What is SSH? | Secure Shell (SSH) Protocol

Securing communications between devices is important, especially when managing remote systems. One of the most widely used and trusted protocols for secure remote access is SSH (Secure Shell). This article will dive into what SSH is, how it works, and why it’s so important for network security.
Table of Contents
What is SSH?
SSH (Secure Shell) is a network protocol that allows users to access and manage remote computers securely over an unsecured network, such as the Internet. SSH encrypts the communication between the client (your computer) and the remote server, ensuring that sensitive data like login credentials and commands cannot be intercepted by third parties.
It is a preferred method for system administrators, developers, and IT professionals to control remote servers and devices, providing a safer alternative to older protocols like Telnet, which send data in plain text.
How SSH Works
SSH operates using a client-server model, meaning a user connects from their local device (client) to a remote machine (server). Here’s how the process typically works:
Firstly, Establishing Connection: The user initiates a connection by using an SSH client (software) to communicate with the SSH server running on the remote machine.
Secondly, Authentication: The server authenticates the client using one of several methods, including password-based authentication or public key authentication. Once the authentication is successful, the user gains access to the server.
Thirdly, Encryption: During the session, all data transferred between the client and the server is encrypted, ensuring that even if someone intercepts the data, they cannot read or modify it.
Key Features of Secure Shell Protocols
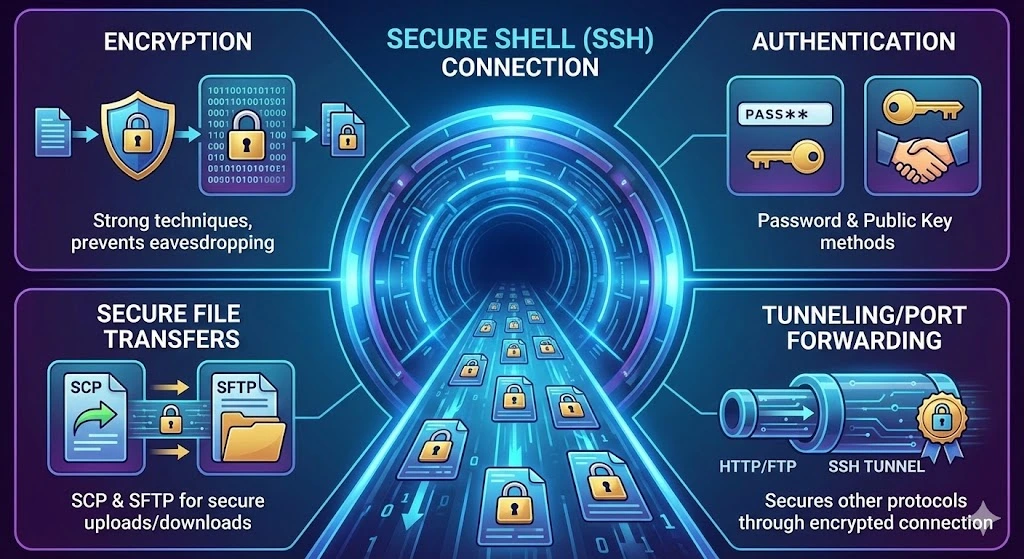
Encryption: SSH uses strong encryption techniques to ensure that all data exchanged between the client and the server is secure. This prevents eavesdropping and tampering by malicious actors.
Authentication: SSH supports several methods of authentication, including password authentication and public Key Authentication.
Secure File Transfers: SSH supports secure file transfers using protocols like SCP (Secure Copy) and SFTP (Secure File Transfer Protocol). This allows users to upload or download files to and from the remote server without worrying about security risks.
Tunneling/Port Forwarding: SSH can securely “tunnel” other protocols (such as HTTP or FTP) through the encrypted SSH connection, enabling secure communication for otherwise unsecured applications.
Common uses of SSH
SSH is primarily used for remote login, enabling system administrators and developers to access and manage remote machines anywhere securely. In addition, SSH is commonly used for file transfers, allowing users to securely move files between a local machine and a remote server using tools like SCP or SFTP.
Another important use of SSH is in automating tasks, such as deploying code, running scripts, or performing backups on remote systems. Additionally, SSH can be used for tunneling services, securely routing insecure network traffic through an encrypted connection to protect sensitive data.
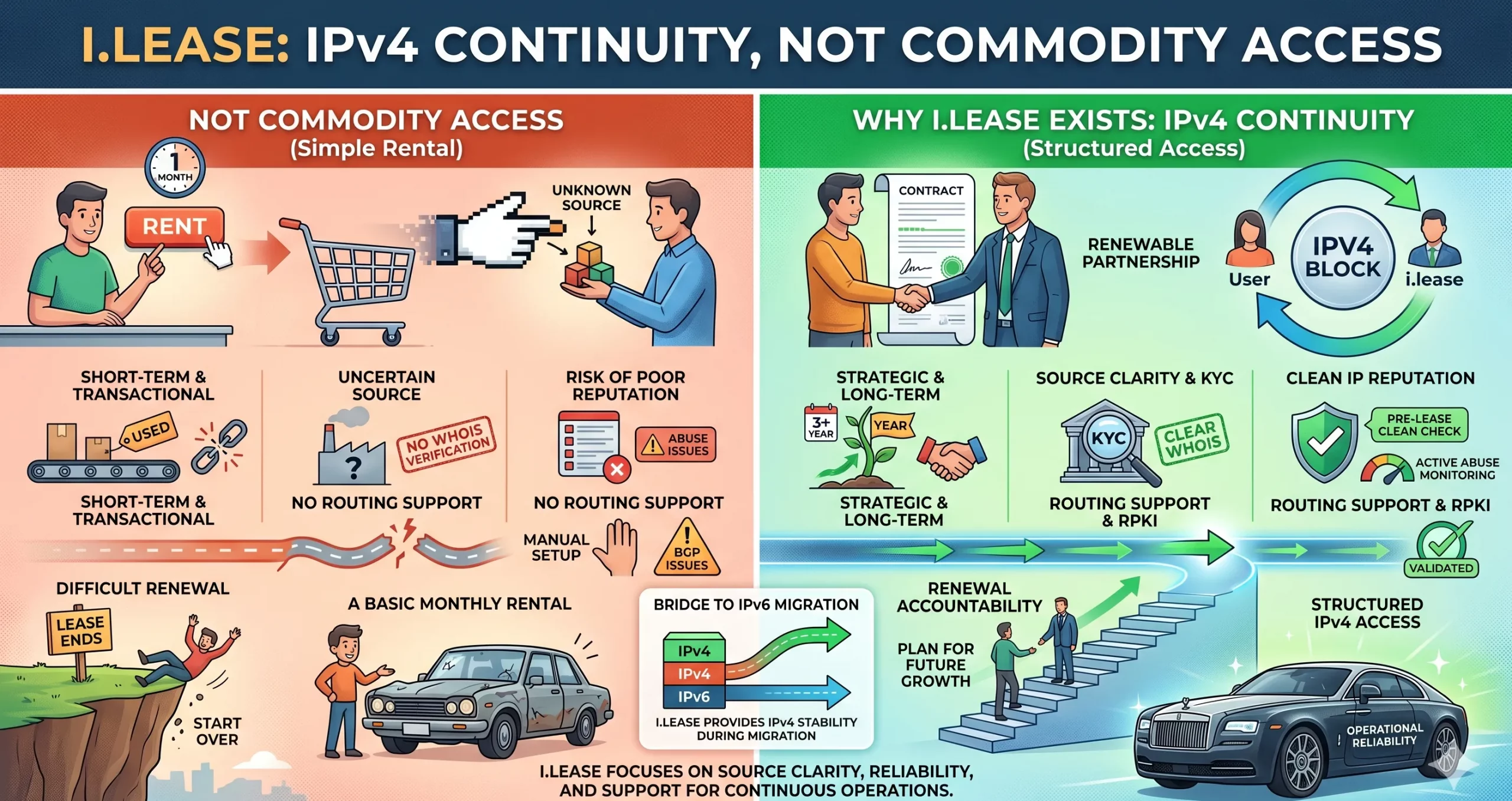
Trusted IPv4 Leasing for Business Growth
Get enterprise-grade IPv4 space quickly, with seamless deployment and end-to-end management.
Get Started with i.leaseFAQs
What is the default port for SSH, and should I change it?
The default port for SSH is Port 22. It is highly recommended to change this default port to a custom number (e.g., 2222 or 1022) on your server. This simple security measure, known as “security through obscurity,” helps reduce the number of automated brute-force attacks and unauthorized login attempts from bots scanning for open default ports.
What is the difference between SSH and Telnet?
The main difference is security. Telnet transmits data, including usernames and passwords, in plain text, meaning anyone intercepting the network traffic can read the credentials. SSH (Secure Shell) uses encryption to scramble data during transmission, making it unreadable to hackers. SSH effectively replaced Telnet for this reason.
Is SSH the same as a VPN?
No, they serve different purposes. SSH is primarily used to securely access and manage a specific remote computer or server via a command line. A VPN (Virtual Private Network) encrypts the internet traffic for an entire device or network, effectively masking your location and securing all browser and app activity. However, SSH tunneling can mimic some VPN features by routing traffic through a secure server.
Can SSH be used on Windows?
Yes. While SSH is native to Linux and macOS terminals, Windows users can use SSH via Windows PowerShell, the Command Prompt (in newer versions of Windows 10/11), or by using third-party clients like PuTTY or MobaXterm.
Articles connexes

Primauté du code en cours d’exécution : pourquoi la location d’adresses IPv4 doit être jugée sur la base de preuves opérationnelles
La location IPv4 commence souvent par une question simple : Ce fournisseur peut-il nous fournir les adresses ? Mais pour les entreprises qui dépendent de l’IPv4 pour l’hébergement, le VPN, le SaaS, le cloud, les télécommunications, la sécurité, la livraison d’e-mails ou les plateformes destinées aux clients, cette question ne suffit pas. Une meilleure question est : Cette structure IPv4 peut-elle prouver qu’elle fonctionne sur le plan opérationnel ? Related Posts How i.lease Simplifies IPv4 Leasing Across Multiple RIR Regions In today’s Internet infrastructure economy, IPv4 address leasing has become a critical operational strategy for enterprises, cloud providers, and network Understanding Operational Risk in IPv4 Address Markets IPv4 has long stopped being a simple technical identifier system. It has become a constrained, priced, and operationally embedded infrastructure Por qué la mayoría de las empresas están expuestas accidentalmente al riesgo de fallo en la asignación de IPv4 La escasez de IPv4 es ampliamente comprendida. Lo que muchas empresas aún subestiman es el riesgo de continuidad relacionado con .related-post {} .related-post .post-list { text-align: left; } .related-post .post-list .item { margin: 5px; padding: 10px; } .related-post .headline { font-size: 18px !important; color: #999999 !important; } .related-post .post-list .item .post_thumb { max-height: 220px; margin: 10px 0px; padding: 0px; display: block; } .related-post .post-list .item .post_title { font-size: 16px; color: #3f3f3f; margin: 10px 0px; padding: 0px; display: block; text-decoration: none; } .related-post .post-list .item .post_excerpt { font-size: 13px; color: #3f3f3f; margin: 10px 0px; padding: 0px; display: block; text-decoration: none; } @media only screen and (min-width: 1024px) { .related-post .post-list .item { width: 30%; } } @media only screen and (min-width: 768px) and (max-width: 1023px) { .related-post .post-list .item { width: 90%; } } @media only screen and (min-width: 0px) and (max-width: 767px) { .related-post .post-list .item { width: 90%; } }
Risques liés au renouvellement d’IPv4 : quand le manque de responsabilisation se transforme en trahison du code en cours d’exécution
La plupart des entreprises entrent sur le marché IPv4 avec un objectif simple. Elles ont besoin d’adresses. Peut-être en ont-elles besoin pour l’hébergement. Peut-être en ont-elles besoin pour une infrastructure VPN. Peut-être en ont-elles besoin pour des services cloud, des plateformes SaaS, l’expansion télécom, des systèmes e-mail, des outils de cybersécurité ou des applications destinées aux clients. Elles recherchent donc un fournisseur IPv4. Elles comparent les prix. Elles vérifientRead more Related Posts How i.lease Simplifies IPv4 Leasing Across Multiple RIR Regions In today’s Internet infrastructure economy, IPv4 address leasing has become a critical operational strategy for enterprises, cloud providers, and network Risk Placement in IPv4 Transactions: What Enterprises Should Know The IPv4 market has quietly evolved into a structured secondary asset class. As global IPv4 exhaustion continues, enterprises, ISPs, and Understanding Operational Risk in IPv4 Address Markets IPv4 has long stopped being a simple technical identifier system. It has become a constrained, priced, and operationally embedded infrastructure .related-post {} .related-post .post-list { text-align: left; } .related-post .post-list .item { margin: 5px; padding: 10px; } .related-post .headline { font-size: 18px !important; color: #999999 !important; } .related-post .post-list .item .post_thumb { max-height: 220px; margin: 10px 0px; padding: 0px; display: block; } .related-post .post-list .item .post_title { font-size: 16px; color: #3f3f3f; margin: 10px 0px; padding: 0px; display: block; text-decoration: none; } .related-post .post-list .item .post_excerpt { font-size: 13px; color: #3f3f3f; margin: 10px 0px; padding: 0px; display: block; text-decoration: none; } @media only screen and (min-width: 1024px) { .related-post .post-list .item { width: 30%; } } @media only screen and (min-width: 768px) and (max-width: 1023px) { .related-post .post-list .item { width: 90%; } } @media only screen and (min-width: 0px) and (max-width: 767px) { .related-post .post-list .item { width: 90%; } }
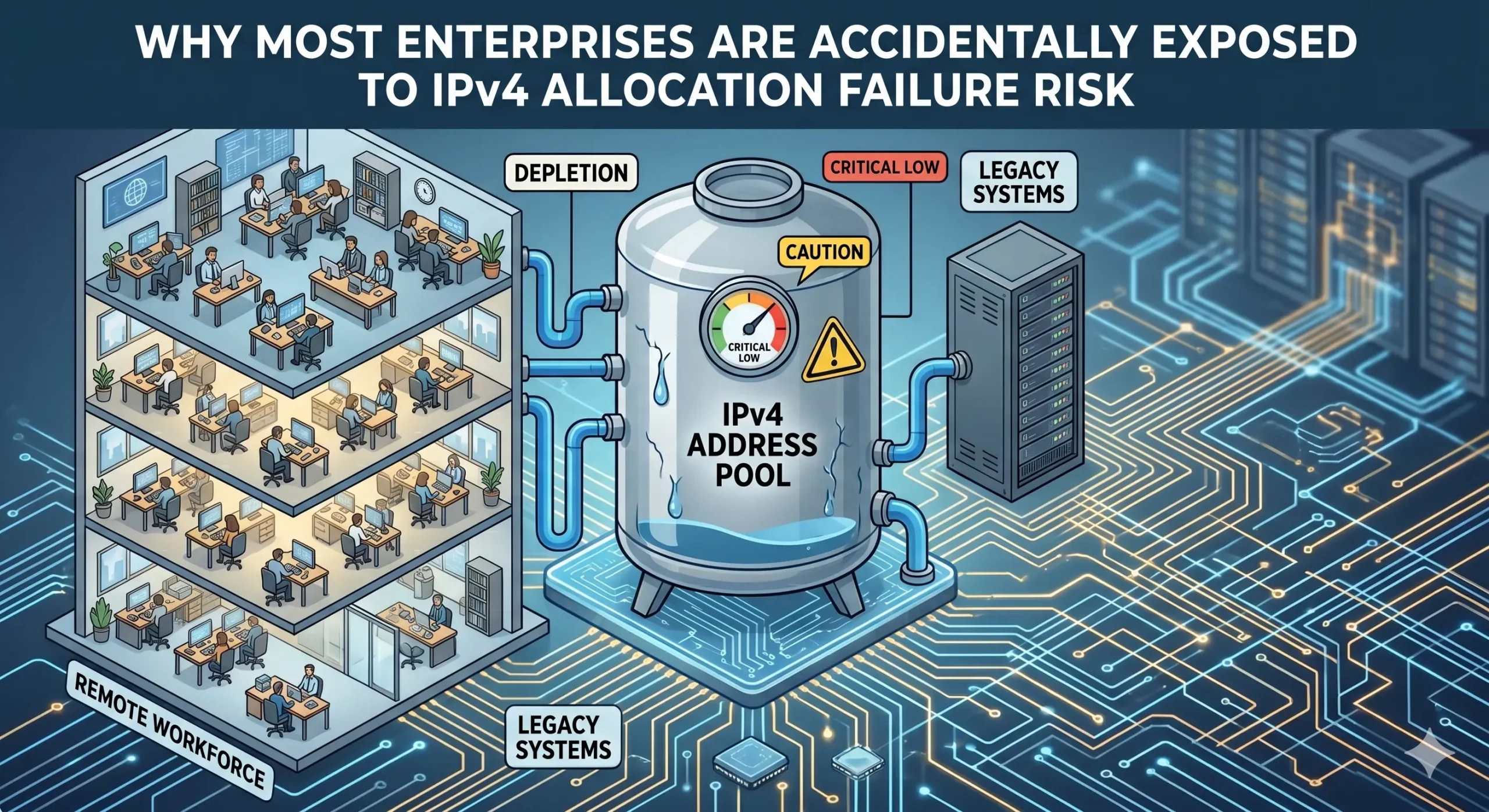
Pourquoi la plupart des entreprises sont exposées accidentellement au risque d’échec d’attribution d’adresse IPv4
La rareté de l’IPv4 est largement comprise. Ce que de nombreuses entreprises sous-estiment encore, c’est le risque de continuité lié à la manière dont les ressources d’adressage sont gouvernées et maintenues. Les entreprises maintiennent souvent une utilisation opérationnelle des ressources IPv4 sans disposer d’une visibilité complète sur les conditions de continuité qui soutiennent ces allocations. La dépendance croissante à la location, aux transferts et aux infrastructures gérées par desRead more Related Posts ¿Qué es el agotamiento de direcciones IPv4? IPv4 es la versión inicial del Protocolo de Internet (IP), capaz de generar 4.300 millones de posibles direcciones IPv4. Sin How i.lease Simplifies IPv4 Leasing Across Multiple RIR Regions In today’s Internet infrastructure economy, IPv4 address leasing has become a critical operational strategy for enterprises, cloud providers, and network Risk Placement in IPv4 Transactions: What Enterprises Should Know The IPv4 market has quietly evolved into a structured secondary asset class. As global IPv4 exhaustion continues, enterprises, ISPs, and .related-post {} .related-post .post-list { text-align: left; } .related-post .post-list .item { margin: 5px; padding: 10px; } .related-post .headline { font-size: 18px !important; color: #999999 !important; } .related-post .post-list .item .post_thumb { max-height: 220px; margin: 10px 0px; padding: 0px; display: block; } .related-post .post-list .item .post_title { font-size: 16px; color: #3f3f3f; margin: 10px 0px; padding: 0px; display: block; text-decoration: none; } .related-post .post-list .item .post_excerpt { font-size: 13px; color: #3f3f3f; margin: 10px 0px; padding: 0px; display: block; text-decoration: none; } @media only screen and (min-width: 1024px) { .related-post .post-list .item { width: 30%; } } @media only screen and (min-width: 768px) and (max-width: 1023px) { .related-post .post-list .item { width: 90%; } } @media only screen and (min-width: 0px) and (max-width: 767px) { .related-post .post-list .item { width: 90%; } }
