Les défis de l’adoption d’IPv6 : solutions pour une transition sans heurts
Dans le paysage en évolution rapide de la technologie Internet, la transition de l’IPv4 à l’IPv6 est devenue une préoccupation de plus en plus pressante pour les organisations du monde entier. Bien que l’IPv6 offre de nombreux avantages par rapport à son prédécesseur, notamment un espace d’adressage considérablement élargi et des fonctions de sécurité améliorées, son adoption présente des défis et des complexités uniques. Dans cet article, nous allons explorer les principaux défis associés à l’adoption d’IPv6 et fournir des solutions pratiques pour les surmonter.
Table of Contents
Comprendre les cinq (5) défis de l’adoption d’IPv6 :
Épuisement des adresses IPv4
L’un des principaux moteurs de la transition vers l’IPv6 est l’épuisement imminent des adresses IPv4 disponibles. Avec la prolifération des appareils connectés à l’internet et la demande croissante d’adresses IP, l’espace d’adressage limité de l’IPv4 est de plus en plus sollicité, ce qui rend nécessaire l’adoption de l’IPv6 pour faire face à la croissance future.
Compatibilité de l’infrastructure existante
De nombreuses organisations s’appuient sur des infrastructures de réseau et des applications héritées qui ne sont pas intrinsèquement compatibles avec l’IPv6. La migration de ces systèmes vers IPv6 peut être un processus complexe et fastidieux, nécessitant des tests approfondis et des mises à niveau ou des remplacements potentiellement coûteux.
Manque de sensibilisation et de formation
Malgré l’importance de l’adoption de l’IPv6, de nombreux professionnels de l’informatique et organisations n’ont pas conscience de ses avantages et de ses subtilités techniques. Le manque de formation et d’expertise dans la mise en œuvre d’IPv6 peut entraver les efforts d’adoption et contribuer à la résistance ou au scepticisme des parties prenantes.
Problèmes de sécurité
Bien que l’IPv6 offre des fonctions de sécurité intégrées telles que l’intégration IPSec et l’autoconfiguration des adresses, son adoption peut introduire de nouveaux risques et de nouvelles vulnérabilités en matière de sécurité si elle n’est pas correctement gérée. Les organisations doivent mettre en œuvre des mesures et des protocoles de sécurité robustes pour atténuer les risques potentiels associés au déploiement de l’IPv6.
Performance et optimisation du réseau :
La transition vers IPv6 peut avoir un impact sur les performances et l’efficacité du réseau, en particulier pendant la période de coexistence où les protocoles IPv4 et IPv6 sont tous deux utilisés. Une planification adéquate et des stratégies d’optimisation sont essentielles pour minimiser les perturbations et garantir des performances optimales tout au long du processus de transition.
Stratégies pour surmonter les difficultés liées à l’adoption d’IPv6
Élaborer un plan d’adoption complet
Commencez par procéder à une évaluation approfondie de l’infrastructure réseau, des applications et des ressources actuelles de votre organisation. Élaborez un plan d’adoption détaillé décrivant les objectifs, les délais et les étapes de la migration vers IPv6.
Investir dans la formation et l’éducation à l’IPv6.
Proposez une formation complète à votre personnel informatique et aux parties prenantes afin de les sensibiliser à la technologie IPv6 et à sa mise en œuvre, et de les aider à mieux la comprendre. Encouragez l’apprentissage continu et le développement des compétences pour assurer une transition en douceur. Pour la formation à l’IPv6, contactez-nous pour en savoir plus !
Tester et valider la compatibilité
Avant le déploiement, effectuez des tests rigoureux et validez la compatibilité d’IPv6 avec les systèmes, les applications et les appareils existants. Identifiez et résolvez tout problème de compatibilité ou d’interopérabilité afin de minimiser les perturbations pendant le processus de transition.
Mettre en œuvre les meilleures pratiques en matière de sécurité
Donner la priorité à la sécurité tout au long du processus d’adoption de l’IPv6 en mettant en œuvre les meilleures pratiques telles que la segmentation du réseau, les contrôles d’accès, le cryptage et les systèmes de détection d’intrusion. Rester informé des menaces et vulnérabilités émergentes liées à l’IPv6 et les traiter de manière proactive pour atténuer les risques.
Collaborer avec les partenaires industriels
S’engager avec les partenaires industriels, les vendeurs et les fournisseurs de services pour tirer parti de leur expertise et de leurs ressources dans l’adoption de l’IPv6. Collaborez aux tests d’interopérabilité, partagez les meilleures pratiques et demandez conseil à des professionnels expérimentés dans le domaine des adresses IP, comme les responsables de Larus, pour faciliter une transition réussie.
L’adoption de l’IPv6 en quelques mots
Bien que l’adoption de l’IPv6 présente de nombreux défis, une planification proactive, l’éducation et la collaboration peuvent aider les organisations à surmonter ces obstacles et à récolter les bénéfices d’une infrastructure Internet moderne, évolutive et sécurisée. En relevant les principaux défis et en mettant en œuvre les meilleures pratiques, les organisations peuvent aborder le passage à l’IPv6 en toute confiance et assurer une transition sans heurts vers la prochaine génération de technologie internet.
Articles connexes
Comment obtenir une adresse IPv4
Related Posts Comment obtenir une adresse IPv4 Chiffrement IP vs HTTPS : quelle est la différence ? 2025年IPv4需求量最高的5个国家 Standfirst — 由于 IPv4 地址仍然稀缺,一些国家对传统 IP 地址的需求尤为强劲。了解这些国家的需求有助于指导租赁或收购策略。美国、中国、日本、德国和英国是 IPv4 地址需求量最大的国家,这既反映了传统地址的分配现状,也反映了支持纯 IPv4 服务的持续压力。对于使用 i.Lease 的组织而言,重点关注这些高需求市场至关重要——竞争异常激烈,但干净且符合规范的 IPv4 地址空间也价值连城。 “IPv4需求”的含义——以及它为何重要 当我们谈论“IPv4 需求”时,我们指的是有限 IPv4 地址池所承受的压力——有多少组织、数据中心和 Read more Related Posts 如何获取 IPv4 地址 IP加密与HTTPS:有什么区别? Les 5 pays présentant la plus forte demande d’IPv4 en 2025 Standfirst — Face à la rareté persistante des adresses IPv4, certains pays affichent une demande particulièrement forte pour les ressources Read more .related-post {} .related-post .post-list { text-align: left; } .related-post .post-list .item { margin: 5px; padding: 10px; } .related-post .headline { font-size: 18px !important; color: #999999 !important; } .related-post .post-list .item .post_thumb { max-height: 220px; margin: 10px 0px; padding: 0px; display: block; } .related-post .post-list .item .post_title { font-size: 16px; color: #3f3f3f; margin: 10px 0px; padding: 0px; display: block; text-decoration: none; } .related-post .post-list .item .post_excerpt { font-size: 13px; color: #3f3f3f; margin: 10px 0px; padding: 0px; display: block; text-decoration: none; } @media only screen and (min-width: 1024px) { .related-post .post-list .item { width: 30%; } } @media only screen and (min-width: 768px) and (max-width: 1023px) { .related-post .post-list .item { width: 90%; } } @media only screen and (min-width: 0px) and (max-width: 767px) { .related-post .post-list .item { width: 90%; } }
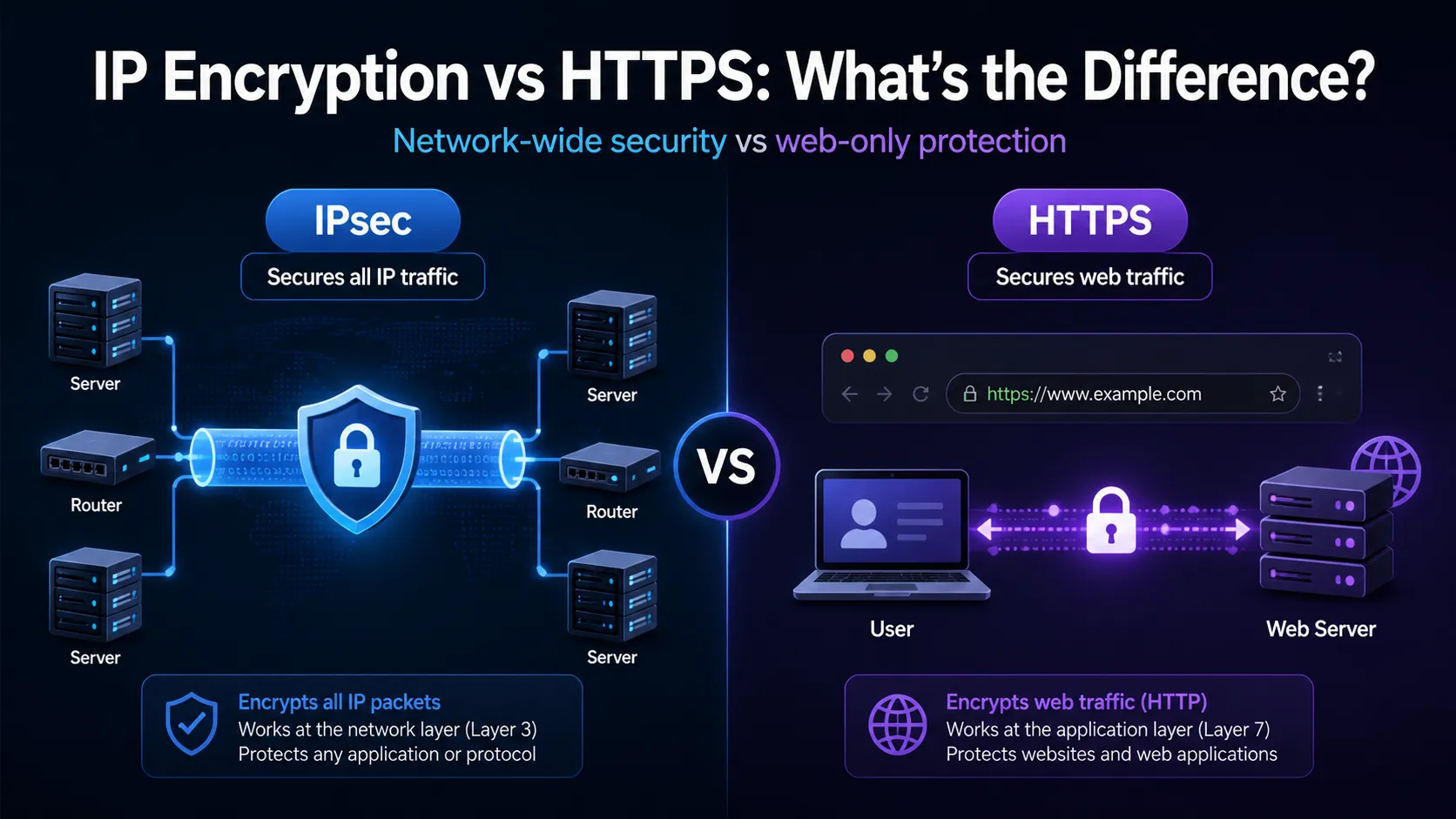
Chiffrement IP vs HTTPS : quelle est la différence ?
Related Posts Comment obtenir une adresse IPv4 Chiffrement IP vs HTTPS : quelle est la différence ? 2025年IPv4需求量最高的5个国家 Standfirst — 由于 IPv4 地址仍然稀缺,一些国家对传统 IP 地址的需求尤为强劲。了解这些国家的需求有助于指导租赁或收购策略。美国、中国、日本、德国和英国是 IPv4 地址需求量最大的国家,这既反映了传统地址的分配现状,也反映了支持纯 IPv4 服务的持续压力。对于使用 i.Lease 的组织而言,重点关注这些高需求市场至关重要——竞争异常激烈,但干净且符合规范的 IPv4 地址空间也价值连城。 “IPv4需求”的含义——以及它为何重要 当我们谈论“IPv4 需求”时,我们指的是有限 IPv4 地址池所承受的压力——有多少组织、数据中心和 Read more Related Posts 如何获取 IPv4 地址 IP加密与HTTPS:有什么区别? Les 5 pays présentant la plus forte demande d’IPv4 en 2025 Standfirst — Face à la rareté persistante des adresses IPv4, certains pays affichent une demande particulièrement forte pour les ressources Read more .related-post {} .related-post .post-list { text-align: left; } .related-post .post-list .item { margin: 5px; padding: 10px; } .related-post .headline { font-size: 18px !important; color: #999999 !important; } .related-post .post-list .item .post_thumb { max-height: 220px; margin: 10px 0px; padding: 0px; display: block; } .related-post .post-list .item .post_title { font-size: 16px; color: #3f3f3f; margin: 10px 0px; padding: 0px; display: block; text-decoration: none; } .related-post .post-list .item .post_excerpt { font-size: 13px; color: #3f3f3f; margin: 10px 0px; padding: 0px; display: block; text-decoration: none; } @media only screen and (min-width: 1024px) { .related-post .post-list .item { width: 30%; } } @media only screen and (min-width: 768px) and (max-width: 1023px) { .related-post .post-list .item { width: 90%; } } @media only screen and (min-width: 0px) and (max-width: 767px) { .related-post .post-list .item { width: 90%; } }

Les 5 pays présentant la plus forte demande d’IPv4 en 2025
Standfirst — Face à la rareté persistante des adresses IPv4, certains pays affichent une demande particulièrement forte pour les ressources IP existantes. Identifier ces pays permet d’orienter les stratégies de location ou d’acquisition. Les États-Unis, la Chine, le Japon, l’Allemagne et le Royaume-Uni sont les principaux pays demandeurs d’IPv4, ce qui reflète à la fois les attributions existantes et la pression constante pour la prise en charge des servicesRead more Related Posts 如何获取 IPv4 地址 IP加密与HTTPS:有什么区别? Les 5 pays présentant la plus forte demande d’IPv4 en 2025 Standfirst — Face à la rareté persistante des adresses IPv4, certains pays affichent une demande particulièrement forte pour les ressources Read more .related-post {} .related-post .post-list { text-align: left; } .related-post .post-list .item { margin: 5px; padding: 10px; } .related-post .headline { font-size: 18px !important; color: #999999 !important; } .related-post .post-list .item .post_thumb { max-height: 220px; margin: 10px 0px; padding: 0px; display: block; } .related-post .post-list .item .post_title { font-size: 16px; color: #3f3f3f; margin: 10px 0px; padding: 0px; display: block; text-decoration: none; } .related-post .post-list .item .post_excerpt { font-size: 13px; color: #3f3f3f; margin: 10px 0px; padding: 0px; display: block; text-decoration: none; } @media only screen and (min-width: 1024px) { .related-post .post-list .item { width: 30%; } } @media only screen and (min-width: 768px) and (max-width: 1023px) { .related-post .post-list .item { width: 90%; } } @media only screen and (min-width: 0px) and (max-width: 767px) { .related-post .post-list .item { width: 90%; } }
