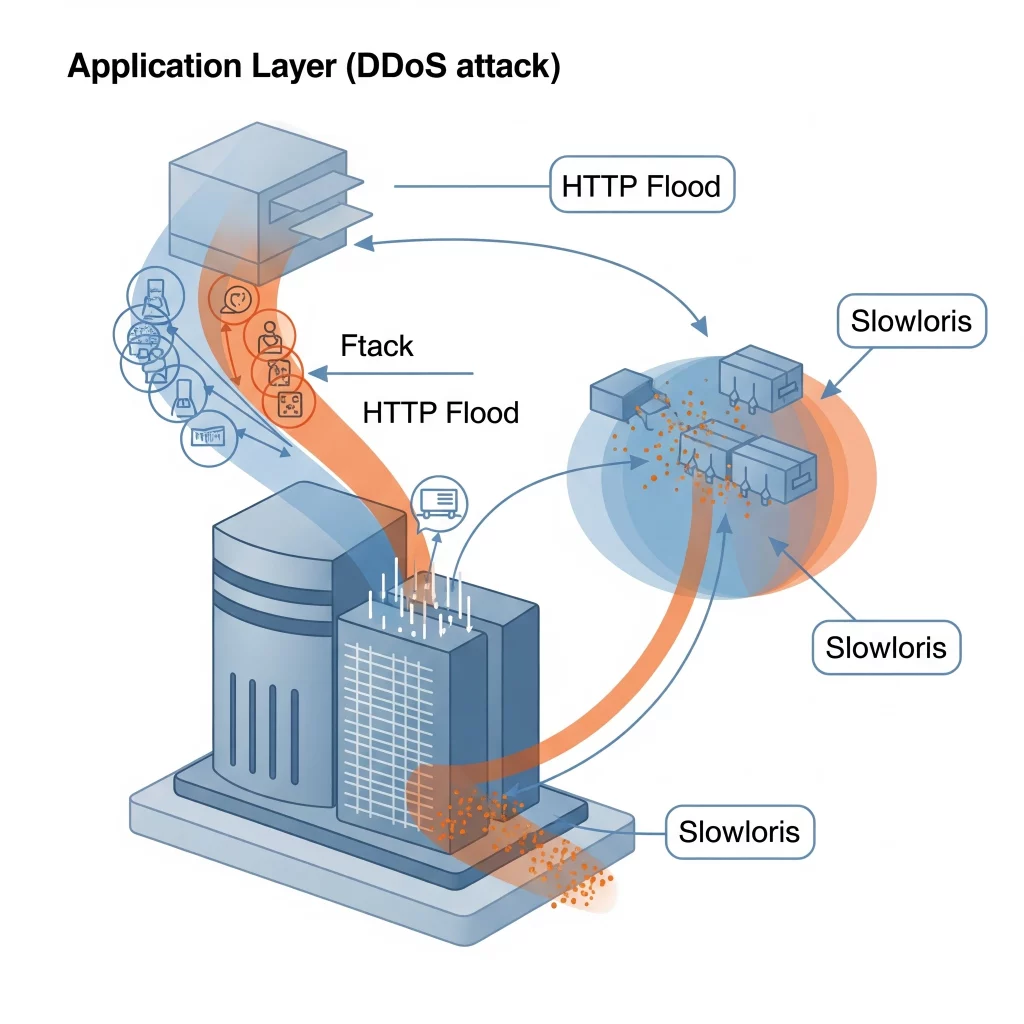
Application layer (Layer 7) attacks mimic legitimate user behavior, making them difficult to distinguish from normal traffic. They target the actual applications, such as web servers.
Key Examples:
- HTTP Flood: Attackers send seemingly legitimate HTTP requests, overwhelming the web server’s capacity to process requests.
- Slowloris: Keeps many connections to the target web server open and holds them open as long as possible by sending partial HTTP requests.
- Zero-day Exploits: These attacks exploit unknown or unpatched vulnerabilities in applications to cause crashes or service interruptions.
Impact:
These attacks are highly stealthy and resource-intensive, aiming to exhaust application resources rather than network bandwidth.
4. Multi-Vector Attacks
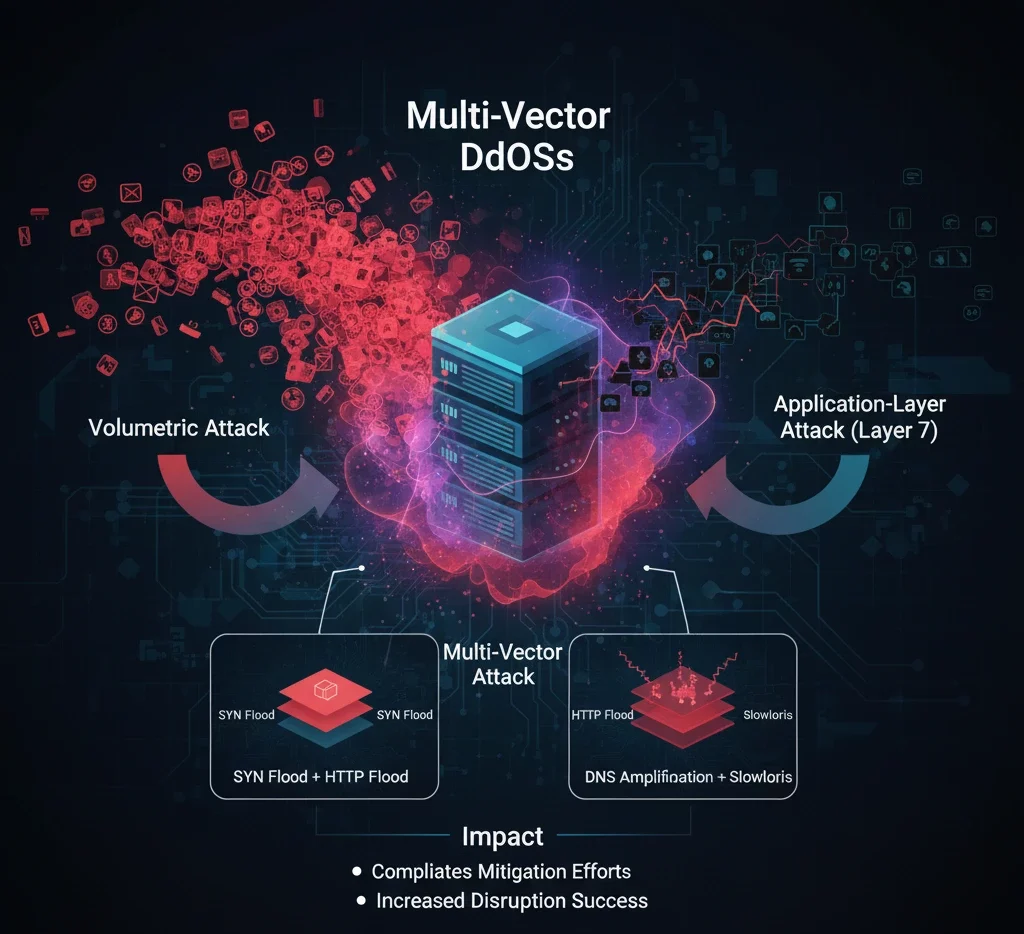
Multi-vector attacks combine two or more different types of DDoS strategies. For example, an attacker might initiate a volumetric attack while simultaneously targeting the application layer.
Key Examples:
- Combining SYN floods with HTTP floods.
- Using DNS amplification in conjunction with Slowloris.
Impact:
By mixing attack types, these methods complicate mitigation efforts and increase the chance of successful disruption.
Pourquoi c'est important
Comprendre ces différentes formes d’attaques DDoS est essentiel pour mettre en œuvre une défense complète. Les organisations doivent déployer des solutions de sécurité multicouches, réaliser régulièrement des évaluations de vulnérabilité et s’assurer que leur infrastructure et leurs applications sont capables de détecter et d’atténuer les activités DDoS.
Outre les pare-feu et les systèmes de prévention d’intrusion classiques, les services de protection contre les attaques DDoS et les outils de surveillance du trafic en temps réel jouent un rôle crucial dans l’identification et la neutralisation des menaces avant qu’elles ne s’aggravent.
Réflexions finales
Les attaques DDoS sont de plus en plus sophistiquées, mais une compréhension approfondie de leur fonctionnement permet aux entreprises de garder une longueur d’avance. Une stratégie de sécurité bien rodée, complétée par des mesures d’atténuation robustes, est essentielle pour protéger votre présence numérique.
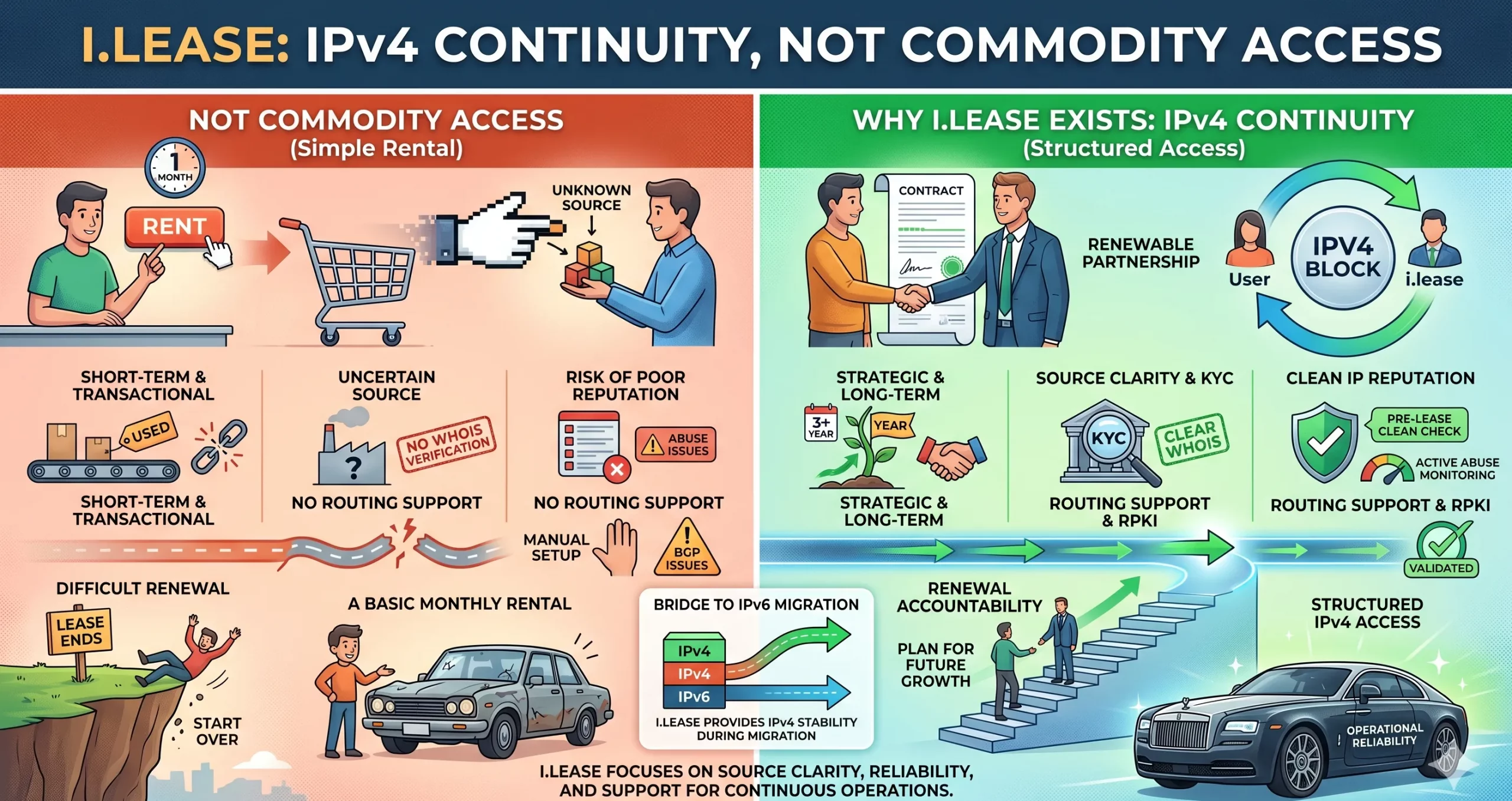
Trusted IPv4 Leasing for Business Growth
Get enterprise-grade IPv4 space quickly, with seamless deployment and end-to-end management.
Get Started with i.leaseRelated Blogs
Articles connexes

Primauté du code en cours d’exécution : pourquoi la location d’adresses IPv4 doit être jugée sur la base de preuves opérationnelles
La location IPv4 commence souvent par une question simple : Ce fournisseur peut-il nous fournir les adresses ? Mais pour les entreprises qui dépendent de l’IPv4 pour l’hébergement, le VPN, le SaaS, le cloud, les télécommunications, la sécurité, la livraison d’e-mails ou les plateformes destinées aux clients, cette question ne suffit pas. Une meilleure question est : Cette structure IPv4 peut-elle prouver qu’elle fonctionne sur le plan opérationnel ? Related Posts La Running-Code Primacy: por qué el arrendamiento de IPv4 debe juzgarse mediante pruebas operativas El arrendamiento de IPv4 suele comenzar con una pregunta simple: ¿Puede este proveedor darnos las direcciones? Pero para las empresas Risques liés au renouvellement d’IPv4 : quand le manque de responsabilisation se transforme en trahison du code en cours d’exécution La plupart des entreprises entrent sur le marché IPv4 avec un objectif simple. Elles ont besoin d’adresses. Peut-être en ont-elles Pourquoi la plupart des entreprises sont exposées accidentellement au risque d’échec d’attribution d’adresse IPv4 La rareté de l’IPv4 est largement comprise. Ce que de nombreuses entreprises sous-estiment encore, c’est le risque de continuité lié .related-post {} .related-post .post-list { text-align: left; } .related-post .post-list .item { margin: 5px; padding: 10px; } .related-post .headline { font-size: 18px !important; color: #999999 !important; } .related-post .post-list .item .post_thumb { max-height: 220px; margin: 10px 0px; padding: 0px; display: block; } .related-post .post-list .item .post_title { font-size: 16px; color: #3f3f3f; margin: 10px 0px; padding: 0px; display: block; text-decoration: none; } .related-post .post-list .item .post_excerpt { font-size: 13px; color: #3f3f3f; margin: 10px 0px; padding: 0px; display: block; text-decoration: none; } @media only screen and (min-width: 1024px) { .related-post .post-list .item { width: 30%; } } @media only screen and (min-width: 768px) and (max-width: 1023px) { .related-post .post-list .item { width: 90%; } } @media only screen and (min-width: 0px) and (max-width: 767px) { .related-post .post-list .item { width: 90%; } }
Risques liés au renouvellement d’IPv4 : quand le manque de responsabilisation se transforme en trahison du code en cours d’exécution
La plupart des entreprises entrent sur le marché IPv4 avec un objectif simple. Elles ont besoin d’adresses. Peut-être en ont-elles besoin pour l’hébergement. Peut-être en ont-elles besoin pour une infrastructure VPN. Peut-être en ont-elles besoin pour des services cloud, des plateformes SaaS, l’expansion télécom, des systèmes e-mail, des outils de cybersécurité ou des applications destinées aux clients. Elles recherchent donc un fournisseur IPv4. Elles comparent les prix. Elles vérifientRead more Related Posts Risk Placement in IPv4 Transactions: What Enterprises Should Know The IPv4 market has quietly evolved into a structured secondary asset class. As global IPv4 exhaustion continues, enterprises, ISPs, and Understanding Operational Risk in IPv4 Address Markets IPv4 has long stopped being a simple technical identifier system. It has become a constrained, priced, and operationally embedded infrastructure Primauté du code en cours d’exécution : pourquoi la location d’adresses IPv4 doit être jugée sur la base de preuves opérationnelles La location IPv4 commence souvent par une question simple :Ce fournisseur peut-il nous fournir les adresses ?Mais pour les entreprises .related-post {} .related-post .post-list { text-align: left; } .related-post .post-list .item { margin: 5px; padding: 10px; } .related-post .headline { font-size: 18px !important; color: #999999 !important; } .related-post .post-list .item .post_thumb { max-height: 220px; margin: 10px 0px; padding: 0px; display: block; } .related-post .post-list .item .post_title { font-size: 16px; color: #3f3f3f; margin: 10px 0px; padding: 0px; display: block; text-decoration: none; } .related-post .post-list .item .post_excerpt { font-size: 13px; color: #3f3f3f; margin: 10px 0px; padding: 0px; display: block; text-decoration: none; } @media only screen and (min-width: 1024px) { .related-post .post-list .item { width: 30%; } } @media only screen and (min-width: 768px) and (max-width: 1023px) { .related-post .post-list .item { width: 90%; } } @media only screen and (min-width: 0px) and (max-width: 767px) { .related-post .post-list .item { width: 90%; } }
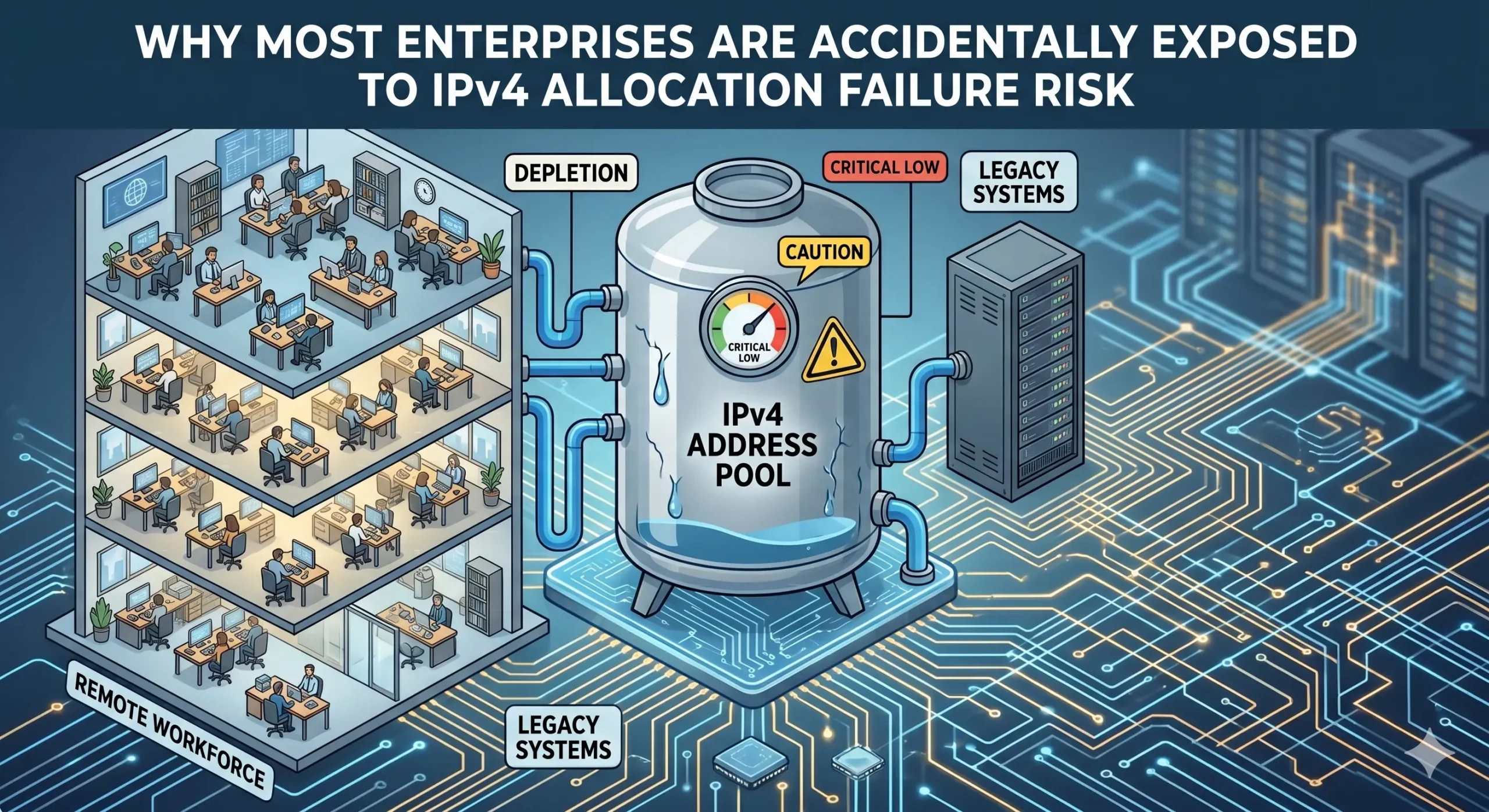
Pourquoi la plupart des entreprises sont exposées accidentellement au risque d’échec d’attribution d’adresse IPv4
La rareté de l’IPv4 est largement comprise. Ce que de nombreuses entreprises sous-estiment encore, c’est le risque de continuité lié à la manière dont les ressources d’adressage sont gouvernées et maintenues. Les entreprises maintiennent souvent une utilisation opérationnelle des ressources IPv4 sans disposer d’une visibilité complète sur les conditions de continuité qui soutiennent ces allocations. La dépendance croissante à la location, aux transferts et aux infrastructures gérées par desRead more Related Posts Risk Placement in IPv4 Transactions: What Enterprises Should Know The IPv4 market has quietly evolved into a structured secondary asset class. As global IPv4 exhaustion continues, enterprises, ISPs, and Understanding Operational Risk in IPv4 Address Markets IPv4 has long stopped being a simple technical identifier system. It has become a constrained, priced, and operationally embedded infrastructure Primauté du code en cours d’exécution : pourquoi la location d’adresses IPv4 doit être jugée sur la base de preuves opérationnelles La location IPv4 commence souvent par une question simple :Ce fournisseur peut-il nous fournir les adresses ?Mais pour les entreprises .related-post {} .related-post .post-list { text-align: left; } .related-post .post-list .item { margin: 5px; padding: 10px; } .related-post .headline { font-size: 18px !important; color: #999999 !important; } .related-post .post-list .item .post_thumb { max-height: 220px; margin: 10px 0px; padding: 0px; display: block; } .related-post .post-list .item .post_title { font-size: 16px; color: #3f3f3f; margin: 10px 0px; padding: 0px; display: block; text-decoration: none; } .related-post .post-list .item .post_excerpt { font-size: 13px; color: #3f3f3f; margin: 10px 0px; padding: 0px; display: block; text-decoration: none; } @media only screen and (min-width: 1024px) { .related-post .post-list .item { width: 30%; } } @media only screen and (min-width: 768px) and (max-width: 1023px) { .related-post .post-list .item { width: 90%; } } @media only screen and (min-width: 0px) and (max-width: 767px) { .related-post .post-list .item { width: 90%; } }
