IP Encryption vs HTTPS: What’s the Difference?
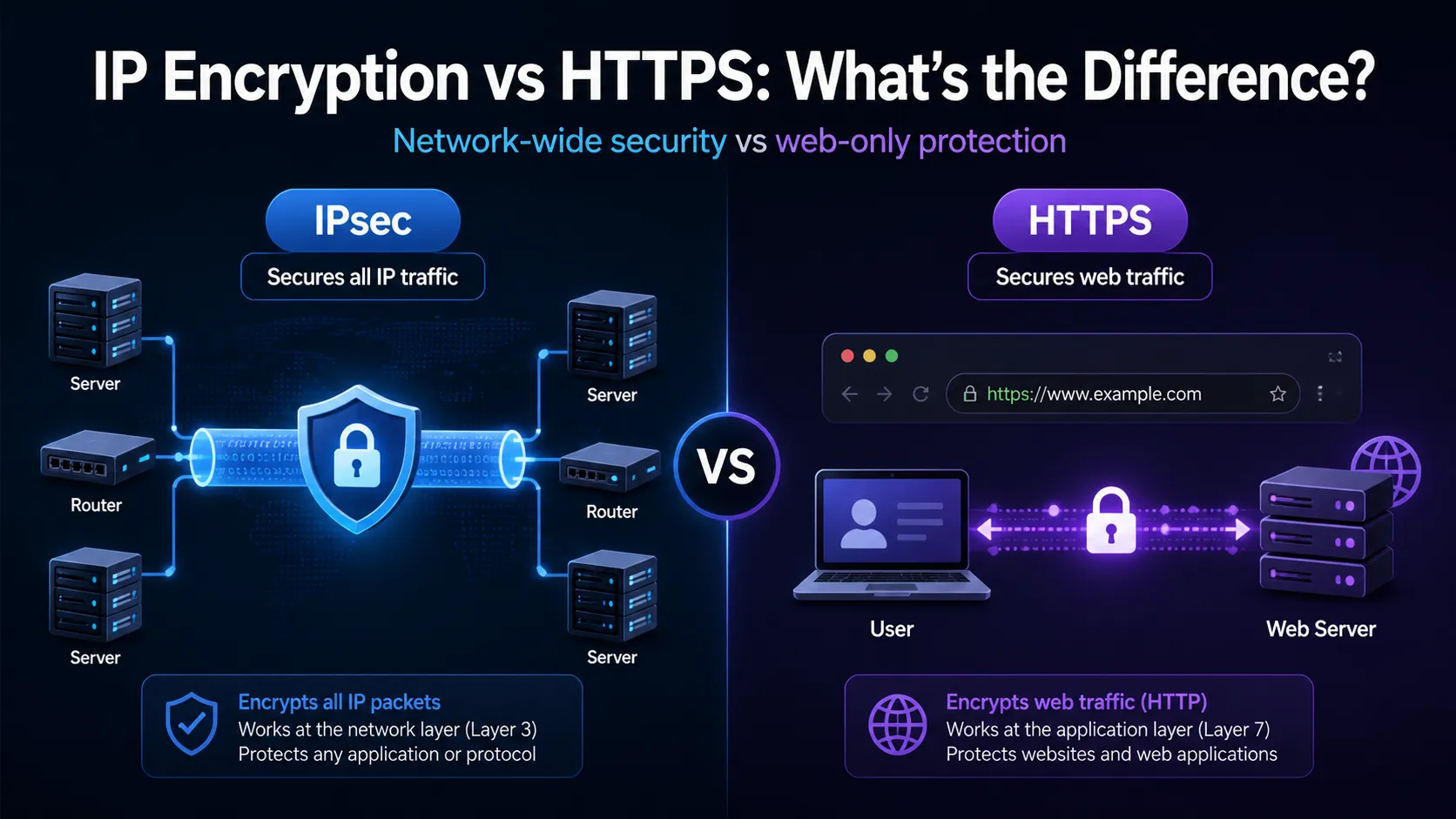
Table of Contents
Explore the distinctions between IP‑layer encryption (IPsec) and HTTPS, their use cases, performance trade‑offs and overlapping functionalities.
- IPsec secures all IP traffic at the network layer, while HTTPS protects web‑specific traffic at the application layer.
- Both offer powerful encryption, but their scope, complexity and deployment models are quite different.
Introduction
In today’s digital world, encryption is no longer a choice. It is something everyone needs. People and businesses now use the internet for many things, such as banking, medical records, cloud storage, and smart devices. Because of this, keeping data safe while it moves across the internet is very important. There are two common ways to protect internet traffic.
One is IP-layer encryption, often done using IPsec. The other is HTTPS, which protects web traffic. Both use strong methods to hide data and keep it safe. But they work in different places and in different ways. IPsec works at the network layer. It protects all data that moves over the internet, no matter what program sends it. HTTPS works at the application layer. It protects only web traffic, like websites or online forms.
Each method has things it does well and things it does not. Each is better in different situations. Knowing the difference between IPsec and HTTPS is important. It helps network engineers and system administrators make good choices. It also helps people who plan cloud services, VPNs, or website security pick the right tool.
What is IP encryption? An overview of IPsec
IPsec—short for Internet Protocol Security—is a suite of protocols defined by the IETF in the 1990s. Its primary purpose is to encrypt and authenticate IP packets, providing confidentiality, data origin authentication, integrity, and protection from replay attacks.
IPsec operates at the network layer (OSI Layer 3) and supports two main modes: Transport mode and Tunnel mode. It’s widely used for establishing VPNs, connecting remote networks, or encrypting host-to-host traffic.
What is HTTPS?
HTTPS (Hypertext Transfer Protocol Secure) is HTTP with TLS (Transport Layer Security) added. It is made to protect web traffic. TLS gives encryption, checks identity, and keeps the data safe. It stops others from seeing or changing the data while it moves between a user’s browser and a web server.
HTTPS works at the application layer (OSI Layer 7). It protects HTTP requests and responses. It also checks the web server’s identity using X.509 certificates. These certificates come from trusted Certificate Authorities (CAs). They help users know they are talking to the real website.
Network-wide vs web-only
IPsec works at the network layer. It can protect all IP-based communication, no matter what application or protocol is used. This makes it useful for site-to-site VPNs that connect full networks. It also works for client-to-site VPNs, where remote users safely reach internal tools like file servers, email systems, or voice services.
HTTPS works only at the application layer. It protects traffic that uses HTTP. It is good for online tasks like banking, shopping, webmail, and APIs. But it does not protect other types of traffic. This includes things like DNS lookups, file transfers over FTP, or voice calls that use SIP.
IPsec covers more kinds of traffic and works more widely. HTTPS only protects web traffic. But it is simpler to use and easy to set up. Most web servers and browsers already support it. Many websites use HTTPS to make sure user data is safe when sent over the internet.
Deployment and complexity
Establishing IPsec has very high technical requirements. It needs to configure the tunnel endpoints, establish a security alliance (sa) through protocols such as IKE/IKEv2, and manage encryption keys or digital certificates. Deployment usually involves the coordination between network devices and firewall rules, and sometimes also involves custom client software, especially in enterprise or cross-organizational environments.
In contrast, HTTPS is easier to implement. Website administrators usually only need to obtain an SSL/TLS certificate, configure a web server (such as Apache or Nginx), and enable HTTPS support. Tools like Let’s Encrypt further simplify the process by automating certificate issuance and renewal, allowing even small websites or personal projects to access secure network communications.
Performance considerations
IPsec encrypts the entire IP packet, including the header (in tunnel mode), which may lead to an increase in packet size and potential issues with MTU (Maximum Transmission Unit), resulting in fragmentation and higher latency. The negotiation process for establishing a secure connection (for example, through IKE) also introduces additional setup time, especially in dynamic or mobile environments.
On the other hand, HTTPS benefits from modern TLS optimizations such as session recovery, zero round-trip time (0-RTT) in TLS 1.3, and performance improvements in HTTP/2 and HTTP/3, including multiplexing and header compression. These enhancements enable HTTPS to provide strong security with minimal impact on speed, making it highly efficient for web applications.
Security and trust models
IPsec relies on peer-to-peer authentication and typically uses pre-shared keys or X.509 certificates exchanged between devices. Trust is established privately, which means that both ends must be manually configured or managed through an internal key infrastructure. This model works well in closed environments such as enterprise networks, but has poor scalability in public-facing services.
On the contrary, HTTPS relies on a global certificate authority (ca) system to verify the identity of web servers. The browser is pre-installed with a list of trusted cas, allowing users to automatically trust HTTPS connections without manual Settings. This public trust model supports large-scale secure communication on the open Internet, but it also introduces risks such as CA leakage or incorrect certificate issuance – these risks are mitigated through mechanisms such as certificate transparency and OCSP binding.
Use cases: when to choose which?
When it is necessary to ensure the security of all traffic in the network, IPsec can be chosen. For example, site-to-site vpn for connecting branch offices, or client-to-site vpn for remote workers accessing internal systems. This is particularly valuable when multiple applications and protocols (such as file sharing, VoIP, and internal services) require encryption without the need for separate modifications.
When you are concerned about web-based communication (such as protecting websites, REST apis or user portals), please choose HTTPS. It is highly suitable for protecting sensitive user data, such as login credentials, payment information and form submissions. For most public-facing applications, HTTPS offers the simplest and most reliable encryption solution.
Do they overlap?
IPsec and HTTPS can work simultaneously because they encrypt data at different layers of the network stack – IPsec at the network layer and HTTPS at the application layer. In this case, HTTPS traffic is encapsulated in an IPsec tunnel, providing double encryption.
However, such redundancy is rarely necessary in practice. For example, using HTTPS to encrypt web sessions has already ensured confidentiality and authenticity; Repackaging it with IPsec will increase complexity, but it will not significantly improve security. That is to say, organizations with strict compliance requirements or zero-trust architectures may still use these two methods for deep defense or to protect internal routing metadata.
Expert insight
Security experts often highlight that IPsec provides broad protection by securing all traffic at the IP layer, regardless of the application or protocol. This makes it well-suited for network-level defence, especially in enterprise VPNs or between data centres.
In contrast, HTTPS offers targeted protection for web-based services and adds a crucial layer of identity assurance through certificates issued by trusted Certificate Authorities. As cybersecurity analyst Lukas Dolnicek puts it
“IPsec is best for infrastructure-wide encryption, while HTTPS ensures end-user trust and data security on the web.”
— Lukas Dolnicek
Each serves a distinct role in a layered security strategy.
Key differences at a glance
While both IPsec and HTTPS aim to secure data in transit, they differ significantly in terms of their operating layers, coverage, deployment models, and trust assumptions. Here is a breakdown of their most important distinctions:
- Layer of Operation
IPsec works at the network layer (OSI Layer 3), securing data packets regardless of the application that generates them. In contrast, HTTPS operates at the application layer (OSI Layer 7), securing only HTTP-based communication. - Traffic Coverage
IPsec can encrypt all IP-based traffic, including email (SMTP), file transfers (FTP), VoIP (SIP), and custom protocols. HTTPS, however, only secures HTTP and HTTPS traffic, which is ideal for web services and APIs. - Encryption Scope
IPsec protects the entire IP packet, including headers (in tunnel mode), which is crucial for routing protection and metadata confidentiality. HTTPS encrypts just the application data, namely the HTTP headers and body, leaving lower-layer metadata exposed. - Trust Model
IPsec uses pre-shared keys or certificates for mutual authentication between peers. Trust is typically established manually or within a private network. HTTPS relies on a global ecosystem of Certificate Authorities (CAs) to validate server identity, making it scalable for public internet use. - Deployment Complexity
IPsec requires more complex configuration, including key exchange protocols (e.g. IKE/IKEv2), tunnel setup, and potentially dedicated VPN hardware or software. HTTPS is much easier to deploy with modern tools and services like Let’s Encrypt, requiring only a valid TLS certificate and basic web server configuration. - Performance Impact
IPsec can introduce latency and fragmentation due to packet overhead, especially in tunnel mode. HTTPS is optimised for performance through TLS 1.3, session resumption, and protocols like HTTP/2 and HTTP/3, delivering strong security with minimal speed penalties. - Primary Use Cases
IPsec is widely used for VPNs, site-to-site tunnels, and full-network protection in corporate settings. HTTPS is best suited for websites, online services, and API endpoints, where user trust and browser compatibility are key concerns.
When might you use both?
While IPsec and HTTPS are generally used independently—each addressing different layers of the network stack—there are specific scenarios where organisations may choose to deploy both protocols simultaneously.
- High-security environments may require layered encryption
Organisations operating under strict regulatory frameworks—such as banks or government agencies—may use IPsec to secure internal communication across data centres or office branches, protecting all IP traffic and concealing metadata like source and destination IP addresses. - HTTPS ensures public-facing application security
In the same environments, HTTPS is typically employed to secure external web services such as online banking platforms, ensuring encryption at the application layer and providing identity verification through trusted digital certificates. - Zero-trust architectures benefit from protocol layering
In modern zero-trust security models, both protocols may be used together to achieve defence-in-depth. IPsec enforces policy-based encryption across internal network segments, while HTTPS protects individual client-server interactions over HTTP. - Dual-layer encryption introduces operational complexity
Running both protocols in tandem can complicate deployment and maintenance. It may require additional certificate management, custom configurations, and more involved troubleshooting—especially when performance or compatibility issues arise. - Justified only in compliance-driven scenarios
The security benefit of overlapping encryption is often minimal unless explicitly mandated by standards such as FIPS 140-2, HIPAA, or classified system requirements. - Not the default choice for most organisations
For most use cases, a single well-implemented protocol is sufficient. The decision to use both should be guided by risk assessment, data classification, and regulatory obligations, rather than assumptions about added security.
Future directions
Both IPsec and HTTPS continue to evolve in response to emerging security threats, performance demands, and shifts in internet architecture.
On the IPsec side, development is driven by the IETF’s IP Security Maintenance and Extensions (ipsecme) working group, which focuses on refining key exchange mechanisms like IKEv2, supporting modern cryptographic algorithms(e.g., ChaCha20-Poly1305 for improved performance on low-power devices), and enhancing NAT traversal to improve compatibility across diverse networks. As enterprises adopt hybrid cloud and multi-site deployments, IPsec remains critical for establishing secure tunnels across complex topologies.
Meanwhile, HTTPS continues its rapid progression alongside the TLS protocol. The widespread adoption of TLS 1.3has reduced handshake times, deprecated older cryptographic suites, and improved privacy by encrypting more of the negotiation process itself. In parallel, HTTP/3, built on QUIC (a transport protocol running over UDP), introduces lower latency, built-in congestion control, and improved resilience for mobile and real-time applications.
Beyond these protocols, there’s a broader movement toward end-to-end encryption across all layers of the internet stack. Technologies like DNS-over-HTTPS (DoH) and DNS-over-TLS (DoT) aim to secure traditionally exposed DNS queries. Initiatives such as Encrypted Client Hello (ECH) further extend encryption into the TLS handshake, concealing metadata like the hostname from observers.
These advancements reflect a growing consensus: encryption should be the default, not the exception. As attackers become more sophisticated and surveillance capabilities expand, both IPsec and HTTPS will continue to adapt—ensuring the confidentiality, integrity, and authenticity of data in an increasingly interconnected world.
Frequently Asked Questions (FAQs)
Can IPsec replace HTTPS?
No, because HTTPS provides publicly trusted certificate-based identity verification, which IPsec lacks; the two serve different roles in the security stack.
Is HTTPS slower than HTTP?
Not significantly—thanks to TLS 1.3 and protocols like HTTP/2 and HTTP/3, HTTPS now delivers security with performance comparable to or even better than HTTP in many cases.
Do I need IPsec if my website uses HTTPS?
Generally no, unless you also need to secure other types of traffic beyond HTTP, such as internal database access or file sharing over IP.
Can IPsec and HTTPS work together?
Yes, they can be layered for added protection in certain scenarios, but it’s rarely necessary outside of environments with strict regulatory or security requirements.
What about other encryption like DoH or DoT?
Protocols like DNS-over-HTTPS (DoH) and DNS-over-TLS (DoT) enhance privacy by encrypting DNS queries, and are complementary to HTTPS and IPsec rather than replacements.
Related Blogs
Artículos relacionados

Why self-holding can expose IPv4 assets to registry risk
Self-holding IPv4 assets increases exposure to registry risk as compliance responsibility, transfer validation, and governance pressure are concentrated internally. Key points Self-holding IPv4 assets concentrate registry compliance responsibility, increasing exposure to audits, transfer validation issues, and documentation gaps. As IPv4 scarcity grows, registry governance becomes stricter, making ownership structure a key factor in operational risk. IPv4 ownership is now defined by governance, not possession IPv4 addresses are no longerRead more Related Posts 短期与长期 IPv4 租赁 在面临 IPv4 短缺的情况下,企业在选择租赁方案时必须权衡成本、速度以及网络增长。 短期租赁可以让你轻松地扩展或缩减资源,但长期来看成本更高,且供应稳定性较低。 长期租赁提供稳定的价格和更可靠的资源获取,但随着需求变化,调整配置会变得更困难。 引言:为什么租用 IPv4 地址是合理的 IPv4 已从一种技术资源演变为一种稀缺的经济资产。尽管 IPv6 的普及仍在继续,但 IPv4 仍然是大多数生产网络的核心。过渡过程较为缓慢,受到迁移挑战、遗留系统依赖和兼容性问题的阻碍。与此同时,全球未分配的 IPv4 地址池几乎耗尽,迫使企业转向二级市场。这就是 IPv4 地址租赁的用武之地。企业可以根据需要租赁 IPv4 资源,从而避免购买地址块。并非所有 Read more 为什么你会想使用 IPv6 引言 随着企业为互联网的长期发展做好准备,IPv6 的重要性日益凸显。它提供的地址空间远大于 IPv4,并支持现代网络扩展,尤其是在云服务、移动网络、物联网、托管和全球数字基础设施等领域。 然而,IPv6 的普及尚未完成。许多企业仍然依赖 IPv4 来满足兼容性、客户访问、电子邮件系统、托管和传统应用程序的需求。这意味着真正的问题不在于 IPv6 是否有用,而在于企业如何在保持 IPv4 连续性的同时采用 IPv6。 对于许多组织而言,最佳策略是务实的:做好 IPv6 的准备,同时在客户和系统仍然依赖 IPv4 的地方保留 IPv4 的可用性。 Read more 为什么子网划分对网络管理至关重要 子网划分在现代网络中的作用 子网划分是指将大型 IP 网络分割成更小的部分。它对网络管理至关重要。子网划分使管理员能够谨慎地分配 IP 地址,从而减少浪费并避免冲突。此外,子网划分还有助于以清晰的方式组织网络。如今,许多设备都连接到网络。如果没有子网,网络可能会变得混乱不堪。子网划分使网络更易于控制。 子网划分起源于互联网 IP 地址较少的时期。工程师需要一种方法来使用地址而不会耗尽。他们将大块地址分割成更小的组。每个组都有自己的网络 ID 和主机地址。这种理念至今仍然重要。即使在拥有更多地址的 IPv6 时代,子网划分仍然能够保持网络的结构性和安全性,并且便于日后扩展网络。 对于网络管理员来说,子网划分有很多好处。它有助于合理利用地址并简化路由表,从而降低延迟并节省带宽。清晰的子网划分也使应用安全规则、控制资源和监控流量变得更加容易。每个子网可以服务于一个部门、一个地点或一个应用程序。这使得问题更容易解决,也使添加新设备更加便捷。 子网划分还有助于遵守规则和法律。许多组织出于安全考虑必须将数据隔离。子网可以隔离敏感信息,例如财务数据或个人数据。这使得访问控制和记录保存更加便捷。如果进行审计,清晰的子网划分也体现了良好的管理。子网划分不仅仅是技术层面的,它还有助于风险管理和规则遵守。 提升网络性能 网络性能至关重要。子网划分有助于提升网络运行速度。单个网络中设备过多会产生过多流量,从而导致通信速度下降。将网络划分为子网可以有效减少流量。设备仅在需要时才接收消息,从而降低延迟,使网络更加流畅。子网划分还有助于路由器更好地工作。路由器利用子网信息高效地发送数据。较小的子网可以缩短路由表,使路由器运行速度更快。当网络规模扩大时,采用子网划分的网络能够更好地处理流量。子网划分使网络扩展更加便捷。通过子网,添加新的办公室或应用程序变得简单。每个新子网都可以拥有足够的地址,而无需更改原有网络,从而保持网络的稳定性和速度。安全性也得到提升。可以密切监控子网中的流量。防火墙可以单独控制每个子网。如果某个子网遭到攻击,攻击会被控制在一定范围内,从而防止攻击扩散。子网有助于保护关键数据并降低风险。 安全与合规优势 子网划分还能提高网络安全。每个部门或功能都可以拥有自己的子网。即使一个子网遭到攻击,其他子网也能保持安全。例如,访客 Wi-Fi 子网可以与内部服务器隔离。这样可以保护重要数据的安全。子网划分使规则管理更加便捷。管理员无需控制每个设备,只需为子网设置规则即可。这既节省时间,又能保持安全性的一致性。每个子网都可以设置独立的登录信息。这可以限制攻击者,从而提高网络安全。子网划分还有助于遵守相关法规。诸如 GDPR 或 Read more .related-post {} .related-post .post-list { text-align: left; } .related-post .post-list .item { margin: 5px; padding: 10px; } .related-post .headline { font-size: 18px !important; color: #999999 !important; } .related-post .post-list .item .post_thumb { max-height: 220px; margin: 10px 0px; padding: 0px; display: block; } .related-post .post-list .item .post_title { font-size: 16px; color: #3f3f3f; margin: 10px 0px; padding: 0px; display: block; text-decoration: none; } .related-post .post-list .item .post_excerpt { font-size: 13px; color: #3f3f3f; margin: 10px 0px; padding: 0px; display: block; text-decoration: none; } @media only screen and (min-width: 1024px) { .related-post .post-list .item { width: 30%; } } @media only screen and (min-width: 768px) and (max-width: 1023px) { .related-post .post-list .item { width: 90%; } } @media only screen and (min-width: 0px) and (max-width: 767px) { .related-post .post-list .item { width: 90%; } }

Is Your Company Absorbing IPv4 Risk?
Is Your Company Becoming the Shock Absorber for IPv4 Risk? Many businesses think the biggest IPv4 risk is not having enough addresses. That is only part of the problem. The more dangerous question is this: when something goes wrong, who absorbs the damage? If your IPv4 strategy is poorly structured, the answer may be your company. Your business may carry the customers, servers, routing, contracts, compliance duties, support workload,Read more Related Posts 短期与长期 IPv4 租赁 在面临 IPv4 短缺的情况下,企业在选择租赁方案时必须权衡成本、速度以及网络增长。 短期租赁可以让你轻松地扩展或缩减资源,但长期来看成本更高,且供应稳定性较低。 长期租赁提供稳定的价格和更可靠的资源获取,但随着需求变化,调整配置会变得更困难。 引言:为什么租用 IPv4 地址是合理的 IPv4 已从一种技术资源演变为一种稀缺的经济资产。尽管 IPv6 的普及仍在继续,但 IPv4 仍然是大多数生产网络的核心。过渡过程较为缓慢,受到迁移挑战、遗留系统依赖和兼容性问题的阻碍。与此同时,全球未分配的 IPv4 地址池几乎耗尽,迫使企业转向二级市场。这就是 IPv4 地址租赁的用武之地。企业可以根据需要租赁 IPv4 资源,从而避免购买地址块。并非所有 Read more 为什么你会想使用 IPv6 引言 随着企业为互联网的长期发展做好准备,IPv6 的重要性日益凸显。它提供的地址空间远大于 IPv4,并支持现代网络扩展,尤其是在云服务、移动网络、物联网、托管和全球数字基础设施等领域。 然而,IPv6 的普及尚未完成。许多企业仍然依赖 IPv4 来满足兼容性、客户访问、电子邮件系统、托管和传统应用程序的需求。这意味着真正的问题不在于 IPv6 是否有用,而在于企业如何在保持 IPv4 连续性的同时采用 IPv6。 对于许多组织而言,最佳策略是务实的:做好 IPv6 的准备,同时在客户和系统仍然依赖 IPv4 的地方保留 IPv4 的可用性。 Read more 为什么子网划分对网络管理至关重要 子网划分在现代网络中的作用 子网划分是指将大型 IP 网络分割成更小的部分。它对网络管理至关重要。子网划分使管理员能够谨慎地分配 IP 地址,从而减少浪费并避免冲突。此外,子网划分还有助于以清晰的方式组织网络。如今,许多设备都连接到网络。如果没有子网,网络可能会变得混乱不堪。子网划分使网络更易于控制。 子网划分起源于互联网 IP 地址较少的时期。工程师需要一种方法来使用地址而不会耗尽。他们将大块地址分割成更小的组。每个组都有自己的网络 ID 和主机地址。这种理念至今仍然重要。即使在拥有更多地址的 IPv6 时代,子网划分仍然能够保持网络的结构性和安全性,并且便于日后扩展网络。 对于网络管理员来说,子网划分有很多好处。它有助于合理利用地址并简化路由表,从而降低延迟并节省带宽。清晰的子网划分也使应用安全规则、控制资源和监控流量变得更加容易。每个子网可以服务于一个部门、一个地点或一个应用程序。这使得问题更容易解决,也使添加新设备更加便捷。 子网划分还有助于遵守规则和法律。许多组织出于安全考虑必须将数据隔离。子网可以隔离敏感信息,例如财务数据或个人数据。这使得访问控制和记录保存更加便捷。如果进行审计,清晰的子网划分也体现了良好的管理。子网划分不仅仅是技术层面的,它还有助于风险管理和规则遵守。 提升网络性能 网络性能至关重要。子网划分有助于提升网络运行速度。单个网络中设备过多会产生过多流量,从而导致通信速度下降。将网络划分为子网可以有效减少流量。设备仅在需要时才接收消息,从而降低延迟,使网络更加流畅。子网划分还有助于路由器更好地工作。路由器利用子网信息高效地发送数据。较小的子网可以缩短路由表,使路由器运行速度更快。当网络规模扩大时,采用子网划分的网络能够更好地处理流量。子网划分使网络扩展更加便捷。通过子网,添加新的办公室或应用程序变得简单。每个新子网都可以拥有足够的地址,而无需更改原有网络,从而保持网络的稳定性和速度。安全性也得到提升。可以密切监控子网中的流量。防火墙可以单独控制每个子网。如果某个子网遭到攻击,攻击会被控制在一定范围内,从而防止攻击扩散。子网有助于保护关键数据并降低风险。 安全与合规优势 子网划分还能提高网络安全。每个部门或功能都可以拥有自己的子网。即使一个子网遭到攻击,其他子网也能保持安全。例如,访客 Wi-Fi 子网可以与内部服务器隔离。这样可以保护重要数据的安全。子网划分使规则管理更加便捷。管理员无需控制每个设备,只需为子网设置规则即可。这既节省时间,又能保持安全性的一致性。每个子网都可以设置独立的登录信息。这可以限制攻击者,从而提高网络安全。子网划分还有助于遵守相关法规。诸如 GDPR 或 Read more .related-post {} .related-post .post-list { text-align: left; } .related-post .post-list .item { margin: 5px; padding: 10px; } .related-post .headline { font-size: 18px !important; color: #999999 !important; } .related-post .post-list .item .post_thumb { max-height: 220px; margin: 10px 0px; padding: 0px; display: block; } .related-post .post-list .item .post_title { font-size: 16px; color: #3f3f3f; margin: 10px 0px; padding: 0px; display: block; text-decoration: none; } .related-post .post-list .item .post_excerpt { font-size: 13px; color: #3f3f3f; margin: 10px 0px; padding: 0px; display: block; text-decoration: none; } @media only screen and (min-width: 1024px) { .related-post .post-list .item { width: 30%; } } @media only screen and (min-width: 768px) and (max-width: 1023px) { .related-post .post-list .item { width: 90%; } } @media only screen and (min-width: 0px) and (max-width: 767px) { .related-post .post-list .item { width: 90%; } }

What If a Policy Room Risks Your Running Network?
What If a Policy Room Puts Your Running Network at Risk? Your network may be running today. Your customers may be connected. Your servers may be online. Your IPv4 addresses may already support applications, hosting, VPNs, SaaS platforms, email systems, cloud workloads, and revenue-generating services. But what if the real risk is not inside your data centre? What if the risk sits above your network — inside policy rooms,Read more Related Posts 短期与长期 IPv4 租赁 在面临 IPv4 短缺的情况下,企业在选择租赁方案时必须权衡成本、速度以及网络增长。 短期租赁可以让你轻松地扩展或缩减资源,但长期来看成本更高,且供应稳定性较低。 长期租赁提供稳定的价格和更可靠的资源获取,但随着需求变化,调整配置会变得更困难。 引言:为什么租用 IPv4 地址是合理的 IPv4 已从一种技术资源演变为一种稀缺的经济资产。尽管 IPv6 的普及仍在继续,但 IPv4 仍然是大多数生产网络的核心。过渡过程较为缓慢,受到迁移挑战、遗留系统依赖和兼容性问题的阻碍。与此同时,全球未分配的 IPv4 地址池几乎耗尽,迫使企业转向二级市场。这就是 IPv4 地址租赁的用武之地。企业可以根据需要租赁 IPv4 资源,从而避免购买地址块。并非所有 Read more 为什么你会想使用 IPv6 引言 随着企业为互联网的长期发展做好准备,IPv6 的重要性日益凸显。它提供的地址空间远大于 IPv4,并支持现代网络扩展,尤其是在云服务、移动网络、物联网、托管和全球数字基础设施等领域。 然而,IPv6 的普及尚未完成。许多企业仍然依赖 IPv4 来满足兼容性、客户访问、电子邮件系统、托管和传统应用程序的需求。这意味着真正的问题不在于 IPv6 是否有用,而在于企业如何在保持 IPv4 连续性的同时采用 IPv6。 对于许多组织而言,最佳策略是务实的:做好 IPv6 的准备,同时在客户和系统仍然依赖 IPv4 的地方保留 IPv4 的可用性。 Read more 如何获取 IPv4 地址 .related-post {} .related-post .post-list { text-align: left; } .related-post .post-list .item { margin: 5px; padding: 10px; } .related-post .headline { font-size: 18px !important; color: #999999 !important; } .related-post .post-list .item .post_thumb { max-height: 220px; margin: 10px 0px; padding: 0px; display: block; } .related-post .post-list .item .post_title { font-size: 16px; color: #3f3f3f; margin: 10px 0px; padding: 0px; display: block; text-decoration: none; } .related-post .post-list .item .post_excerpt { font-size: 13px; color: #3f3f3f; margin: 10px 0px; padding: 0px; display: block; text-decoration: none; } @media only screen and (min-width: 1024px) { .related-post .post-list .item { width: 30%; } } @media only screen and (min-width: 768px) and (max-width: 1023px) { .related-post .post-list .item { width: 90%; } } @media only screen and (min-width: 0px) and (max-width: 767px) { .related-post .post-list .item { width: 90%; } }
