The Potential Risks of Using Public IP Addresses (Part 1)

Public IP addresses allow devices to communicate directly with the internet, but they also come with several risks that can jeopardize security and privacy. This article explores the potential dangers associated with using public IP addresses and offers tips on how to mitigate these risks in Part 2
Table of Contents
What is a public IP address?
A public IP address is an address that is accessible over the internet. It is assigned by an Internet Service Provider (ISP) and can be used by any device connected to the Internet to communicate with other devices. Unlike private IP addresses, which are used within a local network and are not accessible from outside, public IP addresses are visible to everyone on the internet.
Potential Risks of Public IP Addresses
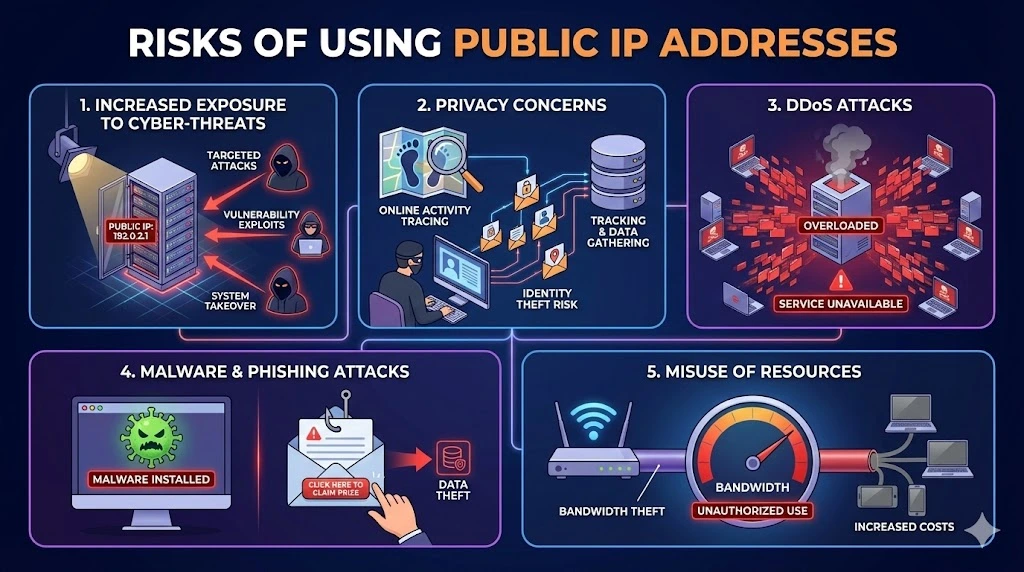
Increased Exposure to Cyber-threats
One of the primary risks of using public IP addresses is increased exposure to cyber threats. Since public IP addresses are accessible over the internet, they can be targeted by hackers who use various methods to exploit vulnerabilities. This can lead to unauthorized access to sensitive information, data breaches, and even complete system takeovers.
Privacy Concerns
Public IP addresses can be tracked and monitored, leading to significant privacy concerns. Malicious actors can use public IP addresses to trace online activities, gather personal information, and even pinpoint physical locations. This information can be used for identity theft, stalking, or other malicious purposes.
Distributed Denial of Service (DDoS) Attacks
Public IP addresses are often the target of distributed denial of service (DDoS) attacks. In a DDoS attack, multiple compromised systems flood a target system with traffic, overwhelming it and causing it to become unavailable. These attacks can disrupt business operations, cause financial losses, and damage reputations.
Malware and Phishing Attacks
Devices with public IP addresses are more susceptible to malware and phishing attacks. Hackers can exploit vulnerabilities to install malware on a device, which can then be used to steal data, monitor activities, or launch further attacks. Phishing attacks, where attackers trick individuals into providing sensitive information, are more likely when public IP addresses are involved.
Misuse of Resources
When using public IP addresses, there is a risk that unauthorized users can misuse your network resources. This can include bandwidth theft, where others use your internet connection without permission, leading to slower internet speeds and increased costs.
Summary of The Article
While public IP addresses are necessary for certain internet functionalities, they come with inherent risks. By understanding these risks and implementing appropriate security measures, individuals and organizations can protect themselves from potential threats and ensure their online activities remain secure.
Discover the potential risks of using public IP addresses and learn how to protect your network from cyber attacks, privacy breaches, and other threats. Taking proactive steps to safeguard public IP addresses is essential in today’s digital landscape. Stay tuned for part 2!
Trusted IPv4 Leasing for Business Growth
Get enterprise-grade IPv4 space quickly, with seamless deployment and end-to-end management.
Get Started with i.leaseFAQs
Can someone find my exact location from my Public IP address?
Not your exact street address. A Public IP address typically reveals your approximate location (Country, City, and ISP). However, legal authorities can subpoena your ISP to reveal your exact physical address and identity if illegal activity is suspected.
Is it safer to use a Static or Dynamic Public IP address?
A Dynamic IP (which changes periodically) is generally considered slightly safer for home users because it makes it harder for hackers to target you consistently over time. Static IPs are easier to target but are often necessary for businesses hosting servers or CCTV systems.
Can I change my Public IP address to stop an attack?
Yes. If you have a Dynamic IP, simply unplugging your modem/router for 5-10 minutes (or sometimes overnight) is often enough to get assigned a new IP address by your ISP. If you have a Static IP, you must contact your ISP and request a change due to security concerns.
Related Posts
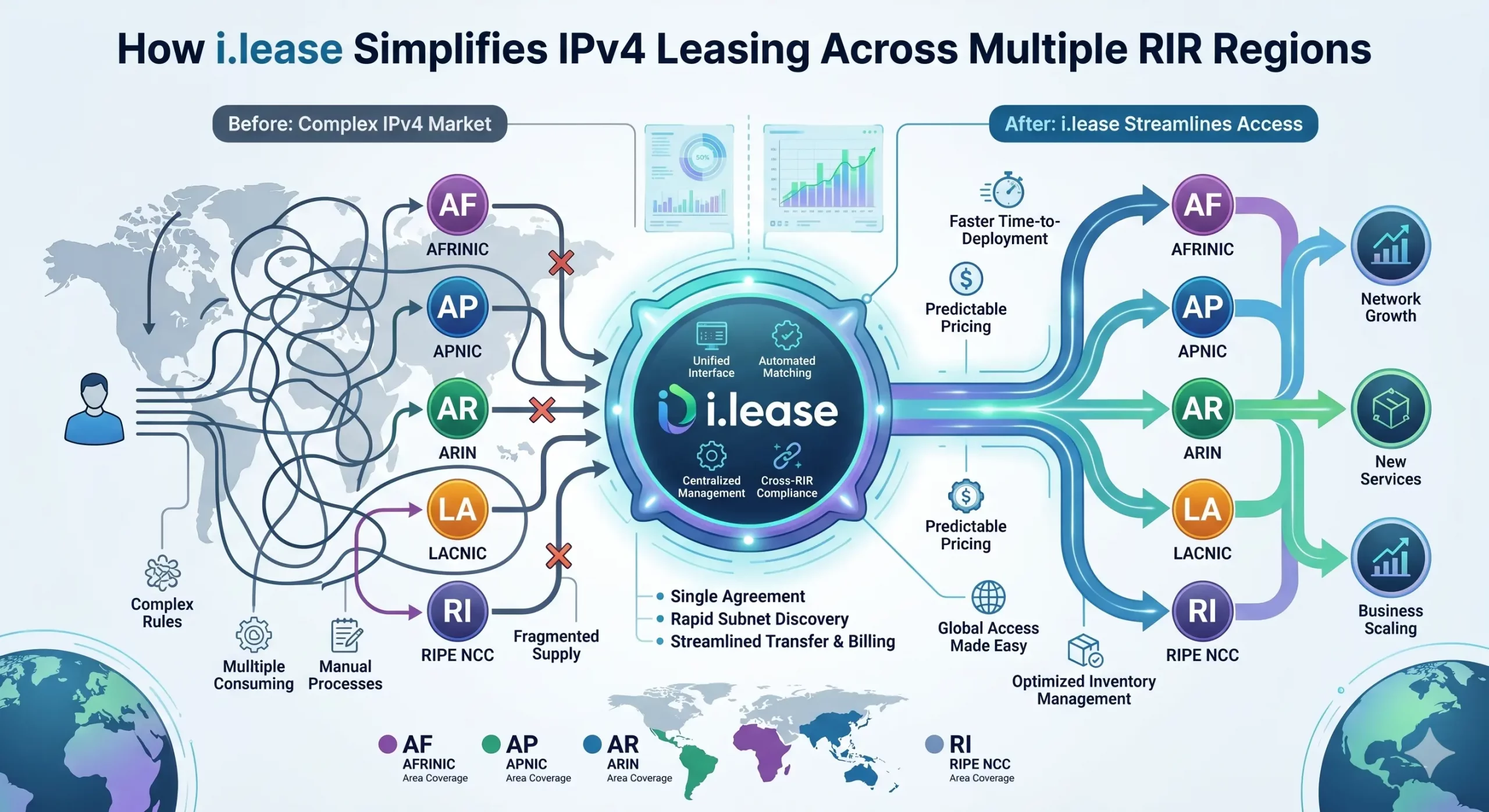
How i.lease Simplifies IPv4 Leasing Across Multiple RIR Regions
In today’s Internet infrastructure economy, IPv4 address leasing has become a critical operational strategy for enterprises, cloud providers, and network operators facing persistent address scarcity. As IPv4 exhaustion continues across all five Regional Internet Registries (RIRs)—ARIN, RIPE NCC, APNIC, LACNIC, and AFRINIC—the need for structured, compliant, and cross-regional leasing solutions has never been greater. However, beneath the surface of what appears to be a simple “supply-and-demand” market lies aRead more Related Posts How i.lease Simplifies IPv4 Leasing Across Multiple RIR Regions In today’s Internet infrastructure economy, IPv4 address leasing has become a critical operational strategy for enterprises, cloud providers, and network Why Malaysia Is Becoming a Data Centre Hub for Cloud and AI Infrastructure Malaysia is becoming one of Southeast Asia’s most important data centre growth markets. Demand for cloud computing, artificial intelligence, enterprise Understanding Operational Risk in IPv4 Address Markets IPv4 has long stopped being a simple technical identifier system. It has become a constrained, priced, and operationally embedded infrastructure .related-post {} .related-post .post-list { text-align: left; } .related-post .post-list .item { margin: 5px; padding: 10px; } .related-post .headline { font-size: 18px !important; color: #999999 !important; } .related-post .post-list .item .post_thumb { max-height: 220px; margin: 10px 0px; padding: 0px; display: block; } .related-post .post-list .item .post_title { font-size: 16px; color: #3f3f3f; margin: 10px 0px; padding: 0px; display: block; text-decoration: none; } .related-post .post-list .item .post_excerpt { font-size: 13px; color: #3f3f3f; margin: 10px 0px; padding: 0px; display: block; text-decoration: none; } @media only screen and (min-width: 1024px) { .related-post .post-list .item { width: 30%; } } @media only screen and (min-width: 768px) and (max-width: 1023px) { .related-post .post-list .item { width: 90%; } } @media only screen and (min-width: 0px) and (max-width: 767px) { .related-post .post-list .item { width: 90%; } }

Why Malaysia Is Becoming a Data Centre Hub for Cloud and AI Infrastructure
Malaysia is becoming one of Southeast Asia’s most important data centre growth markets. Demand for cloud computing, artificial intelligence, enterprise applications, digital payments, e-commerce, cybersecurity, and low-latency regional services is pushing companies to build more infrastructure closer to users. This growth is not only based on hype. Malaysia has attracted large-scale investment from global technology companies, cloud providers, AI infrastructure operators, and hyperscale data centre developers. According to MIDA’sRead more Related Posts How i.lease Simplifies IPv4 Leasing Across Multiple RIR Regions In today’s Internet infrastructure economy, IPv4 address leasing has become a critical operational strategy for enterprises, cloud providers, and network Why Malaysia Is Becoming a Data Centre Hub for Cloud and AI Infrastructure Malaysia is becoming one of Southeast Asia’s most important data centre growth markets. Demand for cloud computing, artificial intelligence, enterprise Understanding Operational Risk in IPv4 Address Markets IPv4 has long stopped being a simple technical identifier system. It has become a constrained, priced, and operationally embedded infrastructure .related-post {} .related-post .post-list { text-align: left; } .related-post .post-list .item { margin: 5px; padding: 10px; } .related-post .headline { font-size: 18px !important; color: #999999 !important; } .related-post .post-list .item .post_thumb { max-height: 220px; margin: 10px 0px; padding: 0px; display: block; } .related-post .post-list .item .post_title { font-size: 16px; color: #3f3f3f; margin: 10px 0px; padding: 0px; display: block; text-decoration: none; } .related-post .post-list .item .post_excerpt { font-size: 13px; color: #3f3f3f; margin: 10px 0px; padding: 0px; display: block; text-decoration: none; } @media only screen and (min-width: 1024px) { .related-post .post-list .item { width: 30%; } } @media only screen and (min-width: 768px) and (max-width: 1023px) { .related-post .post-list .item { width: 90%; } } @media only screen and (min-width: 0px) and (max-width: 767px) { .related-post .post-list .item { width: 90%; } }
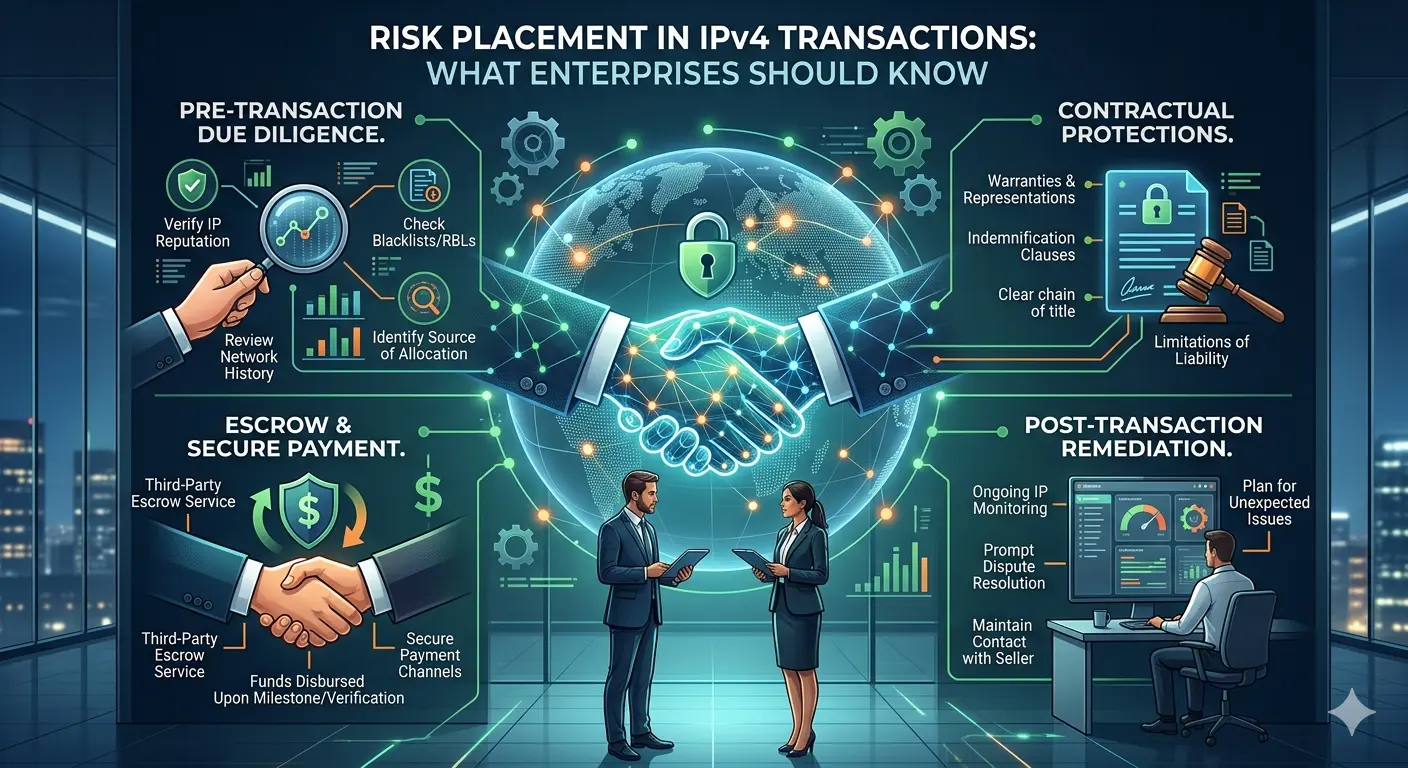
Risk Placement in IPv4 Transactions: What Enterprises Should Know
The IPv4 market has quietly evolved into a structured secondary asset class. As global IPv4 exhaustion continues, enterprises, ISPs, and brokers now routinely engage in buying, leasing, and transferring IPv4 address blocks. Alongside this growth, one topic has become increasingly important—but still under-discussed: risk placement in IPv4 transactions. For organizations participating in this market, especially through platforms such as i.lease, understanding how risk is identified, allocated, and mitigated isRead more Related Posts How i.lease Simplifies IPv4 Leasing Across Multiple RIR Regions In today’s Internet infrastructure economy, IPv4 address leasing has become a critical operational strategy for enterprises, cloud providers, and network Why Malaysia Is Becoming a Data Centre Hub for Cloud and AI Infrastructure Malaysia is becoming one of Southeast Asia’s most important data centre growth markets. Demand for cloud computing, artificial intelligence, enterprise Understanding Operational Risk in IPv4 Address Markets IPv4 has long stopped being a simple technical identifier system. It has become a constrained, priced, and operationally embedded infrastructure .related-post {} .related-post .post-list { text-align: left; } .related-post .post-list .item { margin: 5px; padding: 10px; } .related-post .headline { font-size: 18px !important; color: #999999 !important; } .related-post .post-list .item .post_thumb { max-height: 220px; margin: 10px 0px; padding: 0px; display: block; } .related-post .post-list .item .post_title { font-size: 16px; color: #3f3f3f; margin: 10px 0px; padding: 0px; display: block; text-decoration: none; } .related-post .post-list .item .post_excerpt { font-size: 13px; color: #3f3f3f; margin: 10px 0px; padding: 0px; display: block; text-decoration: none; } @media only screen and (min-width: 1024px) { .related-post .post-list .item { width: 30%; } } @media only screen and (min-width: 768px) and (max-width: 1023px) { .related-post .post-list .item { width: 90%; } } @media only screen and (min-width: 0px) and (max-width: 767px) { .related-post .post-list .item { width: 90%; } }
