Understanding IT Infrastructure: The Backbone of Modern Businesses
A robust IT infrastructure is critical for the success of any business in today’s digital age. It forms the foundation on which companies build their day-to-day operations, ensuring everything runs smoothly—from managing internal processes to interacting with customers. But what exactly is IT infrastructure, and why is it so essential?
Table of Contents
This article will walk you through the key elements of IT infrastructure and its importance in the modern business landscape.
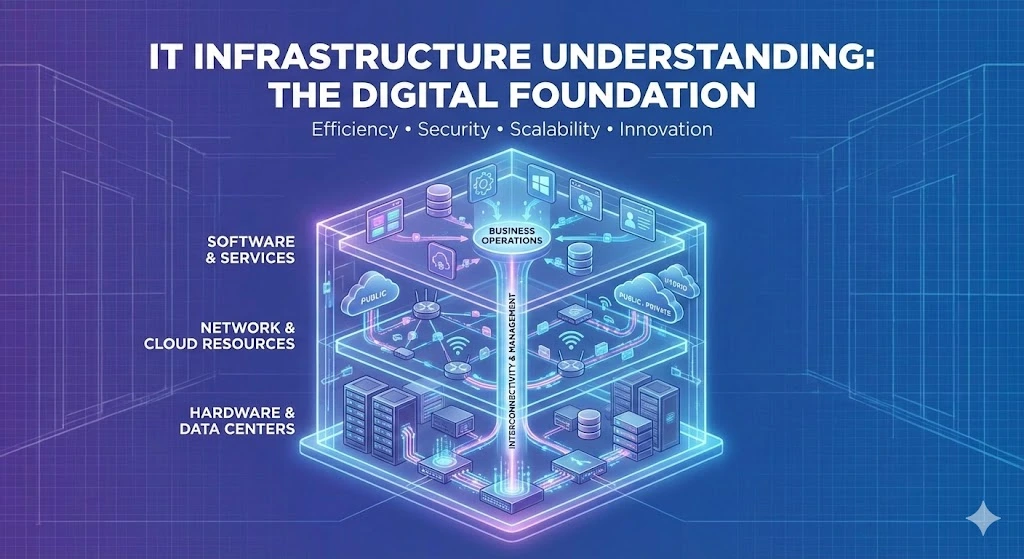
What is IT Infrastructure?
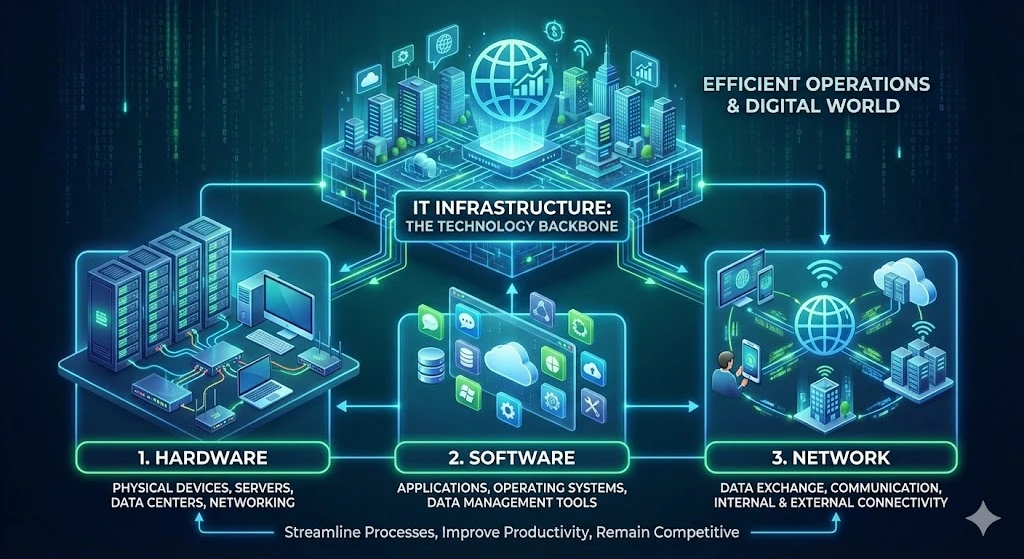
IT infrastructure refers to the collection of hardware, software, networks, and services required for an organization to operate efficiently in the digital world. Essentially, a company’s technology backbone supports all operations, allowing businesses to streamline processes, improve productivity, and remain competitive in a fast-evolving market.
IT infrastructure can be broadly categorized into three components:
1. Hardware: This includes physical devices such as servers, data centers, computers, and networking equipment (routers, switches, etc.) that form the core of IT operations.
2. Software: The applications and operating systems that run on hardware, providing businesses with the tools they need for communication, data management, and other functions.
3. Network: This enables data exchange and communication between devices, systems, and users, both internally and externally.
Key Components of IT Infrastructure
1. Servers:
Servers are the heart of IT infrastructure. They store, process, and manage data, ensuring that employees, systems, and customers can access information quickly and reliably. Businesses may rely on on-premises servers or cloud-based servers, depending on their size and needs.
2. Networking Equipment:
Routers, switches, and firewalls are essential for connecting different devices, systems, and users within an organization. They manage the flow of information and secure networks against cyber threats.
3. Data Storage:
Storing data securely and efficiently is a critical aspect of IT infrastructure. Businesses use storage solutions such as Network Attached Storage (NAS) or cloud storage to ensure that data is always available and protected from potential threats or disasters.
4. Software and Applications:
Operating systems, databases, and specialized applications all contribute to business efficiency. Whether it’s enterprise resource planning (ERP) systems, customer relationship management (CRM) software, or cloud-based collaboration tools, software plays an integral role in business operations.
5. Cloud Infrastructure:
Increasingly, businesses are turning to cloud infrastructure to reduce the cost and complexity of managing physical servers. Cloud computing enables businesses to scale their IT resources on demand and provides flexibility for remote access.
6. Security Systems:
Cybersecurity is a crucial aspect of IT infrastructure. Firewalls, encryption, intrusion detection systems, and antivirus software protect sensitive information from cyberattacks and ensure compliance with data protection regulations.
Why IT Infrastructure Matters for Businesses
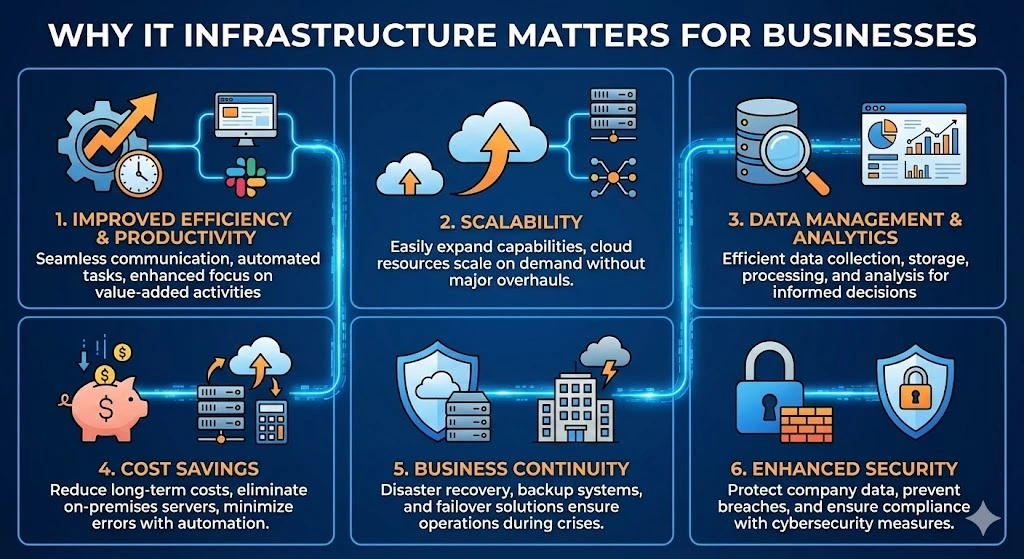
1. Improved Efficiency and Productivity:
A well-designed IT infrastructure ensures seamless communication between systems, automates manual tasks and allows employees to focus on more value-added activities. The integration of advanced software and collaboration tools enhances overall productivity.
2. Scalability:
As businesses grow, their IT needs evolve. A scalable IT infrastructure allows companies to expand their technology capabilities without major overhauls or disruptions. This is particularly important in cloud computing environments, where resources can be quickly scaled up or down based on demand.
3. Data Management and Analytics:
Modern businesses rely heavily on data to make informed decisions. A strong IT infrastructure enables efficient data collection, storage, and processing, providing valuable insights that can drive business strategy. Proper infrastructure also ensures that data remains secure and accessible for analysis.
4. Cost Savings:
By investing in the right infrastructure, businesses can reduce long-term costs. Cloud solutions, for example, eliminate the need for expensive on-premises servers, while automation tools can reduce labor costs and minimize errors.
5. Business Continuity:
A reliable IT infrastructure helps businesses remain operational during crises or unforeseen events. Disaster recovery plans, backup systems, and failover solutions are essential for ensuring business continuity in the face of cyberattacks, hardware failures, or natural disasters.
6. Enhanced Security:
With cyber threats on the rise, protecting company data and customer information is more important than ever. A strong IT infrastructure that incorporates cybersecurity measures helps prevent data breaches and ensures compliance with legal regulations.
Trusted IPv4 Leasing for Business Growth
Get enterprise-grade IPv4 space quickly, with seamless deployment and end-to-end management.
Get Started with i.leaseArticles connexes
Qu’est-ce qu’une adresse IP proxy ?
Une adresse IP proxy est une adresse IP intermédiaire utilisée pour masquer ou relayer votre adresse IP d’origine lors de l’accès à Internet. Elle agit comme une passerelle entre l’utilisateur et le web. Lorsqu’une demande d’accès à un site Web est effectuée, le serveur proxy (qui utilise l’adresse IP proxy) transmet cette demande, cachant ainsi la véritable adresse IP de l’utilisateur au site. Cela permet d’augmenter la confidentialité etRead more Related Posts Why IPv4 scarcity drives economic value for operators Finite IPv4 supply, persistent demand, and slow IPv6 transition are turning IP addresses into tradable assets shaping telecom economics globally. IPv4 Read more What Determines IPv4 Pricing in Today’s Market? Scarcity, shifting demand, and leasing platforms such as i.lease are reshaping how IPv4 addresses are valued and traded globally.IPv4 pricing is driven Read more The future of IPv4 markets Despite IPv6 expansion, scarcity keeps IPv4 valuable, sustaining a global secondary market where addresses increasingly function as tradable digital assets.Finite Read more .related-post {} .related-post .post-list { text-align: left; } .related-post .post-list .item { margin: 5px; padding: 10px; } .related-post .headline { font-size: 18px !important; color: #999999 !important; } .related-post .post-list .item .post_thumb { max-height: 220px; margin: 10px 0px; padding: 0px; display: block; } .related-post .post-list .item .post_title { font-size: 16px; color: #3f3f3f; margin: 10px 0px; padding: 0px; display: block; text-decoration: none; } .related-post .post-list .item .post_excerpt { font-size: 13px; color: #3f3f3f; margin: 10px 0px; padding: 0px; display: block; text-decoration: none; } @media only screen and (min-width: 1024px) { .related-post .post-list .item { width: 30%; } } @media only screen and (min-width: 768px) and (max-width: 1023px) { .related-post .post-list .item { width: 90%; } } @media only screen and (min-width: 0px) and (max-width: 767px) { .related-post .post-list .item { width: 90%; } }
Guide complet du marché des adresses IP
Les adresses IP sont essentielles pour identifier les appareils et permettre la communication entre les réseaux. Avec l’expansion continue d’Internet, la demande d’adresses IP a considérablement augmenté, entraînant l’essor du marché des adresses IP. Ce marché unique permet aux entreprises et aux particuliers d’acheter, de vendre ou de louer des adresses IP, assurant ainsi une utilisation optimale des ressources dans un monde où les adresses IPv4 deviennent rares. Qu’est-ceRead more Related Posts Why IPv4 scarcity drives economic value for operators Finite IPv4 supply, persistent demand, and slow IPv6 transition are turning IP addresses into tradable assets shaping telecom economics globally. IPv4 Read more What Determines IPv4 Pricing in Today’s Market? Scarcity, shifting demand, and leasing platforms such as i.lease are reshaping how IPv4 addresses are valued and traded globally.IPv4 pricing is driven Read more The future of IPv4 markets Despite IPv6 expansion, scarcity keeps IPv4 valuable, sustaining a global secondary market where addresses increasingly function as tradable digital assets.Finite Read more .related-post {} .related-post .post-list { text-align: left; } .related-post .post-list .item { margin: 5px; padding: 10px; } .related-post .headline { font-size: 18px !important; color: #999999 !important; } .related-post .post-list .item .post_thumb { max-height: 220px; margin: 10px 0px; padding: 0px; display: block; } .related-post .post-list .item .post_title { font-size: 16px; color: #3f3f3f; margin: 10px 0px; padding: 0px; display: block; text-decoration: none; } .related-post .post-list .item .post_excerpt { font-size: 13px; color: #3f3f3f; margin: 10px 0px; padding: 0px; display: block; text-decoration: none; } @media only screen and (min-width: 1024px) { .related-post .post-list .item { width: 30%; } } @media only screen and (min-width: 768px) and (max-width: 1023px) { .related-post .post-list .item { width: 90%; } } @media only screen and (min-width: 0px) and (max-width: 767px) { .related-post .post-list .item { width: 90%; } }
Qu’est-ce que SSH ? | Protocole Secure Shell (SSH)
Sécuriser les communications entre appareils est essentiel, surtout lors de la gestion de systèmes distants. L’un des protocoles les plus largement utilisés et fiables pour un accès distant sécurisé est SSH (Secure Shell). Cet article explore ce qu’est SSH, comment il fonctionne et pourquoi il est crucial pour la sécurité des réseaux. Qu’est-ce que SSH ? SSH (Secure Shell) est un protocole réseau qui permet aux utilisateurs d’accéder etRead more Related Posts Qu’est-ce qu’une adresse IP proxy ? Une adresse IP proxy est une adresse IP intermédiaire utilisée pour masquer ou relayer votre adresse IP d'origine lors de Read more Guide complet du marché des adresses IP Les adresses IP sont essentielles pour identifier les appareils et permettre la communication entre les réseaux. Avec l'expansion continue d'Internet, Read more ما هو SSH؟ | بروتوكول القشرة الآمنة (SSH) يعد تأمين الاتصالات بين الأجهزة أمراً مهماً، خاصة عند إدارة الأنظمة البعيدة. أحد البروتوكولات الأكثر استخدامًا وموثوقية للوصول الآمن عن Read more .related-post {} .related-post .post-list { text-align: left; } .related-post .post-list .item { margin: 5px; padding: 10px; } .related-post .headline { font-size: 18px !important; color: #999999 !important; } .related-post .post-list .item .post_thumb { max-height: 220px; margin: 10px 0px; padding: 0px; display: block; } .related-post .post-list .item .post_title { font-size: 16px; color: #3f3f3f; margin: 10px 0px; padding: 0px; display: block; text-decoration: none; } .related-post .post-list .item .post_excerpt { font-size: 13px; color: #3f3f3f; margin: 10px 0px; padding: 0px; display: block; text-decoration: none; } @media only screen and (min-width: 1024px) { .related-post .post-list .item { width: 30%; } } @media only screen and (min-width: 768px) and (max-width: 1023px) { .related-post .post-list .item { width: 90%; } } @media only screen and (min-width: 0px) and (max-width: 767px) { .related-post .post-list .item { width: 90%; } }