How IP risk scoring helps prevent cyberattacks and fraud

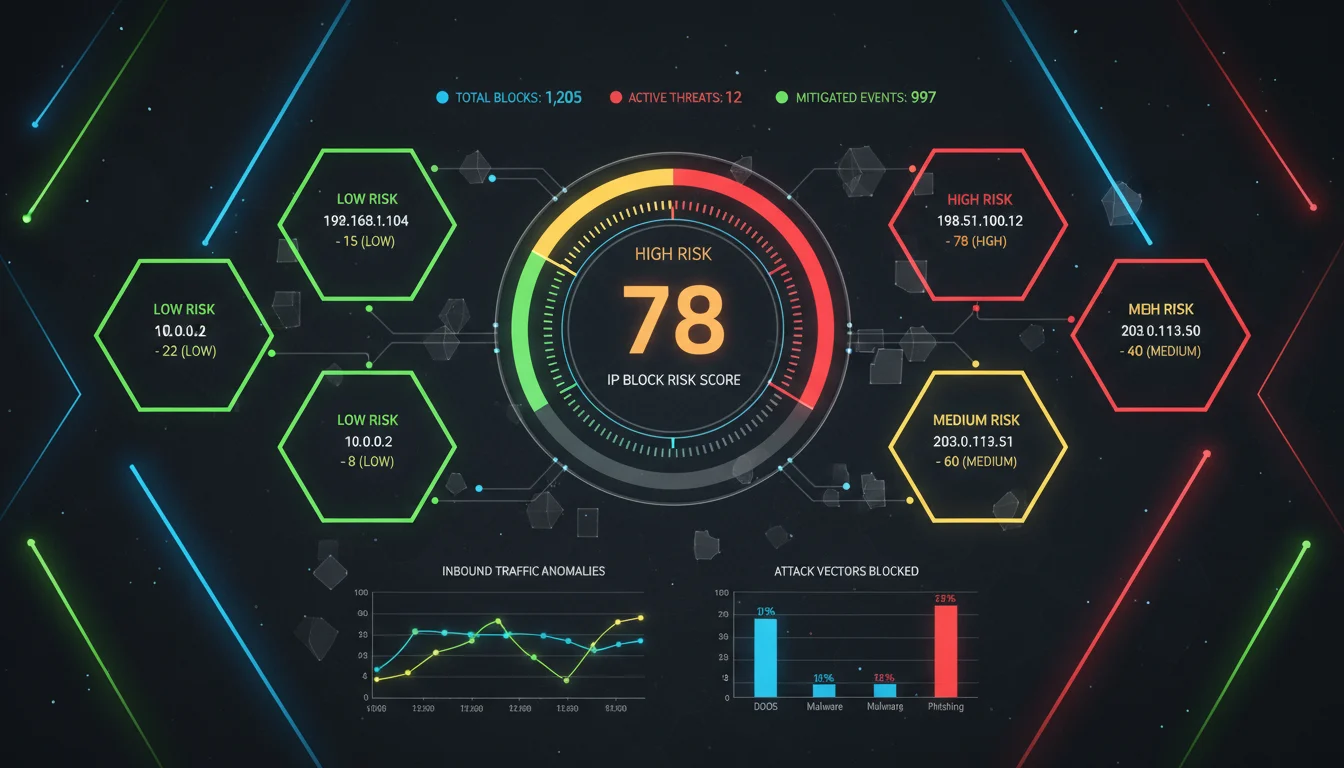
Organisations increasingly rely on IP risk scores. They use them to assess threat levels. They reduce fraud losses. They strengthen cybersecurity defences. IP risk scoring lets firms flag suspicious IP addresses. It does so by analysing usage patterns. It analyses proxies/VPNs. It also analyses historical fraud links. Integrating IP risk scores with transaction workflows enhances threat detection. Integrating with authentication workflows also helps. The detection is real-time. It prevents account takeover and payment fraud.
Table of Contents
What is IP risk scoring
IP risk scoring is a specific method. Each internet protocol (IP) address is assigned a value. The value is numeric or categorical. It reflects the likelihood of malicious behaviour. It also reflects the likelihood of fraudulent behaviour.
Multilogin has provided a definition. “IP Risk Score is a metric used to assess the likelihood that an IP address is associated with malicious activity.” The score often ranges from 0 to 100. Higher values indicate greater risk.
These scores draw on multiple signals. For instance, IPQualityScore (IPQS) offers specific tools. It provides real-time lookup tools. These tools analyse proxies. They analyse VPNs. They analyse known bot traffic. They also analyse connection velocity for each IP.
SEON explains a key function. IP fraud scores detect “risky or fraudulent users. They do so by analysing how users connect online.” The analysis includes proxy use. It includes location mismatches. It also includes historical abuse.
In practice, organisations integrate an IP risk score into specific workflows. The workflows are for fraud prevention. They are for cybersecurity. The integration happens at entry-points. Examples include login, transaction authorisation and account recovery. A high score might trigger additional verification. It might trigger challenge questions. It might trigger access restrictions.
Why IP address risk matters in cyberattacks
IP addresses serve a key role. They are the gateway for devices. They are the gateway for users. Devices and users connect to online systems through them.
Attackers understand this. They often exploit compromised IPs. They exploit proxies. They exploit anonymised networks. The goal is to mask identity. They launch credential-stuffing attacks. They create fake accounts. They initiate fraudulent payments. Scoring IPs for risk changes the defender’s approach. Defenders shift from reactive blocks. They move to proactive screening.
The Canadian Centre for Cyber Security has released a report. It is the National Cyber Threat Assessment 2025-26. The report highlights a trend. Cyber threat actors increasingly use anonymised networks. They use bot infrastructures. They launch large-scale campaigns.
Filtering high-risk IP addresses via scoring is critical. Flagging them is also critical. It helps reduce exposure to these attacks.
How IP risk scoring works in fraud prevention
Effective IP risk scoring systems evaluate various dimensions. These dimensions include:
Anonymity and routing context: VPNs, Tor nodes or data-centre IPs are present. Their presence raises baseline risk. SEON notes a key point. Proxies and VPNs act as “red flags. This happens when someone uses one to buy something on a website.”
Geolocation and velocity checks: IP location changes rapidly. Device and shipping country details mismatch. Time zones are inconsistent. These indicators point to fraud-oriented behaviour.
Historical reputation and abuse: IPs have previous listings on blacklists. They are associated with botnets. They are linked to chargebacks. Such IPs inherit higher risk. Fraudlogix has identified core components. “Database size … data collection … data refresh rates” are critical for accurate IP fraud scores.
Behavioural signals: Mass account creation occurs. Rapid login failures happen. Repeated payment attempts come from the same IP. These patterns further increase risk.
IP risk scoring integrates into digital risk management workflows. A high score can trigger additional controls. These controls include:
Step-up authentication
Manual review
Rate limiting
Outright blocking
This layered approach helps thwart fraudsters. It maintains smoother experiences for legitimate users.
Case examples and industry adoption
IP risk scoring is widely regarded as standard practice. This is true among fraud-prevention platforms. For example, IPQualityScore offers an API. It supports real-time decisioning for high-risk IPs. It enables organisations to “instantly detect high-risk users, bots, proxies and VPNs.”
Fraudlogix emphasises a key issue. Poor data quality undermines risk scoring accuracy. It points to specific needs. Large, high-quality sensor networks are required. Frequent updates are necessary. In e-commerce, payments and fintech sectors, IP screening is vital. It happens at transaction-initiation. It can reduce chargebacks. It can reduce bot-driven fraud.
Benefits of IP risk scores for cyber-defence
IP risk scoring offers several advantages, including pre-emptive threat mitigation where organisations do not wait for malicious behaviour but instead block or challenge suspect connections at entry-points; cost reduction by lowering fraud losses, reducing the need for manual reviews, and improving conversion rates for legitimate users; operational efficiency as automated scoring enables high-volume screening without adding friction for benign traffic; and a holistic security posture by combining with other tools such as device fingerprinting, behavioural analytics, and transaction scoring to add another layer of defence.
A cybersecurity guide has outlined a principle that a “basic risk assessment and management method” starts with identifying existing risks, then assessing their likelihood and impact. Applying IP risk scores aligns neatly with these principles.
Limitations and risks of over-reliance
IP risk scoring is powerful, but it is not a silver bullet, and several caveats apply: false positives may occur when legitimate users appear high risk due to shared network use, VPN privacy services, or dynamic IP assignments, and blocking these users harms user experience; sophisticated actors employ evasion tactics such as residential proxies, device spoofing, and hijacked legitimate IPs to evade detection; collecting and scoring IP data raises concerns, with regulations like GDPR applying, so practices must ensure legality and transparency; and as IPv6 adoption grows and anonymising services proliferate, scoring models must evolve accordingly.
Domain experts emphasise that IP risk scores should be one signal among many. For example, a recent academic study notes that “novel data types” beyond scans—such as technology signatures—can improve the accuracy of cyber-risk assessment.
IP-based indicators are noisy and prone to false positives, so they should be used cautiously as only one component of a broader risk-assessment strategy
-Sarabi, Karir & Liu, “Scoring the Unscorables: Cyber Risk Assessment Beyond Internet Scans.
Integrating IP risk scores into enterprise systems
Organisations seeking to deploy IP risk scoring should follow best practices, including defining clear thresholds and actions by deciding the score ranges for blocking, review, and challenge; testing in low-risk environments by first running scoring in monitoring mode to understand its impact on legitimate users; combining IP scores with other data such as device fingerprinting, behavioural analytics, geolocation, and historical fraud signals; conducting continuous tuning by ensuring the scoring engine refreshes data frequently—something Fraudlogix emphasises the importance of; and maintaining transparency and governance by explaining scoring criteria and ensuring compliance with regulatory frameworks, which is especially important when decisions impact users.

IP risk scoring in emerging threat landscapes
Cyber-threats continue to evolve. IP risk scoring is adapting. The shift towards remote work is ongoing. IoT devices are more prevalent. Cloud-edge architectures are expanding. These trends mean more endpoints. They mean more dynamic IP use. They mean greater complexity.
The National Cyber Threat Assessment 2025-26 highlights a development. Adversaries increasingly embed operations within legitimate cloud infrastructures. They embed within legitimate network infrastructures. This makes IP screening more critical.
Fraud models are evolving beyond traditional payments. They now include account takeover. They include credential abuse, botnets and machine-driven attacks. IP risk scoring plays a dual role. It aids fraud prevention. It underpins broader cyber-resilience.
IP risk scoring is now a core defence layer in an era where threats hide inside trusted infrastructures
—Alex Morgan, Cybersecurity Strategist
The future of IP-based risk scoring
Looking ahead, IP risk scoring will deepen in sophistication with key developments including machine-learning integration where models use multiple signals such as behaviour, fingerprinting and traffic patterns to assign risk dynamically; collaborative intelligence sharing through which organisations may share anonymised IP risk data to refine scoring and improve detection across sectors; expanded coverage of edge and IoT domains as connected devices explode in number, requiring IP risk scoring to cover diverse and transient endpoints; and evolving regulatory frameworks as scoring becomes more integral to access and security decisions, leading to increased legal scrutiny focused on transparency, fairness and bias. Underpinning all of this is a core need: IP risk scores must be explainable, they must be fair, they must integrate into broader defence strategies and they should not be used in isolation, with governance and oversight needing to improve as tools advance
Trusted IPv4 Leasing for Business Growth
Get enterprise-grade IPv4 space quickly, with seamless deployment and end-to-end management.
Get Started with i.leaseFAQs
1. What is an IP risk score?
An IP risk score is a metric. It assesses the likelihood of an IP address being involved in malicious activity. It assesses involvement in fraudulent activity. It evaluates factors such as reputation. It evaluates proxy/VPN use, behaviour and historical abuse.
2. How does IP risk scoring help prevent fraud?
It identifies high-risk IP addresses early. Organisations can challenge suspect connections. They can block suspect connections. This happens during login. It happens during transaction initiation. It happens during account recovery. It reduces fraud losses. It reduces account-takeover risk.
3. Are IP risk scores accurate?
They are a useful tool. They are not perfect. Accuracy depends on data quality. It depends on refresh frequency. It depends on integration with other signals. Fraudlogix notes key factors. “Database size … data refresh rates” matter.
4.Can platforms like i.lease automate risk assessments?
Yes, automation represents a key feature. Blacklist scanning occurs automatically. AI predictions flag potential issues. Clean block swaps happen instantly.
5. What should organisations consider when adopting IP risk scoring?
Important considerations include defining clear actions based on scores. They include combining scoring with other data signals. They include continuously refreshing data. They include ensuring regulatory compliance. They include monitoring impact on legitimate users.
Related Blogs
Artículos relacionados

IPv4 leasing vs purchasing: structural risk in the IPv4 address market
IPv4 leasing vs purchasing reflects a structural shift in IP address markets, balancing cost, control, scarcity, and operational risk in 2026. Key points IPv4 leasing has become a flexible operating model, with stable monthly pricing driven by scarcity and fast deployment needs. IPv4 purchasing is shifting into a long-term asset strategy, but exposed to price cycles, liquidity changes, and capital lock-in. IPv4 is no longer just infrastructure — itRead more Related Posts IPv4 租赁 vs 购买|2026 年 IPv4 市场结构性风险解析 在 IPv4 稀缺持续加剧的市场中,租赁与购买已不只是价格差异,而是两种不同的风险结构。本文解析 IPv4 租赁与购买的成本、控制权、连续性、市场风险与适用场景,帮助企业制定更合适的 IP 策略。 重点摘要 到了 2026 年,IPv4 租赁已经成为一种更灵活的运营模式,月租价格相对稳定,主要由稀缺性和快速部署需求驱动。IPv4 购买则越来越像一种长期资产策略,但也会暴露在价格周期、流动性变化和资金锁定风险之下。 IPv4 已经不只是基础设施,它是一个稀缺市场 IPv4 地址系统已经完全转入二级市场生态。自从 IANA 的免费分配耗尽后,组织现在主要依赖以下方式取得 IPv4:通过区域互联网注册机构(RIR)的转移经纪撮合的二级市场买卖像 Read more IPv4 leasing vs purchasing: structural risk in the IPv4 address market IPv4 leasing vs purchasing reflects a structural shift in IP address markets, balancing cost, control, scarcity, and operational risk in Read more تأجير IPv4 لمراكز البيانات: ما الذي تحتاج إلى معرفته مع تزايد ندرة IPv4، تعتمد مراكز البيانات بشكل متزايد على التأجير لتوسيع البنية التحتية، والتحكم في التكاليف، والحفاظ على اتصال Read more .related-post {} .related-post .post-list { text-align: left; } .related-post .post-list .item { margin: 5px; padding: 10px; } .related-post .headline { font-size: 18px !important; color: #999999 !important; } .related-post .post-list .item .post_thumb { max-height: 220px; margin: 10px 0px; padding: 0px; display: block; } .related-post .post-list .item .post_title { font-size: 16px; color: #3f3f3f; margin: 10px 0px; padding: 0px; display: block; text-decoration: none; } .related-post .post-list .item .post_excerpt { font-size: 13px; color: #3f3f3f; margin: 10px 0px; padding: 0px; display: block; text-decoration: none; } @media only screen and (min-width: 1024px) { .related-post .post-list .item { width: 30%; } } @media only screen and (min-width: 768px) and (max-width: 1023px) { .related-post .post-list .item { width: 90%; } } @media only screen and (min-width: 0px) and (max-width: 767px) { .related-post .post-list .item { width: 90%; } }

IPv4 Leasing for Data Centres: What You Need To Know
As IPv4 scarcity intensifies, data centres increasingly rely on leasing to scale infrastructure, control costs, and maintain reliable connectivity worldwide. IPv4 leasing has become a critical strategy for data centres facing address shortages and rising acquisition costs Leasing offers flexibility and scalability, but introduces risks around reputation, compliance, and long-term dependency Understanding IPv4 and why data centres still depend on it Despite years of tech progress IPv4 is stillRead more Related Posts IPv4 租赁 vs 购买|2026 年 IPv4 市场结构性风险解析 在 IPv4 稀缺持续加剧的市场中,租赁与购买已不只是价格差异,而是两种不同的风险结构。本文解析 IPv4 租赁与购买的成本、控制权、连续性、市场风险与适用场景,帮助企业制定更合适的 IP 策略。 重点摘要 到了 2026 年,IPv4 租赁已经成为一种更灵活的运营模式,月租价格相对稳定,主要由稀缺性和快速部署需求驱动。IPv4 购买则越来越像一种长期资产策略,但也会暴露在价格周期、流动性变化和资金锁定风险之下。 IPv4 已经不只是基础设施,它是一个稀缺市场 IPv4 地址系统已经完全转入二级市场生态。自从 IANA 的免费分配耗尽后,组织现在主要依赖以下方式取得 IPv4:通过区域互联网注册机构(RIR)的转移经纪撮合的二级市场买卖像 Read more IPv4 leasing vs purchasing: structural risk in the IPv4 address market IPv4 leasing vs purchasing reflects a structural shift in IP address markets, balancing cost, control, scarcity, and operational risk in Read more تأجير IPv4 لمراكز البيانات: ما الذي تحتاج إلى معرفته مع تزايد ندرة IPv4، تعتمد مراكز البيانات بشكل متزايد على التأجير لتوسيع البنية التحتية، والتحكم في التكاليف، والحفاظ على اتصال Read more .related-post {} .related-post .post-list { text-align: left; } .related-post .post-list .item { margin: 5px; padding: 10px; } .related-post .headline { font-size: 18px !important; color: #999999 !important; } .related-post .post-list .item .post_thumb { max-height: 220px; margin: 10px 0px; padding: 0px; display: block; } .related-post .post-list .item .post_title { font-size: 16px; color: #3f3f3f; margin: 10px 0px; padding: 0px; display: block; text-decoration: none; } .related-post .post-list .item .post_excerpt { font-size: 13px; color: #3f3f3f; margin: 10px 0px; padding: 0px; display: block; text-decoration: none; } @media only screen and (min-width: 1024px) { .related-post .post-list .item { width: 30%; } } @media only screen and (min-width: 768px) and (max-width: 1023px) { .related-post .post-list .item { width: 90%; } } @media only screen and (min-width: 0px) and (max-width: 767px) { .related-post .post-list .item { width: 90%; } }
What are the risks of buying IPv4 from the wrong source?
Buying IPv4 addresses outside proper IP Allocation channels exposes organisations to fraud, legal disputes, operational failures and long-term governance risks. Key points: Poorly governed IPv4 transactions can fail regional internet registry checks, leading to loss of assets or invalid transfers. Cheap or unverified sources often hide risks including hijacked IP space, blacklisting, and non-compliance with centralized IP allocation policies. Introduction: scarcity fuels risk in the IPv4 market The globalRead more Related Posts IPv4 租赁 vs 购买|2026 年 IPv4 市场结构性风险解析 在 IPv4 稀缺持续加剧的市场中,租赁与购买已不只是价格差异,而是两种不同的风险结构。本文解析 IPv4 租赁与购买的成本、控制权、连续性、市场风险与适用场景,帮助企业制定更合适的 IP 策略。 重点摘要 到了 2026 年,IPv4 租赁已经成为一种更灵活的运营模式,月租价格相对稳定,主要由稀缺性和快速部署需求驱动。IPv4 购买则越来越像一种长期资产策略,但也会暴露在价格周期、流动性变化和资金锁定风险之下。 IPv4 已经不只是基础设施,它是一个稀缺市场 IPv4 地址系统已经完全转入二级市场生态。自从 IANA 的免费分配耗尽后,组织现在主要依赖以下方式取得 IPv4:通过区域互联网注册机构(RIR)的转移经纪撮合的二级市场买卖像 Read more IPv4 leasing vs purchasing: structural risk in the IPv4 address market IPv4 leasing vs purchasing reflects a structural shift in IP address markets, balancing cost, control, scarcity, and operational risk in Read more تأجير IPv4 لمراكز البيانات: ما الذي تحتاج إلى معرفته مع تزايد ندرة IPv4، تعتمد مراكز البيانات بشكل متزايد على التأجير لتوسيع البنية التحتية، والتحكم في التكاليف، والحفاظ على اتصال Read more .related-post {} .related-post .post-list { text-align: left; } .related-post .post-list .item { margin: 5px; padding: 10px; } .related-post .headline { font-size: 18px !important; color: #999999 !important; } .related-post .post-list .item .post_thumb { max-height: 220px; margin: 10px 0px; padding: 0px; display: block; } .related-post .post-list .item .post_title { font-size: 16px; color: #3f3f3f; margin: 10px 0px; padding: 0px; display: block; text-decoration: none; } .related-post .post-list .item .post_excerpt { font-size: 13px; color: #3f3f3f; margin: 10px 0px; padding: 0px; display: block; text-decoration: none; } @media only screen and (min-width: 1024px) { .related-post .post-list .item { width: 30%; } } @media only screen and (min-width: 768px) and (max-width: 1023px) { .related-post .post-list .item { width: 90%; } } @media only screen and (min-width: 0px) and (max-width: 767px) { .related-post .post-list .item { width: 90%; } }
