How does the government track down people using their IP addresses?
Queries: How does the government track down people using their IP addresses? Why is it difficult for them to catch scammers and hackers?
Table of Contents
IP addresses serve as unique identifiers for internet users, enabling connectivity and interaction. Governments and law enforcement agencies utilize these digital signatures to track down individuals involved in illegal online activities.
However, capturing scammers and hackers isn’t as straightforward as it might seem. Despite the sophisticated technology at their disposal, authorities often find themselves playing a high-stakes game of digital hide-and-seek. This is due to the advanced evasion techniques employed by cybercriminals, the transient nature of IP addresses, and the complex, borderless realm of cyberspace.
In this article, we’ll explore how IP tracking is used by governments and why, despite these efforts, scammers and hackers often remain one step ahead.
Internet Protocol Addresses

Every device connected to the internet is identified by a unique number known as an IP (Internet Protocol) address. This digital identifier is crucial not only for everyday communications but also for law enforcement agencies that need to track down individuals involved in illegal online activities. However, the task of catching cybercriminals like scammers and hackers is fraught with challenges, despite the sophisticated tools at the disposal of governments. Here’s a closer look at how governments use IP addresses for tracking and why catching cybercriminals remains a complex issue.
How Governments Track Individuals Through IP Addresses
Governments and law enforcement agencies can trace digital activities back to specific IP addresses through various means. One of the primary methods involves cooperation with Internet Service Providers (ISPs). ISPs typically maintain detailed logs that link IP addresses to their customers’ accounts. When suspicious activities are detected, authorities can request these logs under legal mandates, which allow them to identify the individual associated with a particular IP address at a given time.
Additionally, governments often collaborate with online platforms such as social media sites, email providers, and other digital services. These platforms can provide valuable logs that detail the IP addresses used to access particular accounts or conduct specific actions online. This data can be instrumental in piecing together a suspect’s online presence and activities.
Challenges in Catching Scammers and Hackers
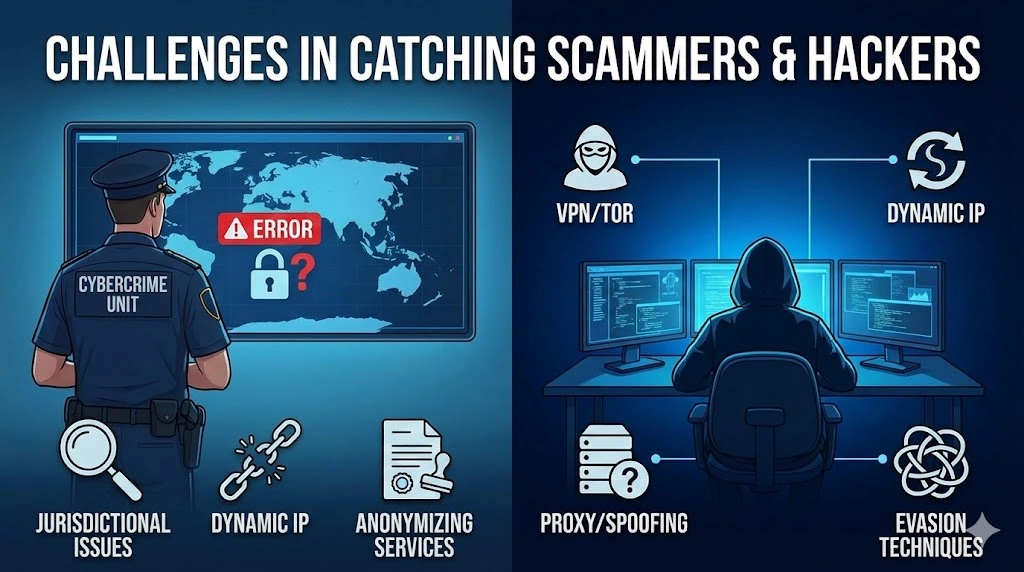
Despite the ability to track IP addresses, several significant obstacles make it difficult for authorities to apprehend cybercriminals:
Use of Anonymizing Services
Many scammers and hackers use VPNs (Virtual Private Networks), proxies, and services like Tor to mask their IP addresses. These tools can hide the user’s real IP address and make it appear as if they are operating from a different location, often in a completely different part of the world.
Dynamic IP Addresses
Many ISPs assign dynamic IP addresses, which change periodically. This variability can make it challenging to pinpoint who had access to a specific IP address at any given time without accurate logs from the ISP.
International Jurisdictional Issues
Cybercrime often transcends borders, with criminals operating from one country while committing crimes in another. This global nature of the internet creates significant legal and practical challenges in cooperation between different countries’ law enforcement agencies.
Advanced Evasion Techniques
Hackers often employ sophisticated methods to avoid detection, including spoofing IP addresses or using compromised systems as proxies for their attacks. This not only obscures their trail but also complicates the legal process of tracking and prosecuting them.
Moving Forward
Addressing the challenges of tracking cybercriminals requires international cooperation and consistent advancements in cybersecurity technology. Law enforcement agencies must also keep pace with the rapidly evolving techniques used by criminals. Additionally, there’s a growing need for legislation that addresses the unique challenges posed by digital crime and ensures that ISPs and other online platforms cooperate fully with investigations.
In conclusion, while the tracking of individuals through IP addresses is a powerful tool for law enforcement, the complexities of the digital age offer unprecedented challenges that require innovative solutions. As cybercrime continues to evolve, so too must the strategies to combat it, ensuring a safer online environment for all users.
Trusted IPv4 Leasing for Business Growth
Get enterprise-grade IPv4 space quickly, with seamless deployment and end-to-end management.
Get Started with i.leaseFAQs
Does "Incognito Mode" hide my activity from the government?
No. Incognito (or Private) mode only prevents your browser from saving your history on your specific device. Your Internet Service Provider (ISP) can still see every website you visit, and they can be legally compelled to share those logs with government agencies.
How long do ISPs keep IP address logs?
Data retention laws vary by country. In the US, ISPs typically retain IP assignment logs for 6 months to 2 years. In the EU, retention periods are strictly regulated but still exist for law enforcement purposes. These logs are the primary link between an IP address and a subscriber’s identity.
Can the government track me through the Tor Browser?
Tor is much harder to track than a standard VPN because it bounces traffic through three different volunteer nodes. However, government agencies (like the NSA or FBI) have developed sophisticated techniques (such as “Traffic Correlation” or compromising exit nodes) to de-anonymize users in high-profile criminal investigations.
Related Posts

IPv4 leasing vs purchasing: structural risk in the IPv4 address market
IPv4 leasing vs purchasing reflects a structural shift in IP address markets, balancing cost, control, scarcity, and operational risk in 2026. Key points IPv4 leasing has become a flexible operating model, with stable monthly pricing driven by scarcity and fast deployment needs. IPv4 purchasing is shifting into a long-term asset strategy, but exposed to price cycles, liquidity changes, and capital lock-in. IPv4 is no longer just infrastructure — itRead more Related Posts IPv4 租赁 vs 购买|2026 年 IPv4 市场结构性风险解析 在 IPv4 稀缺持续加剧的市场中,租赁与购买已不只是价格差异,而是两种不同的风险结构。本文解析 IPv4 租赁与购买的成本、控制权、连续性、市场风险与适用场景,帮助企业制定更合适的 IP 策略。 重点摘要 到了 2026 年,IPv4 租赁已经成为一种更灵活的运营模式,月租价格相对稳定,主要由稀缺性和快速部署需求驱动。IPv4 购买则越来越像一种长期资产策略,但也会暴露在价格周期、流动性变化和资金锁定风险之下。 IPv4 已经不只是基础设施,它是一个稀缺市场 IPv4 地址系统已经完全转入二级市场生态。自从 IANA 的免费分配耗尽后,组织现在主要依赖以下方式取得 IPv4:通过区域互联网注册机构(RIR)的转移经纪撮合的二级市场买卖像 Read more IPv4 leasing vs purchasing: structural risk in the IPv4 address market IPv4 leasing vs purchasing reflects a structural shift in IP address markets, balancing cost, control, scarcity, and operational risk in Read more تأجير IPv4 لمراكز البيانات: ما الذي تحتاج إلى معرفته مع تزايد ندرة IPv4، تعتمد مراكز البيانات بشكل متزايد على التأجير لتوسيع البنية التحتية، والتحكم في التكاليف، والحفاظ على اتصال Read more .related-post {} .related-post .post-list { text-align: left; } .related-post .post-list .item { margin: 5px; padding: 10px; } .related-post .headline { font-size: 18px !important; color: #999999 !important; } .related-post .post-list .item .post_thumb { max-height: 220px; margin: 10px 0px; padding: 0px; display: block; } .related-post .post-list .item .post_title { font-size: 16px; color: #3f3f3f; margin: 10px 0px; padding: 0px; display: block; text-decoration: none; } .related-post .post-list .item .post_excerpt { font-size: 13px; color: #3f3f3f; margin: 10px 0px; padding: 0px; display: block; text-decoration: none; } @media only screen and (min-width: 1024px) { .related-post .post-list .item { width: 30%; } } @media only screen and (min-width: 768px) and (max-width: 1023px) { .related-post .post-list .item { width: 90%; } } @media only screen and (min-width: 0px) and (max-width: 767px) { .related-post .post-list .item { width: 90%; } }

IPv4 Leasing for Data Centres: What You Need To Know
As IPv4 scarcity intensifies, data centres increasingly rely on leasing to scale infrastructure, control costs, and maintain reliable connectivity worldwide. IPv4 leasing has become a critical strategy for data centres facing address shortages and rising acquisition costs Leasing offers flexibility and scalability, but introduces risks around reputation, compliance, and long-term dependency Understanding IPv4 and why data centres still depend on it Despite years of tech progress IPv4 is stillRead more Related Posts IPv4 租赁 vs 购买|2026 年 IPv4 市场结构性风险解析 在 IPv4 稀缺持续加剧的市场中,租赁与购买已不只是价格差异,而是两种不同的风险结构。本文解析 IPv4 租赁与购买的成本、控制权、连续性、市场风险与适用场景,帮助企业制定更合适的 IP 策略。 重点摘要 到了 2026 年,IPv4 租赁已经成为一种更灵活的运营模式,月租价格相对稳定,主要由稀缺性和快速部署需求驱动。IPv4 购买则越来越像一种长期资产策略,但也会暴露在价格周期、流动性变化和资金锁定风险之下。 IPv4 已经不只是基础设施,它是一个稀缺市场 IPv4 地址系统已经完全转入二级市场生态。自从 IANA 的免费分配耗尽后,组织现在主要依赖以下方式取得 IPv4:通过区域互联网注册机构(RIR)的转移经纪撮合的二级市场买卖像 Read more IPv4 leasing vs purchasing: structural risk in the IPv4 address market IPv4 leasing vs purchasing reflects a structural shift in IP address markets, balancing cost, control, scarcity, and operational risk in Read more تأجير IPv4 لمراكز البيانات: ما الذي تحتاج إلى معرفته مع تزايد ندرة IPv4، تعتمد مراكز البيانات بشكل متزايد على التأجير لتوسيع البنية التحتية، والتحكم في التكاليف، والحفاظ على اتصال Read more .related-post {} .related-post .post-list { text-align: left; } .related-post .post-list .item { margin: 5px; padding: 10px; } .related-post .headline { font-size: 18px !important; color: #999999 !important; } .related-post .post-list .item .post_thumb { max-height: 220px; margin: 10px 0px; padding: 0px; display: block; } .related-post .post-list .item .post_title { font-size: 16px; color: #3f3f3f; margin: 10px 0px; padding: 0px; display: block; text-decoration: none; } .related-post .post-list .item .post_excerpt { font-size: 13px; color: #3f3f3f; margin: 10px 0px; padding: 0px; display: block; text-decoration: none; } @media only screen and (min-width: 1024px) { .related-post .post-list .item { width: 30%; } } @media only screen and (min-width: 768px) and (max-width: 1023px) { .related-post .post-list .item { width: 90%; } } @media only screen and (min-width: 0px) and (max-width: 767px) { .related-post .post-list .item { width: 90%; } }
What are the risks of buying IPv4 from the wrong source?
Buying IPv4 addresses outside proper IP Allocation channels exposes organisations to fraud, legal disputes, operational failures and long-term governance risks. Key points: Poorly governed IPv4 transactions can fail regional internet registry checks, leading to loss of assets or invalid transfers. Cheap or unverified sources often hide risks including hijacked IP space, blacklisting, and non-compliance with centralized IP allocation policies. Introduction: scarcity fuels risk in the IPv4 market The globalRead more Related Posts IPv4 租赁 vs 购买|2026 年 IPv4 市场结构性风险解析 在 IPv4 稀缺持续加剧的市场中,租赁与购买已不只是价格差异,而是两种不同的风险结构。本文解析 IPv4 租赁与购买的成本、控制权、连续性、市场风险与适用场景,帮助企业制定更合适的 IP 策略。 重点摘要 到了 2026 年,IPv4 租赁已经成为一种更灵活的运营模式,月租价格相对稳定,主要由稀缺性和快速部署需求驱动。IPv4 购买则越来越像一种长期资产策略,但也会暴露在价格周期、流动性变化和资金锁定风险之下。 IPv4 已经不只是基础设施,它是一个稀缺市场 IPv4 地址系统已经完全转入二级市场生态。自从 IANA 的免费分配耗尽后,组织现在主要依赖以下方式取得 IPv4:通过区域互联网注册机构(RIR)的转移经纪撮合的二级市场买卖像 Read more IPv4 leasing vs purchasing: structural risk in the IPv4 address market IPv4 leasing vs purchasing reflects a structural shift in IP address markets, balancing cost, control, scarcity, and operational risk in Read more تأجير IPv4 لمراكز البيانات: ما الذي تحتاج إلى معرفته مع تزايد ندرة IPv4، تعتمد مراكز البيانات بشكل متزايد على التأجير لتوسيع البنية التحتية، والتحكم في التكاليف، والحفاظ على اتصال Read more .related-post {} .related-post .post-list { text-align: left; } .related-post .post-list .item { margin: 5px; padding: 10px; } .related-post .headline { font-size: 18px !important; color: #999999 !important; } .related-post .post-list .item .post_thumb { max-height: 220px; margin: 10px 0px; padding: 0px; display: block; } .related-post .post-list .item .post_title { font-size: 16px; color: #3f3f3f; margin: 10px 0px; padding: 0px; display: block; text-decoration: none; } .related-post .post-list .item .post_excerpt { font-size: 13px; color: #3f3f3f; margin: 10px 0px; padding: 0px; display: block; text-decoration: none; } @media only screen and (min-width: 1024px) { .related-post .post-list .item { width: 30%; } } @media only screen and (min-width: 768px) and (max-width: 1023px) { .related-post .post-list .item { width: 90%; } } @media only screen and (min-width: 0px) and (max-width: 767px) { .related-post .post-list .item { width: 90%; } }
