互联网审查与防火长城:理解数字世界的边界
互联网彻底改变了我们连接、学习和分享信息的方式,但其开放性也引发了有关控制、隐私和自由的重大争论。
Table of Contents
这些讨论的核心是互联网审查的概念,其中最引人注目的是中国的 “防火长城”(GFW)。本文探讨了互联网审查的复杂性、其实施以及 “防火长城 ”背后的技术。
什么是互联网审查?
互联网审查是指控制或禁止访问互联网上的信息。政府、私人组织或其他监管机构可实施审查,限制用户可获取的内容。这包括封锁特定网站、过滤搜索结果或监控在线活动。
为什么要实施互联网审查?
实施互联网审查的原因因国家、意识形态和环境而异。常见的动机包括
1) 国家安全: 保护敏感的政府数据,防止错误信息或极端主义宣传的传播。
2) 文化保护: 通过限制访问不恰当或令人反感的内容来维护文化规范。
3) 政治目的: 通过限制获取政治敏感信息来控制异议和反对派。
4) 经济保护: 通过限制外国公司的竞争来支持本地企业。
5) 道德和伦理关切: 封杀与色情、吸毒或其他有害社会的内容。
尽管支持者认为审查制度对维护社会秩序至关重要,但批评者认为它侵犯了言论自由和获取信息的权利。
什么是防火长城?
长城防火墙的正式名称为 “金盾工程”,是中国复杂的互联网审查系统。长城防火墙于 2000 年代初实施,旨在监管信息流动,控制与政府政策和意识形态相冲突的国际网站和服务的访问。
长城防火墙的主要功能包括:
- 阻止访问谷歌、Facebook 和 Twitter 等热门网站。
- 限制批评中国政府的外国新闻机构和平台。
- 监控和过滤用户活动,确保遵守当地法律。
互联网审查是如何实施的?
互联网审查涉及技术措施和监管政策的结合。以下是主要方法:
- IP 拦截: 防止访问链接到受限网站的特定 IP 地址。
- DNS 过滤和重定向: 更改域名系统(DNS)请求,误导试图访问受限网站的用户。
- 关键词过滤: 监控并过滤搜索查询、电子邮件或社交媒体帖子中的特定关键词。
- 深度数据包检测(DPI): 分析数据包,识别并阻止受限内容。
- 节流: 降低某些网站或服务的网速,使其几乎无法访问。
- 执行法规: 强制互联网服务提供商(ISP)和平台遵守审查法律。
防火长城如何运作?
长城防火墙先进地融合了上述技术,并通过人工智能(AI)和机器学习技术加以强化。下面是它的功能原理:
- 网络监控: 中国政府通过 DPI 监控流量,允许当局阻止或限制与受限网站的连接。
- URL 过滤: 将特定 URL 或域列入黑名单,防止用户访问。
- 关键词监控: 标记并阻止含有敏感关键词的内容,从而影响搜索引擎和社交媒体平台。
- VPN 检测和拦截: 虚拟专用网络(VPN)通常用于绕过审查制度,通过先进的算法进行检测和禁用。
- 与本地公司合作: 微信和百度等国内平台在严格的监管准则下运营,在内部执行审查制度。
结语
互联网审查和 “长城防火墙 ”体现了监管数字空间的复杂性。尽管审查制度旨在实现国家安全和文化保护等目标,但它往往会引发有关言论自由和信息获取的伦理问题。
尤其是 “长城防火墙”,它展示了如何利用技术来控制网络叙事,从而创建一个受到严格监控和过滤的互联网生态系统。
Related Posts
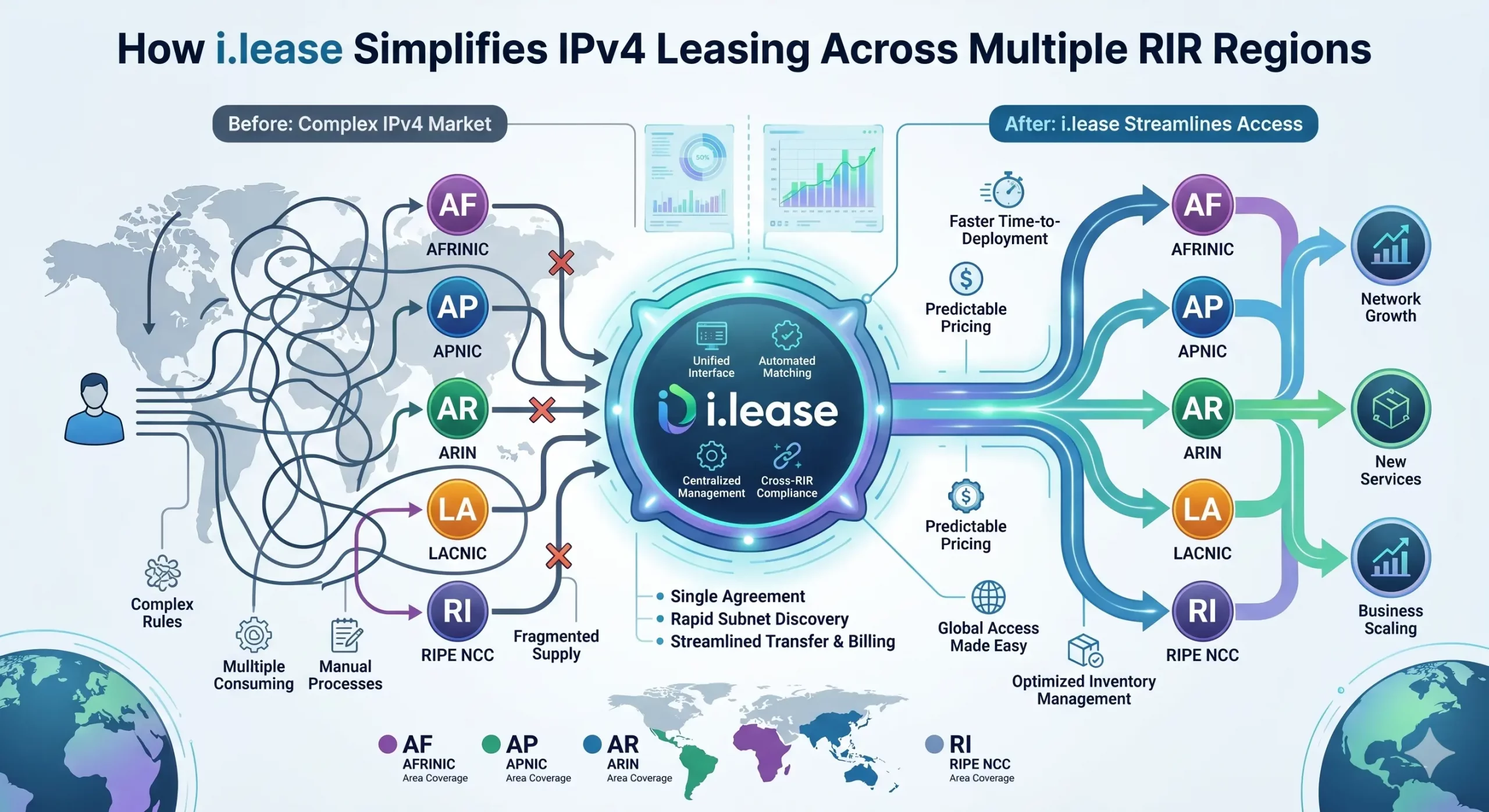
How i.lease Simplifies IPv4 Leasing Across Multiple RIR Regions
In today’s Internet infrastructure economy, IPv4 address leasing has become a critical operational strategy for enterprises, cloud providers, and network operators facing persistent address scarcity. As IPv4 exhaustion continues across all five Regional Internet Registries (RIRs)—ARIN, RIPE NCC, APNIC, LACNIC, and AFRINIC—the need for structured, compliant, and cross-regional leasing solutions has never been greater. However, beneath the surface of what appears to be a simple “supply-and-demand” market lies aRead more Related Posts Risk Placement in IPv4 Transactions: What Enterprises Should Know The IPv4 market has quietly evolved into a structured secondary asset class. As global IPv4 exhaustion continues, enterprises, ISPs, and Understanding Operational Risk in IPv4 Address Markets IPv4 has long stopped being a simple technical identifier system. It has become a constrained, priced, and operationally embedded infrastructure Por qué la mayoría de las empresas están expuestas accidentalmente al riesgo de fallo en la asignación de IPv4 La escasez de IPv4 es ampliamente comprendida. Lo que muchas empresas aún subestiman es el riesgo de continuidad relacionado con .related-post {} .related-post .post-list { text-align: left; } .related-post .post-list .item { margin: 5px; padding: 10px; } .related-post .headline { font-size: 18px !important; color: #999999 !important; } .related-post .post-list .item .post_thumb { max-height: 220px; margin: 10px 0px; padding: 0px; display: block; } .related-post .post-list .item .post_title { font-size: 16px; color: #3f3f3f; margin: 10px 0px; padding: 0px; display: block; text-decoration: none; } .related-post .post-list .item .post_excerpt { font-size: 13px; color: #3f3f3f; margin: 10px 0px; padding: 0px; display: block; text-decoration: none; } @media only screen and (min-width: 1024px) { .related-post .post-list .item { width: 30%; } } @media only screen and (min-width: 768px) and (max-width: 1023px) { .related-post .post-list .item { width: 90%; } } @media only screen and (min-width: 0px) and (max-width: 767px) { .related-post .post-list .item { width: 90%; } }
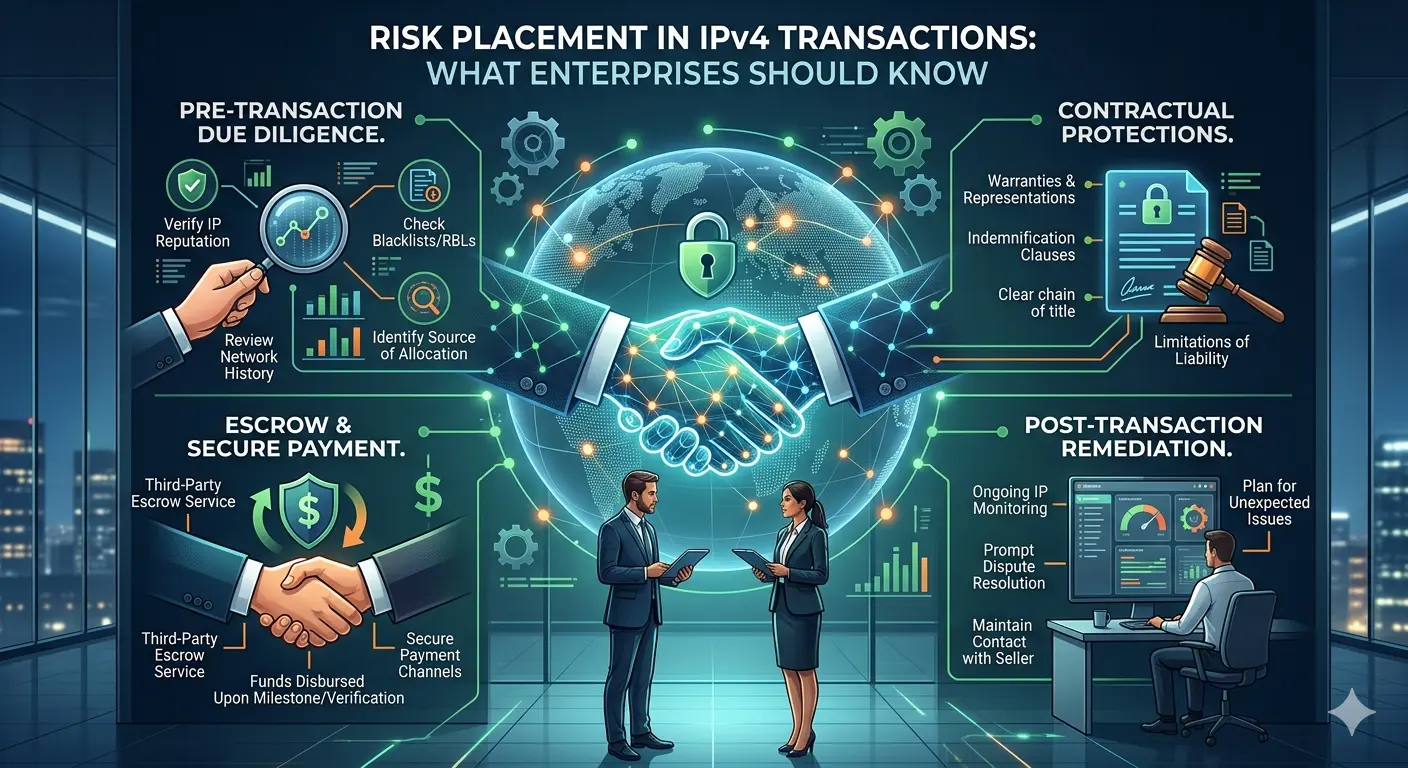
Risk Placement in IPv4 Transactions: What Enterprises Should Know
The IPv4 market has quietly evolved into a structured secondary asset class. As global IPv4 exhaustion continues, enterprises, ISPs, and brokers now routinely engage in buying, leasing, and transferring IPv4 address blocks. Alongside this growth, one topic has become increasingly important—but still under-discussed: risk placement in IPv4 transactions. For organizations participating in this market, especially through platforms such as i.lease, understanding how risk is identified, allocated, and mitigated isRead more Related Posts Risk Placement in IPv4 Transactions: What Enterprises Should Know The IPv4 market has quietly evolved into a structured secondary asset class. As global IPv4 exhaustion continues, enterprises, ISPs, and Understanding Operational Risk in IPv4 Address Markets IPv4 has long stopped being a simple technical identifier system. It has become a constrained, priced, and operationally embedded infrastructure Por qué la mayoría de las empresas están expuestas accidentalmente al riesgo de fallo en la asignación de IPv4 La escasez de IPv4 es ampliamente comprendida. Lo que muchas empresas aún subestiman es el riesgo de continuidad relacionado con .related-post {} .related-post .post-list { text-align: left; } .related-post .post-list .item { margin: 5px; padding: 10px; } .related-post .headline { font-size: 18px !important; color: #999999 !important; } .related-post .post-list .item .post_thumb { max-height: 220px; margin: 10px 0px; padding: 0px; display: block; } .related-post .post-list .item .post_title { font-size: 16px; color: #3f3f3f; margin: 10px 0px; padding: 0px; display: block; text-decoration: none; } .related-post .post-list .item .post_excerpt { font-size: 13px; color: #3f3f3f; margin: 10px 0px; padding: 0px; display: block; text-decoration: none; } @media only screen and (min-width: 1024px) { .related-post .post-list .item { width: 30%; } } @media only screen and (min-width: 768px) and (max-width: 1023px) { .related-post .post-list .item { width: 90%; } } @media only screen and (min-width: 0px) and (max-width: 767px) { .related-post .post-list .item { width: 90%; } }
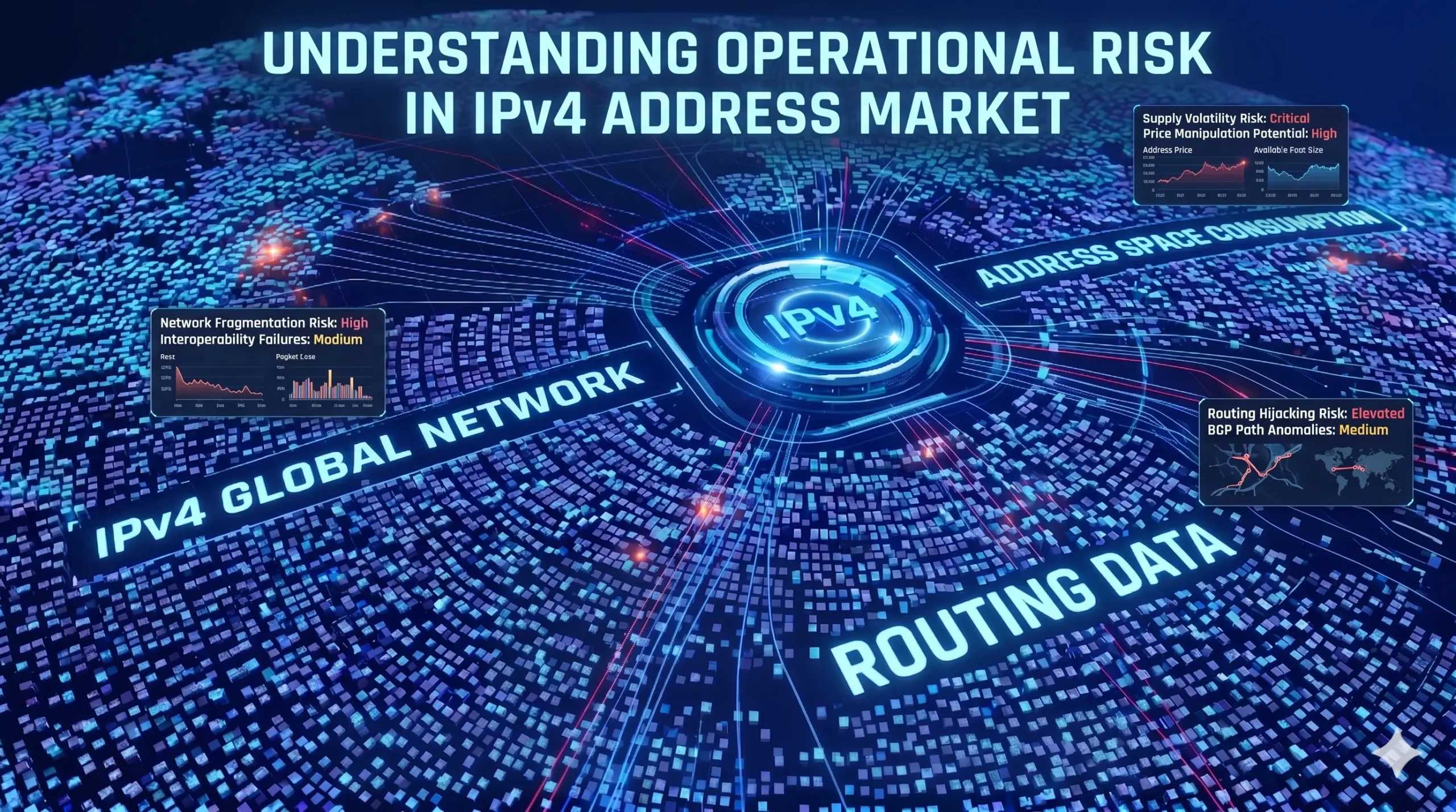
Understanding Operational Risk in IPv4 Address Markets
IPv4 has long stopped being a simple technical identifier system. It has become a constrained, priced, and operationally embedded infrastructure asset class. “In the IPv4 market, execution is not paperwork. Execution is continuity under registry-layer uncertainty.”https://heng.lu/on-why-i-lease-exists-and-why-the-broker-question-is-really-a-registry-risk-question/ Yet most of the industry still speaks about it as if it were a straightforward marketplace problem: buyers, sellers, brokers, escrow, transfer, done. That framing is increasingly outdated. The real structure of riskRead more Related Posts Risk Placement in IPv4 Transactions: What Enterprises Should Know The IPv4 market has quietly evolved into a structured secondary asset class. As global IPv4 exhaustion continues, enterprises, ISPs, and Understanding Operational Risk in IPv4 Address Markets IPv4 has long stopped being a simple technical identifier system. It has become a constrained, priced, and operationally embedded infrastructure Por qué la mayoría de las empresas están expuestas accidentalmente al riesgo de fallo en la asignación de IPv4 La escasez de IPv4 es ampliamente comprendida. Lo que muchas empresas aún subestiman es el riesgo de continuidad relacionado con .related-post {} .related-post .post-list { text-align: left; } .related-post .post-list .item { margin: 5px; padding: 10px; } .related-post .headline { font-size: 18px !important; color: #999999 !important; } .related-post .post-list .item .post_thumb { max-height: 220px; margin: 10px 0px; padding: 0px; display: block; } .related-post .post-list .item .post_title { font-size: 16px; color: #3f3f3f; margin: 10px 0px; padding: 0px; display: block; text-decoration: none; } .related-post .post-list .item .post_excerpt { font-size: 13px; color: #3f3f3f; margin: 10px 0px; padding: 0px; display: block; text-decoration: none; } @media only screen and (min-width: 1024px) { .related-post .post-list .item { width: 30%; } } @media only screen and (min-width: 768px) and (max-width: 1023px) { .related-post .post-list .item { width: 90%; } } @media only screen and (min-width: 0px) and (max-width: 767px) { .related-post .post-list .item { width: 90%; } }
