DoS 和 DDoS 攻击的区别
拒绝服务(DoS)攻击试图通过压倒性的流量或请求,使用户无法使用机器、网络或服务。它通常来自单一来源。
分布式拒绝服务 (DDoS) 攻击的意图类似,但涉及多个系统(通常是僵尸网络)同时攻击受害者,因此更难阻止或追踪。
Table of Contents
DoS 和 DDoS 攻击的关键特征
DoS 攻击
1) 单一流量来源。
2) 由于可识别来源,因此更容易缓解。
3) 规模和复杂性低于 DDoS。
DDoS 攻击
1) 分布在多个受损系统上。
2) 规模大、复杂程度高。
3) 由于流量来源不同,更难阻止。
常用 DoS/DDoS 攻击工具
- 低轨道离子炮(LOIC): 用于基本 DoS 攻击的开源工具。
- HOIC(高轨道离子炮): LOIC 的后继者,攻击机制更具攻击性和可配置性。
- Mirai 僵尸网络: 一种利用物联网设备发动大规模 DDoS 攻击的恶意软件。
- Slowloris:一种长时间保持连接开放、耗尽服务器资源的工具。
- HTTP 不堪重负王(HULK): 产生大量独特请求,使服务器不堪重负。
如何抵御 DoS/DDoS 工具的攻击?
1) 内容分发网络(CDN): Cloudflare 或 Akamai 等 CDN 可在多个服务器之间分发流量,从而减少攻击。
2) 使用 DDoS 防护服务: AWS Shield 和 Arbor Networks 等服务可检测和缓解大规模攻击。
3)配置防火墙和速率限制: 实施防火墙规则以检测异常流量,并实施速率限制以限制来自单一 IP 的请求。
4)配置防火墙和速率限制: 实施防火墙规则以检测异常流量,并实施速率限制以限制来自单一 IP 的请求。
5)监控流量模式: 使用 Nagios 或 Zabbix 等工具及早发现流量模式的异常。
6)实施高级安全功能: 部署网络应用防火墙(WAF)和入侵防御系统(IPS),过滤恶意流量。
DoS 和 DDoS 小总结
DoS 和 DDoS 攻击听起来像是专业术语,但了解它们是保护您的网络世界的关键。这些网络威胁会严重扰乱业务和服务,但只要有正确的工具和积极主动的措施,就能对其进行有效管理。随时了解情况并做好准备,可确保您的数字生活安全、顺畅地运行。
Related Posts
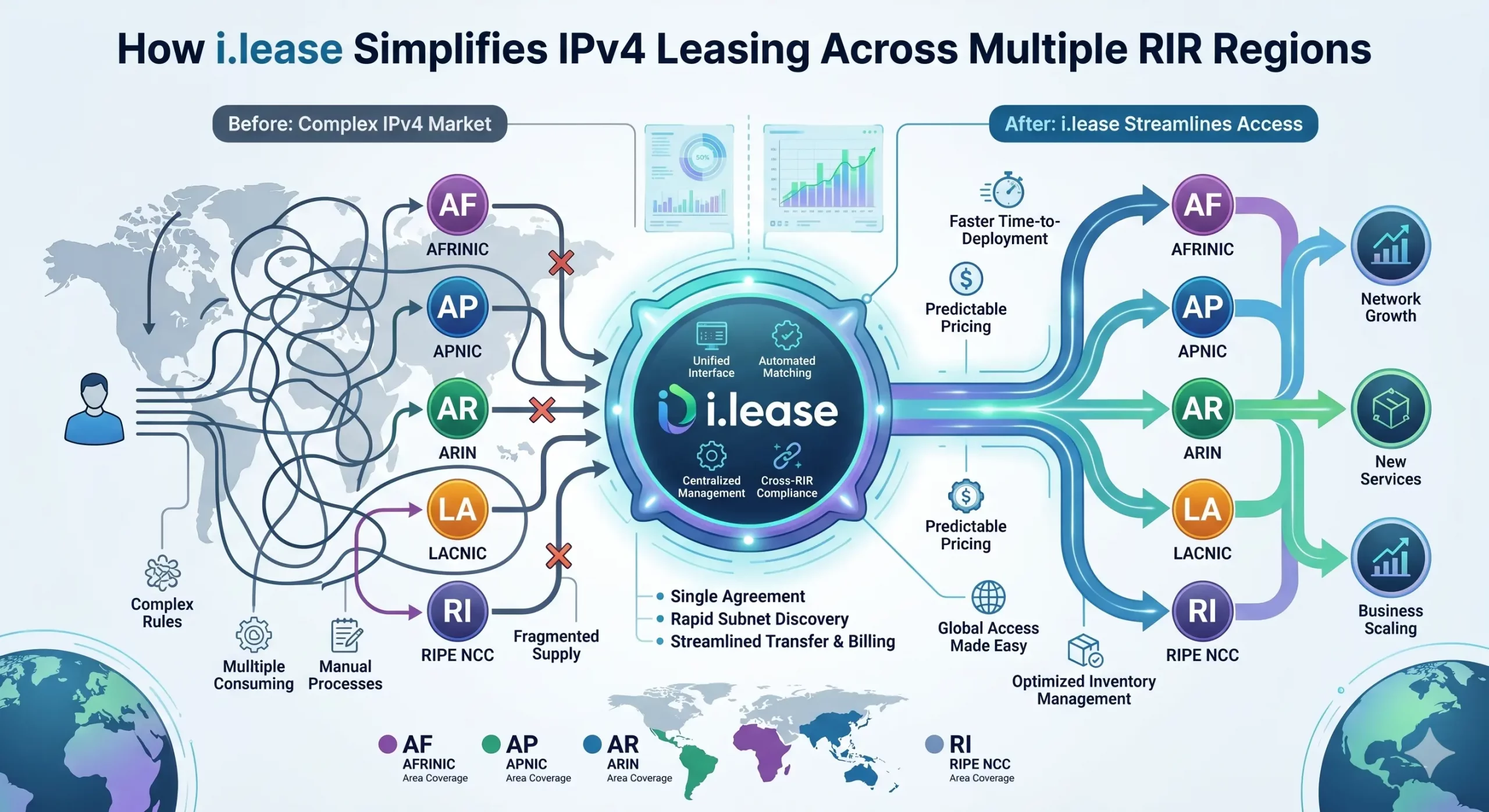
How i.lease Simplifies IPv4 Leasing Across Multiple RIR Regions
In today’s Internet infrastructure economy, IPv4 address leasing has become a critical operational strategy for enterprises, cloud providers, and network operators facing persistent address scarcity. As IPv4 exhaustion continues across all five Regional Internet Registries (RIRs)—ARIN, RIPE NCC, APNIC, LACNIC, and AFRINIC—the need for structured, compliant, and cross-regional leasing solutions has never been greater. However, beneath the surface of what appears to be a simple “supply-and-demand” market lies aRead more Related Posts Risk Placement in IPv4 Transactions: What Enterprises Should Know The IPv4 market has quietly evolved into a structured secondary asset class. As global IPv4 exhaustion continues, enterprises, ISPs, and Understanding Operational Risk in IPv4 Address Markets IPv4 has long stopped being a simple technical identifier system. It has become a constrained, priced, and operationally embedded infrastructure Por qué la mayoría de las empresas están expuestas accidentalmente al riesgo de fallo en la asignación de IPv4 La escasez de IPv4 es ampliamente comprendida. Lo que muchas empresas aún subestiman es el riesgo de continuidad relacionado con .related-post {} .related-post .post-list { text-align: left; } .related-post .post-list .item { margin: 5px; padding: 10px; } .related-post .headline { font-size: 18px !important; color: #999999 !important; } .related-post .post-list .item .post_thumb { max-height: 220px; margin: 10px 0px; padding: 0px; display: block; } .related-post .post-list .item .post_title { font-size: 16px; color: #3f3f3f; margin: 10px 0px; padding: 0px; display: block; text-decoration: none; } .related-post .post-list .item .post_excerpt { font-size: 13px; color: #3f3f3f; margin: 10px 0px; padding: 0px; display: block; text-decoration: none; } @media only screen and (min-width: 1024px) { .related-post .post-list .item { width: 30%; } } @media only screen and (min-width: 768px) and (max-width: 1023px) { .related-post .post-list .item { width: 90%; } } @media only screen and (min-width: 0px) and (max-width: 767px) { .related-post .post-list .item { width: 90%; } }
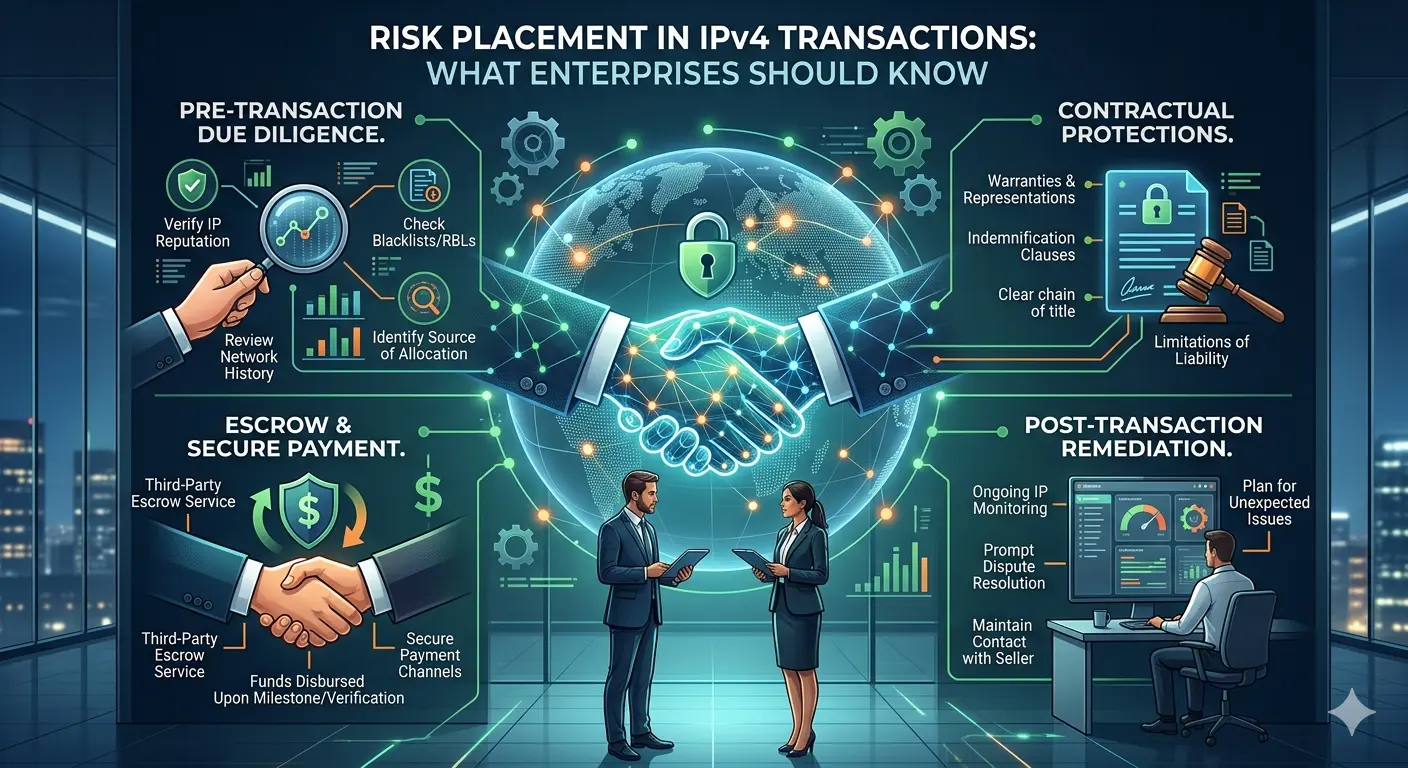
Risk Placement in IPv4 Transactions: What Enterprises Should Know
The IPv4 market has quietly evolved into a structured secondary asset class. As global IPv4 exhaustion continues, enterprises, ISPs, and brokers now routinely engage in buying, leasing, and transferring IPv4 address blocks. Alongside this growth, one topic has become increasingly important—but still under-discussed: risk placement in IPv4 transactions. For organizations participating in this market, especially through platforms such as i.lease, understanding how risk is identified, allocated, and mitigated isRead more Related Posts Risk Placement in IPv4 Transactions: What Enterprises Should Know The IPv4 market has quietly evolved into a structured secondary asset class. As global IPv4 exhaustion continues, enterprises, ISPs, and Understanding Operational Risk in IPv4 Address Markets IPv4 has long stopped being a simple technical identifier system. It has become a constrained, priced, and operationally embedded infrastructure Por qué la mayoría de las empresas están expuestas accidentalmente al riesgo de fallo en la asignación de IPv4 La escasez de IPv4 es ampliamente comprendida. Lo que muchas empresas aún subestiman es el riesgo de continuidad relacionado con .related-post {} .related-post .post-list { text-align: left; } .related-post .post-list .item { margin: 5px; padding: 10px; } .related-post .headline { font-size: 18px !important; color: #999999 !important; } .related-post .post-list .item .post_thumb { max-height: 220px; margin: 10px 0px; padding: 0px; display: block; } .related-post .post-list .item .post_title { font-size: 16px; color: #3f3f3f; margin: 10px 0px; padding: 0px; display: block; text-decoration: none; } .related-post .post-list .item .post_excerpt { font-size: 13px; color: #3f3f3f; margin: 10px 0px; padding: 0px; display: block; text-decoration: none; } @media only screen and (min-width: 1024px) { .related-post .post-list .item { width: 30%; } } @media only screen and (min-width: 768px) and (max-width: 1023px) { .related-post .post-list .item { width: 90%; } } @media only screen and (min-width: 0px) and (max-width: 767px) { .related-post .post-list .item { width: 90%; } }
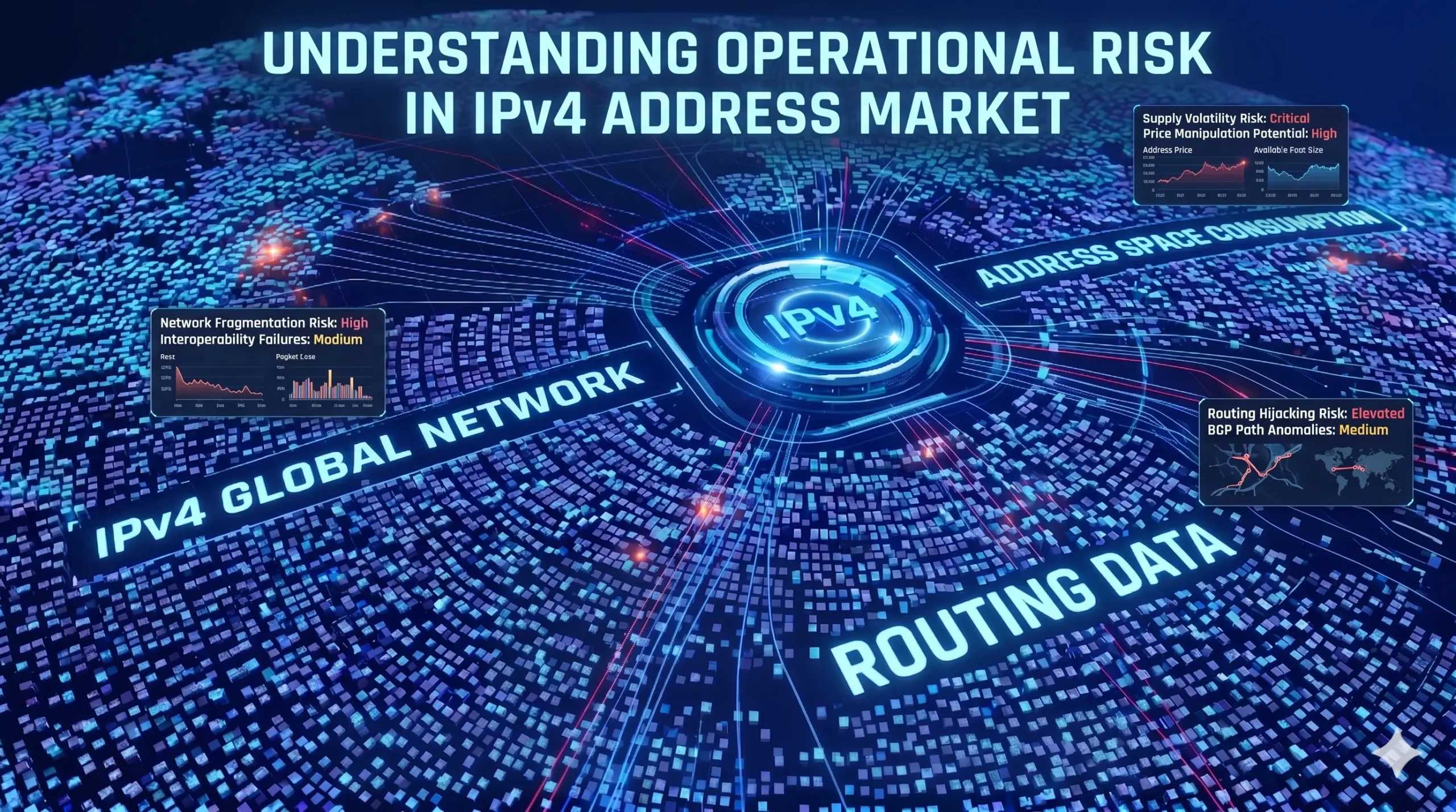
Understanding Operational Risk in IPv4 Address Markets
IPv4 has long stopped being a simple technical identifier system. It has become a constrained, priced, and operationally embedded infrastructure asset class. “In the IPv4 market, execution is not paperwork. Execution is continuity under registry-layer uncertainty.”https://heng.lu/on-why-i-lease-exists-and-why-the-broker-question-is-really-a-registry-risk-question/ Yet most of the industry still speaks about it as if it were a straightforward marketplace problem: buyers, sellers, brokers, escrow, transfer, done. That framing is increasingly outdated. The real structure of riskRead more Related Posts Risk Placement in IPv4 Transactions: What Enterprises Should Know The IPv4 market has quietly evolved into a structured secondary asset class. As global IPv4 exhaustion continues, enterprises, ISPs, and Understanding Operational Risk in IPv4 Address Markets IPv4 has long stopped being a simple technical identifier system. It has become a constrained, priced, and operationally embedded infrastructure Por qué la mayoría de las empresas están expuestas accidentalmente al riesgo de fallo en la asignación de IPv4 La escasez de IPv4 es ampliamente comprendida. Lo que muchas empresas aún subestiman es el riesgo de continuidad relacionado con .related-post {} .related-post .post-list { text-align: left; } .related-post .post-list .item { margin: 5px; padding: 10px; } .related-post .headline { font-size: 18px !important; color: #999999 !important; } .related-post .post-list .item .post_thumb { max-height: 220px; margin: 10px 0px; padding: 0px; display: block; } .related-post .post-list .item .post_title { font-size: 16px; color: #3f3f3f; margin: 10px 0px; padding: 0px; display: block; text-decoration: none; } .related-post .post-list .item .post_excerpt { font-size: 13px; color: #3f3f3f; margin: 10px 0px; padding: 0px; display: block; text-decoration: none; } @media only screen and (min-width: 1024px) { .related-post .post-list .item { width: 30%; } } @media only screen and (min-width: 768px) and (max-width: 1023px) { .related-post .post-list .item { width: 90%; } } @media only screen and (min-width: 0px) and (max-width: 767px) { .related-post .post-list .item { width: 90%; } }
