What Is IP Address Reputation

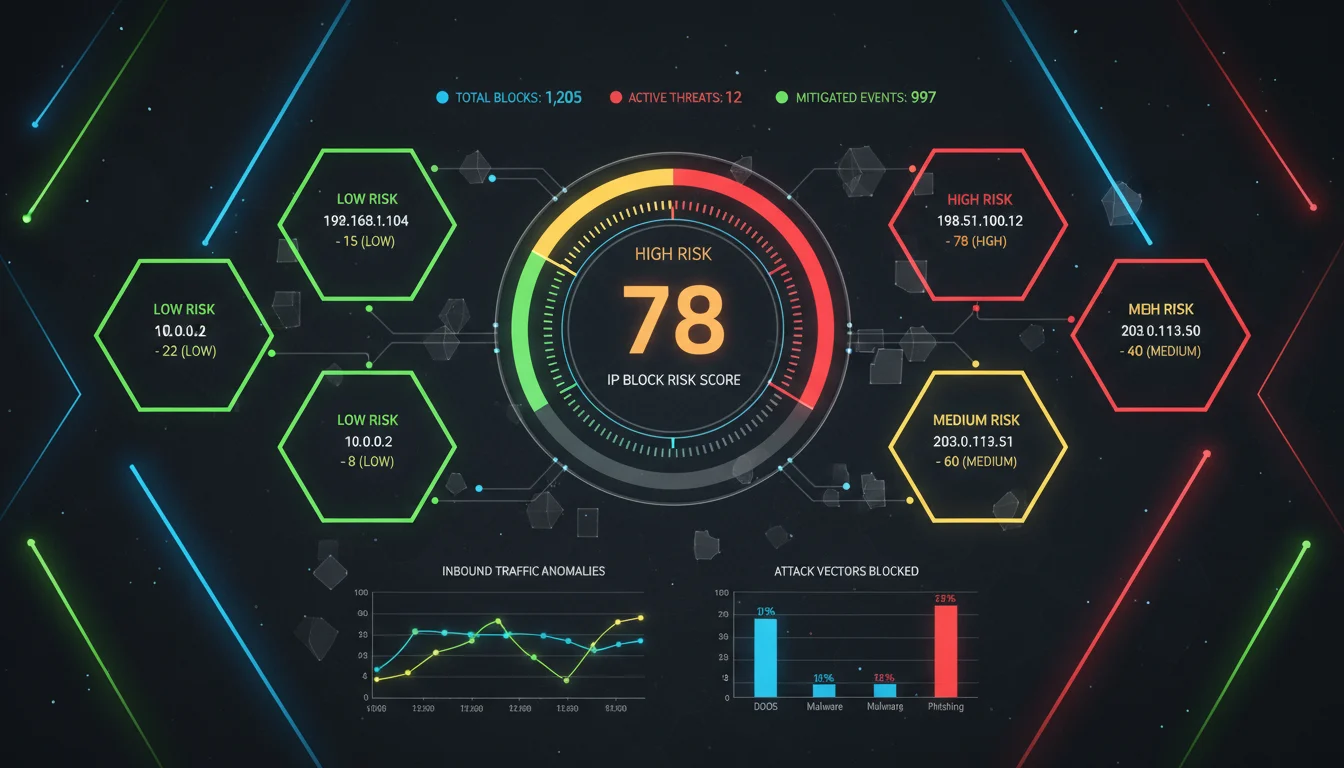
A clear comprehension of the discrepancies between IP reputation and IP risk score constitutes a critical prerequisite for effective cybersecurity governance — the former encapsulates historical trustworthiness, while the latter forecasts potential threat vulnerabilities.
Table of Contents
For instance, a clean IP will send emails that are not flagged and instead land directly in the inbox. A bad one sends emails that go to spam or never arrives. This rating also allows other websites to filter traffic. They deny requests from risky IPs. This impacts not only emails but also browsing, logins, and downloads. When an IP is marked poor, the reputation system will consider it unsafe. The traffic can be rejected or delayed. This is possible even when the user is innocent. The user IP can result from shared servers or cloud systems which have bad reputations. Because of this, reputation matters for businesses that depend on digital tools. Systems need to be kept running and business customers connected guard digital tools brand image. Also protect email marketing efforts. Building a clean reputation takes effort but losing it takes only a moment. This emphasizes the need to regularly and actively manage and monitor IP addresses.
Why IP Address Reputation Matters
When you send an email or visit a website, your IP address is shared. This address is often visible to email providers, web hosts, and security tools. These systems check the reputation of your IP before they allow access or deliver content. If your IP has a good record, your actions are accepted.
If your IP shows past issues, like spam or strange behaviour, your activity may be blocked or delayed. For email, this can mean your message goes straight to the spam folder. For websites, your connection may be denied. These checks run in the background, but they affect every online process. A clean reputation makes it easier to reach users, send newsletters, or host services. A poor reputation causes messages to fail, pages not to load, and services to stop working. Many companies lose sales when emails do not reach customers. Others see damage to their brand when users think the service is broken.
Even with strong content and secure systems, a bad IP score can break the connection. That is why businesses need to monitor their IP status often and fix issues quickly.
How Reputation Is Calculated
Reputation builds slowly through patterns seen over time. Security firms, email providers, and internet carriers watch for common warning signs. They track spam reports, failed login attempts, malware downloads, and how users react to certain content. When these signs appear often, the system takes notice. Each event adds to a bigger picture. The more signals an IP sends, the stronger the impression it leaves. These signals are sorted and measured. Many vendors use algorithms to give each IP a score. Some also assign risk labels, like “clean,” “low-risk,” or “blacklisted.” A clean IP does not cause problems. It sends regular traffic and follows rules. An IP with problems may have been used for spam or fraud. Even if the owner changes, the IP may still carry that past record.
This is why new users can inherit bad reputations without knowing. When a server or service checks an IP, it decides what to allow based on that reputation. If the score is low, the system may block or delay access. If the score is high, the request passes through. Most of these checks happen in seconds, but their results shape the entire user experience.
Key Sources of Reputation Signals
Reputation services help systems decide whether to trust or reject traffic. These services come in many forms. The most common ones are DNS-based blacklists, or DNSBLs. Mail servers use these lists every day. This stops known bad actors from reaching inboxes. Real-time blocklists, or RBLs, work in a similar way. They update more often and respond to fresh threats. Spam filters often use both DNSBLs and RBLs at once to catch more issues.
Large companies also provide their own data. Cisco tracks traffic patterns and flags suspicious activity. Microsoft monitors IPs across its cloud and email services. Akamai collects data from its global delivery network. These sources share intelligence that helps block bots, scanners, or abuse coming from infected systems. Many services use more than one source. When they combine several, they get a better idea of the IP’s behaviour. This makes the judgment more accurate. No single list sees everything, but using many helps reduce mistakes. A clean record across all of them shows strong trust. A mismatch can lead to further checks before traffic is allowed.
Role in Email Deliverability
The success rate of email delivery is largely dependent on the reputation of the IP. If you send emails using an IP with a poor reputation, your emails may be blocked or marked as spam. Large email service providers will carefully verify this information. Services such as Gmail, Outlook, Yahoo Mail, and Alibaba check the reputation of the IP. They decide if emails can reach the recipient’s inbox based on this reputation.
Senders can improve their reputation by gradually and carefully enabling new IP addresses. They must also ensure that users confirm their subscription information before sending emails. Keeping the email list clean, that is, deleting inactive or invalid addresses, is also helpful. Respecting unsubscribe requests is also very important. Sending emails in a stable and low-frequency manner can build trust over time. This stable sending method indicates to the provider that the sender is responsible and follows best practices.
This lowers the chance that emails get rejected or marked as spam. Managing the IP reputation plays a key role in successful email marketing and communication.
Maintaining a Good Reputation
To safeguard the reputation of emails, senders use trusted servers to send messages. They employ domain-based authentication methods such as SPF, DKIM, and DMARC. These methods can prove that the emails come from authorized sources.
Monitoring the blacklist status is important. It helps detect issues early. Early detection allows fixing problems before they cause harm. Using IP rotation requires caution. Moving to a new IP with a bad reputation can bring trouble. Therefore, careful checks are needed before switching IPs. This way, senders avoid inheriting a poor reputation from other users.Switching to an IP address with a poor reputation may damage trust. Network operators play a crucial role in protecting the system by preventing open relaying. They must ensure the security of their systems to prevent abuse and spam. If the system is open, spam senders may take advantage of it, which can damage the reputation.
Keeping the email list clean is another key step. Deleting inactive or invalid addresses can reduce the rejection rate and complaint rate. Combining proactive security measures with careful list management can build a strong reputation over time. Sending users who follow these practices reduce the risk of being blocked or labeled as spam. Maintaining a good IP reputation requires the continuous attention of technical teams and marketers. Such efforts help ensure that emails can reach their intended recipients.
Consequences of Poor Reputation
An IP with a poor reputation is often blocked by email services or websites. Users may see prompts such as “Connection Denied”, receive security warnings, or encounter timeout issues when attempting to connect. For businesses, these problems can cause serious issues. Customer acquisition efforts will fail because emails cannot reach the inbox. Online sales will slow down because users cannot access the website normally. Brand trust will drop significantly as users become frustrated. In industries such as banking or healthcare, blocked IPs may prevent key business operations.
Systems may not be able to communicate or process transactions in a timely manner. Repairing the damaged reputation of an IP requires a long time and a lot of work. Removing an IP from the blocked list requires contacting multiple services and proving that the problem has been resolved. This process typically involves checking for malware, improving security, and changing sending habits. Even with these measures, improving the reputation may take weeks or months. During this period, enterprises must closely monitor their networks to avoid further damage. Before the IP reputation is restored, the risk of lost revenue and damaged relationships remains high.An IP with a poor reputation can disrupt email delivery, block website access, and undermine customer trust. For businesses, this translates into lost revenue, failed customer acquisition, and operational bottlenecks—especially in sensitive industries like banking and healthcare. Repairing a damaged IP reputation is a time-consuming process involving malware removal, strengthened security, and improved sending practices. Even then, it can take weeks or months to fully restore trust, during which careful monitoring is essential to prevent further losses.
-Dr. Evelyn Shaw, Cybersecurity and Network Infrastructure Specialist
Recovering from Reputation Damage
Recovery begins when you find the root cause of the issue. The problem could be malware infections, spam abuse, or incorrect system settings. You must then clean your systems thoroughly. This means patching servers to fix security holes. You also need to stop any ongoing attacks quickly.
Revoking compromised credentials is necessary to block attackers. Removing bad actors prevents further harm. After fixing the problems, you can ask blacklist operators to remove your IP from their lists. Usually, you must wait for a certain time before making this request. During this waiting period, email providers watch your behaviour carefully. They check if you follow safe and trusted practices again. Keeping good system settings helps avoid new problems. Sending emails steadily, without sudden increases, shows responsibility. Getting recipients to open and interact with your emails helps improve your reputation. Doing this slowly rebuilds your IP’s trust score. You need to check your systems often. You should make changes when needed to keep a strong reputation.
Regular monitoring finds problems early. It also keeps your communication working smoothly. This ongoing care makes sure your IP remains reliable and trusted by others.

How Cloud Infrastructure Affects IP Reputation
Today’s cloud providers like AWS, Azure, and Google Cloud have a big impact on IP reputation. They offer flexible ways to assign IP addresses to users. Sometimes, they label certain IP ranges as “high risk” because of past misuse. When users get new IP addresses, these might start as “clean.”
However, if the subnet is shared, bad behaviour from others can hurt the whole range’s reputation. Cloud users need to watch this closely. They should use dedicated IP addresses whenever possible to avoid problems. It helps to keep virtual machines clean and remove any that cause issues. Monitoring changes in IP reputation is also important. This way, users can react fast if their IP gets a poor rating. Managing reputation in the cloud requires constant attention and careful steps to protect business operations and communications.
In today’s cloud landscape, providers like AWS, Azure, and Google Cloud shape the reputation of IP addresses. While new IPs can start 'clean,' shared subnets mean the missteps of one user can impact many. To protect business operations, cloud users should prioritize dedicated IPs, maintain clean virtual machines, and actively monitor reputation shifts. Effective IP reputation management in the cloud demands vigilance, proactive measures, and continuous attention
– Alex Mercer, Cloud Security Specialist
Real-World Cases and Studies
Research groups and email teams watch reputation trends closely. A university found more than 5,000 IP addresses was listed on its DNS blacklist following a security breach in 2023. It showed how quickly a problem can spread across networks. Another company moved its email service to a clean subnet. After that, their daily bounce rates dropped to below 5 percent. This change helped improve email delivery and customer reach. Email marketers have noticed similar results. When they send emails from dedicated IPs that they manage carefully, open rates often rise by 10 to 20 percent. These numbers prove that reputation matters for marketing success. Studies also show that removing an IP from real-time blocklists usually takes between 30 and 90 days of clean activity after fixing the issues. This period allows providers to confirm that problems have stopped. It also helps rebuild trust in the IP. These findings highlight how important it is to keep IP addresses clean and secure over time.
Frequently Asked Questions
1. What is IP address reputation and why does it matter?
IP address reputation is a measure of how much networks and services trust an IP address. It affects whether emails reach inboxes, websites load properly, or connections are allowed. A good reputation helps ensure smooth online communication and business operations.
2. How is IP reputation calculated?
Reputation is based on data collected over time, such as spam reports, malware distribution, login attempts, and user feedback. Security vendors and internet providers use this data to score or label IP addresses as clean, risky, or blacklisted.
3. How does IP reputation impact email delivery?
Email providers check the reputation of sending IPs before delivering messages. Poor reputation can cause emails to be blocked or sent to spam. Maintaining good practices like warming up IPs, cleaning mailing lists, and authenticating emails improves deliverability.
4. What causes an IP address to get a bad reputation?
An IP may get a bad reputation due to spam sending, malware infections, abuse from shared servers, or misconfigured systems. Sometimes new users inherit poor reputation if the IP was previously misused.
5. How can businesses recover a damaged IP reputation?
Recovery starts by identifying and fixing the cause of the problem, such as removing malware or stopping spam. After cleanup, businesses request removal from blacklists and rebuild trust through steady, responsible sending and regular monitoring.
Related Blogs
Related Posts
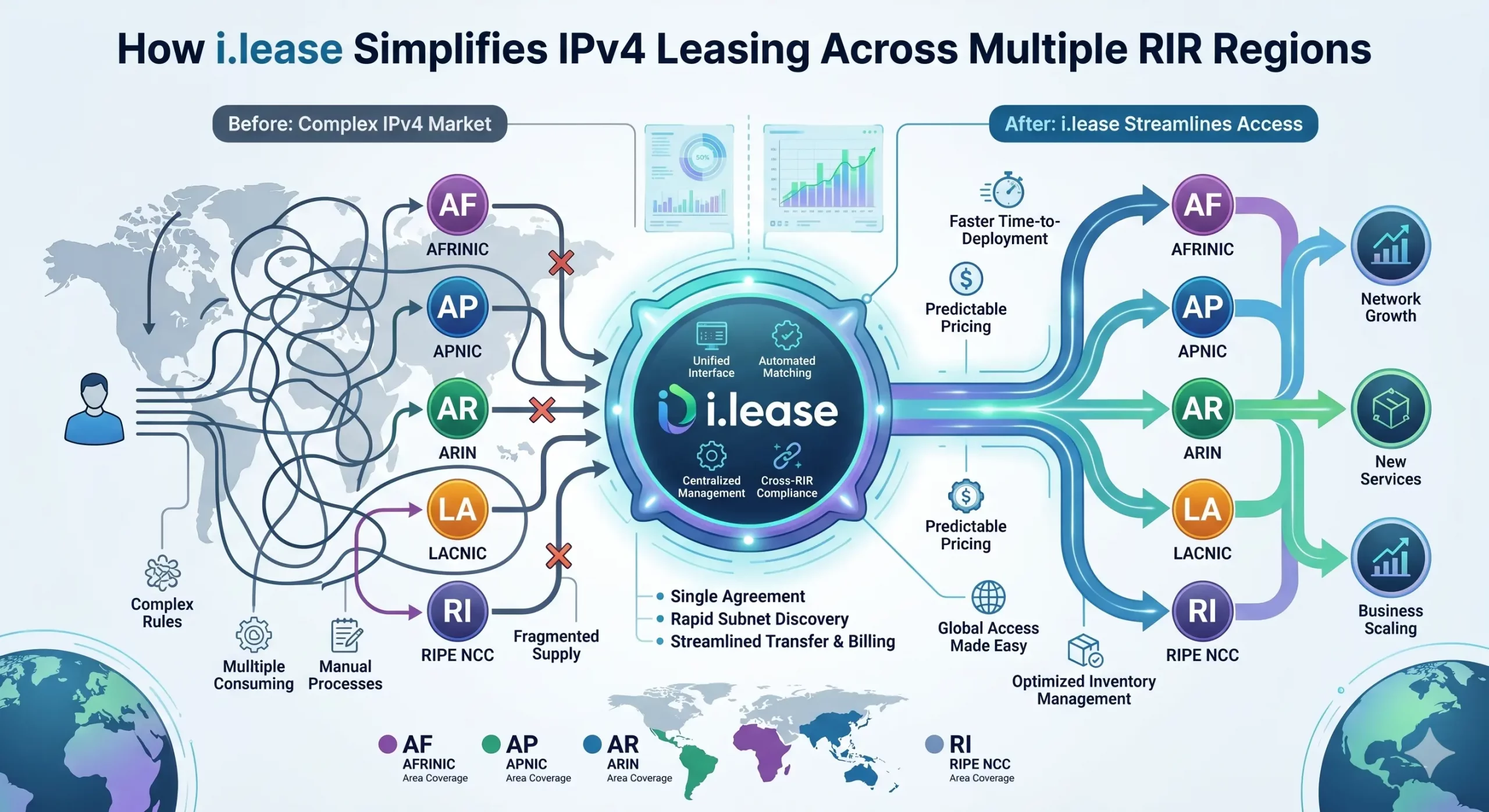
How i.lease Simplifies IPv4 Leasing Across Multiple RIR Regions
In today’s Internet infrastructure economy, IPv4 address leasing has become a critical operational strategy for enterprises, cloud providers, and network operators facing persistent address scarcity. As IPv4 exhaustion continues across all five Regional Internet Registries (RIRs)—ARIN, RIPE NCC, APNIC, LACNIC, and AFRINIC—the need for structured, compliant, and cross-regional leasing solutions has never been greater. However, beneath the surface of what appears to be a simple “supply-and-demand” market lies aRead more Related Posts How i.lease Simplifies IPv4 Leasing Across Multiple RIR Regions In today’s Internet infrastructure economy, IPv4 address leasing has become a critical operational strategy for enterprises, cloud providers, and network Understanding Operational Risk in IPv4 Address Markets IPv4 has long stopped being a simple technical identifier system. It has become a constrained, priced, and operationally embedded infrastructure Por qué la mayoría de las empresas están expuestas accidentalmente al riesgo de fallo en la asignación de IPv4 La escasez de IPv4 es ampliamente comprendida. Lo que muchas empresas aún subestiman es el riesgo de continuidad relacionado con .related-post {} .related-post .post-list { text-align: left; } .related-post .post-list .item { margin: 5px; padding: 10px; } .related-post .headline { font-size: 18px !important; color: #999999 !important; } .related-post .post-list .item .post_thumb { max-height: 220px; margin: 10px 0px; padding: 0px; display: block; } .related-post .post-list .item .post_title { font-size: 16px; color: #3f3f3f; margin: 10px 0px; padding: 0px; display: block; text-decoration: none; } .related-post .post-list .item .post_excerpt { font-size: 13px; color: #3f3f3f; margin: 10px 0px; padding: 0px; display: block; text-decoration: none; } @media only screen and (min-width: 1024px) { .related-post .post-list .item { width: 30%; } } @media only screen and (min-width: 768px) and (max-width: 1023px) { .related-post .post-list .item { width: 90%; } } @media only screen and (min-width: 0px) and (max-width: 767px) { .related-post .post-list .item { width: 90%; } }
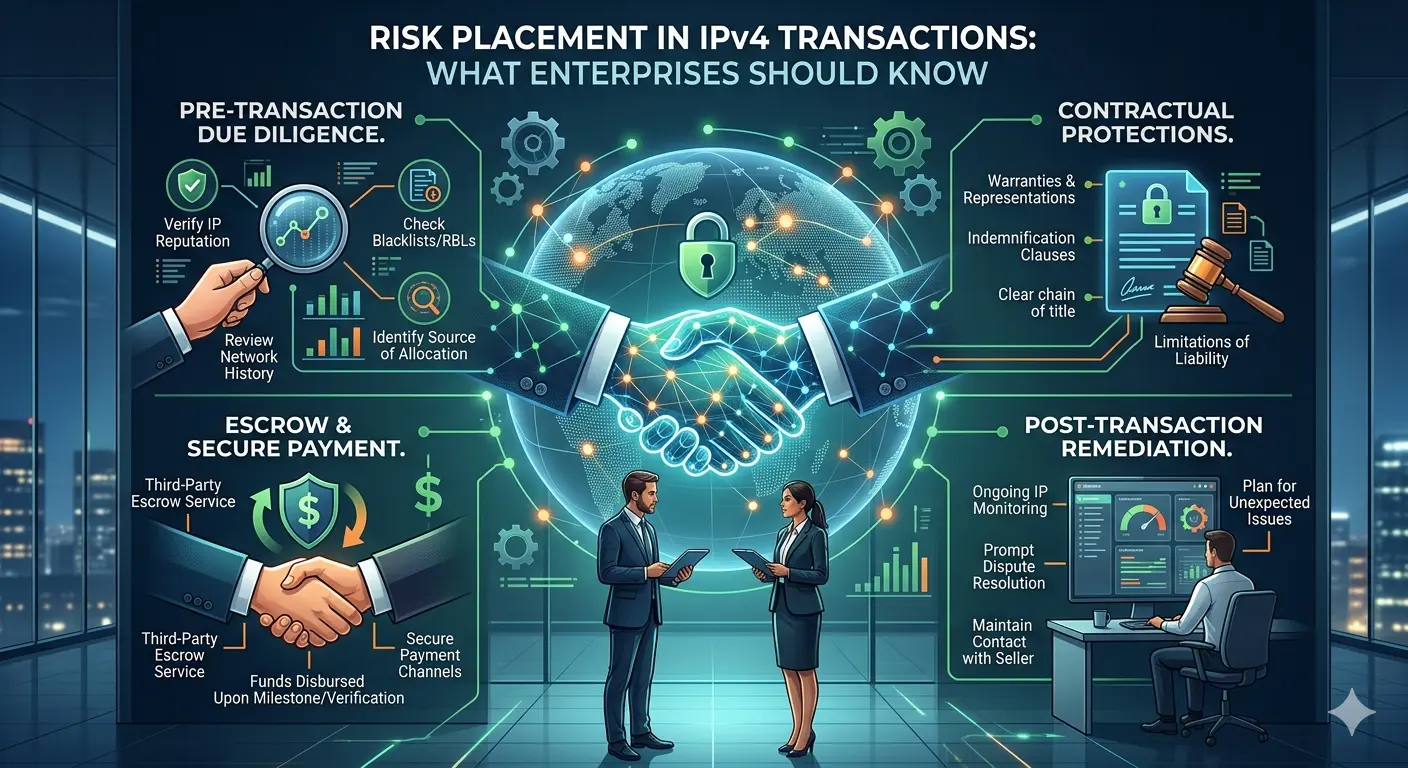
Risk Placement in IPv4 Transactions: What Enterprises Should Know
The IPv4 market has quietly evolved into a structured secondary asset class. As global IPv4 exhaustion continues, enterprises, ISPs, and brokers now routinely engage in buying, leasing, and transferring IPv4 address blocks. Alongside this growth, one topic has become increasingly important—but still under-discussed: risk placement in IPv4 transactions. For organizations participating in this market, especially through platforms such as i.lease, understanding how risk is identified, allocated, and mitigated isRead more Related Posts How i.lease Simplifies IPv4 Leasing Across Multiple RIR Regions In today’s Internet infrastructure economy, IPv4 address leasing has become a critical operational strategy for enterprises, cloud providers, and network Understanding Operational Risk in IPv4 Address Markets IPv4 has long stopped being a simple technical identifier system. It has become a constrained, priced, and operationally embedded infrastructure Por qué la mayoría de las empresas están expuestas accidentalmente al riesgo de fallo en la asignación de IPv4 La escasez de IPv4 es ampliamente comprendida. Lo que muchas empresas aún subestiman es el riesgo de continuidad relacionado con .related-post {} .related-post .post-list { text-align: left; } .related-post .post-list .item { margin: 5px; padding: 10px; } .related-post .headline { font-size: 18px !important; color: #999999 !important; } .related-post .post-list .item .post_thumb { max-height: 220px; margin: 10px 0px; padding: 0px; display: block; } .related-post .post-list .item .post_title { font-size: 16px; color: #3f3f3f; margin: 10px 0px; padding: 0px; display: block; text-decoration: none; } .related-post .post-list .item .post_excerpt { font-size: 13px; color: #3f3f3f; margin: 10px 0px; padding: 0px; display: block; text-decoration: none; } @media only screen and (min-width: 1024px) { .related-post .post-list .item { width: 30%; } } @media only screen and (min-width: 768px) and (max-width: 1023px) { .related-post .post-list .item { width: 90%; } } @media only screen and (min-width: 0px) and (max-width: 767px) { .related-post .post-list .item { width: 90%; } }
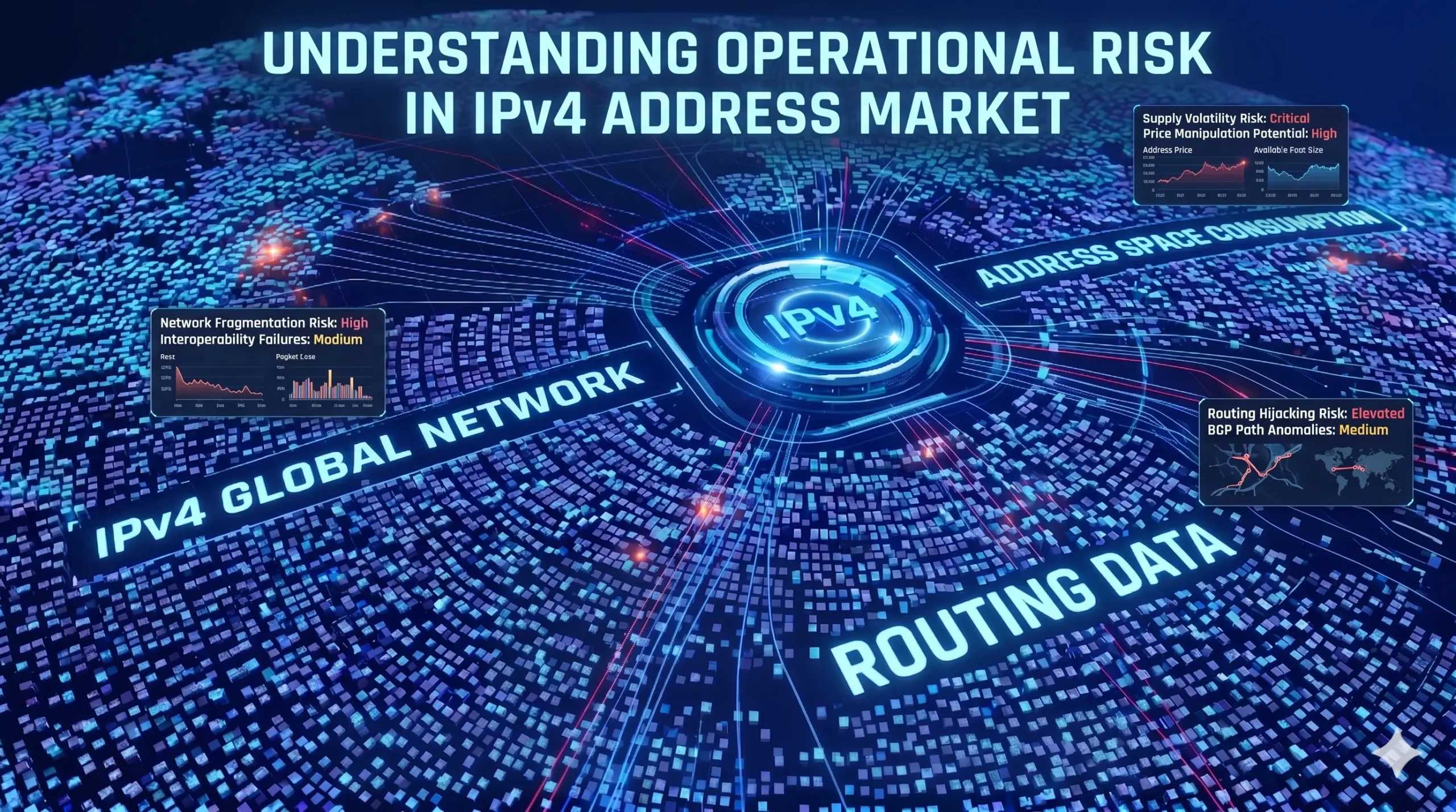
Understanding Operational Risk in IPv4 Address Markets
IPv4 has long stopped being a simple technical identifier system. It has become a constrained, priced, and operationally embedded infrastructure asset class. “In the IPv4 market, execution is not paperwork. Execution is continuity under registry-layer uncertainty.”https://heng.lu/on-why-i-lease-exists-and-why-the-broker-question-is-really-a-registry-risk-question/ Yet most of the industry still speaks about it as if it were a straightforward marketplace problem: buyers, sellers, brokers, escrow, transfer, done. That framing is increasingly outdated. The real structure of riskRead more Related Posts How i.lease Simplifies IPv4 Leasing Across Multiple RIR Regions In today’s Internet infrastructure economy, IPv4 address leasing has become a critical operational strategy for enterprises, cloud providers, and network Understanding Operational Risk in IPv4 Address Markets IPv4 has long stopped being a simple technical identifier system. It has become a constrained, priced, and operationally embedded infrastructure Por qué la mayoría de las empresas están expuestas accidentalmente al riesgo de fallo en la asignación de IPv4 La escasez de IPv4 es ampliamente comprendida. Lo que muchas empresas aún subestiman es el riesgo de continuidad relacionado con .related-post {} .related-post .post-list { text-align: left; } .related-post .post-list .item { margin: 5px; padding: 10px; } .related-post .headline { font-size: 18px !important; color: #999999 !important; } .related-post .post-list .item .post_thumb { max-height: 220px; margin: 10px 0px; padding: 0px; display: block; } .related-post .post-list .item .post_title { font-size: 16px; color: #3f3f3f; margin: 10px 0px; padding: 0px; display: block; text-decoration: none; } .related-post .post-list .item .post_excerpt { font-size: 13px; color: #3f3f3f; margin: 10px 0px; padding: 0px; display: block; text-decoration: none; } @media only screen and (min-width: 1024px) { .related-post .post-list .item { width: 30%; } } @media only screen and (min-width: 768px) and (max-width: 1023px) { .related-post .post-list .item { width: 90%; } } @media only screen and (min-width: 0px) and (max-width: 767px) { .related-post .post-list .item { width: 90%; } }
