How Law Enforcement Tracks Hackers and Telco Scammers: Tools & Techniques
Cybercrime is on the rise, with hackers and telco scammers using sophisticated methods to hide their identities. Law enforcement agencies rely on advanced IP tracking tools, forensic analysis, and cyber intelligence to trace and catch these criminals. In this article, we’ll explore the top tools and techniques used by authorities worldwide to track down cybercriminals.
Table of Contents
IP Tracking & Geolocation Tools
To pinpoint the location of a hacker, authorities use IP tracking and geolocation tools such as MaxMind GeoIP, IPinfo.io, and Whois Lookup. These tools provide insights into an IP address’s physical location, associated ISP, and network details. Shodan and Censys further help by scanning connected devices to reveal potential vulnerabilities that hackers might exploit.
Network Traffic Analysis & Packet Capture
Monitoring real-time network traffic is essential in cybercrime investigations. Tools like Wireshark, Tcpdump, and Zeek (Bro IDS) allow law enforcement to capture and analyze network packets, helping to identify malicious activity. These tools can detect unauthorized connections, suspicious data transfers, and unusual traffic spikes that may indicate cybercrime activities.
Digital Forensics & Log Analysis
Cybercriminals often leave digital footprints that can be uncovered through forensic analysis. Tools like Autopsy, X-Ways Forensics, and Splunk help authorities analyze logs, recover deleted files, and trace an attacker’s movements. ELK Stack (Elasticsearch, Logstash, Kibana) and Graylog provide powerful log monitoring capabilities, assisting in tracking hacker activities over time.
OSINT (Open-Source Intelligence) Tools
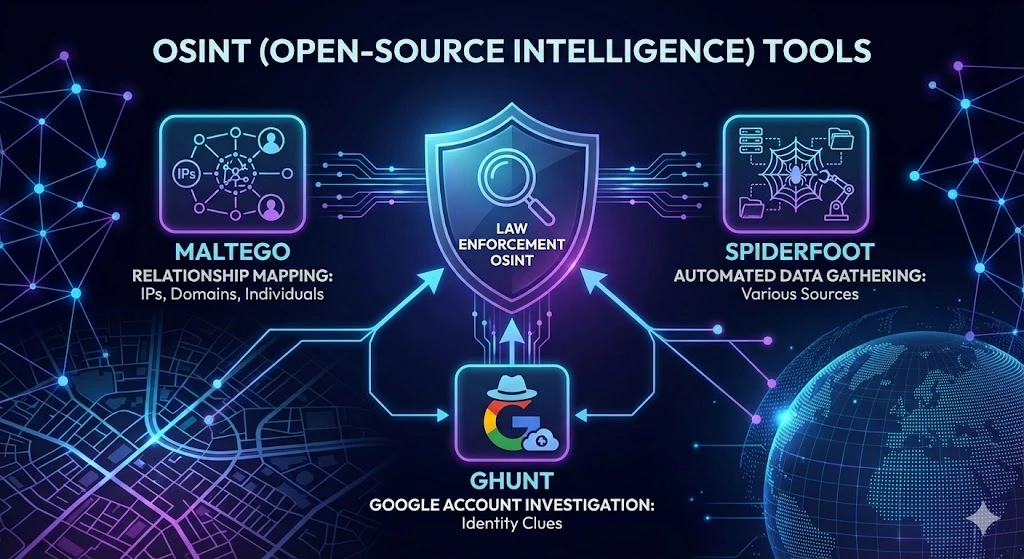
Law enforcement leverages OSINT tools to collect intelligence from publicly available sources. Maltego helps map relationships between IPs, domains, and individuals, while SpiderFoot automates data gathering from various sources. Additionally, GHunt can investigate Google account activity, providing valuable clues about a suspect’s identity.
Tor & Dark Web Monitoring
Hackers and scammers frequently use Tor and dark web platforms to operate anonymously. Tools like Ahmia and OnionScan assist in uncovering hidden services, while CipherTrace and Chainalysis track cryptocurrency transactions linked to cybercrime. Law enforcement also employs ShadowDragon to monitor darknet activities and uncover criminal networks.
ISP Collaboration & Legal Requests
One of the most effective ways to trace hackers is through ISP collaboration. Law enforcement agencies issue subpoenas and MLAT (Mutual Legal Assistance Treaty) requests to obtain user logs from ISPs. Programs like LEAP (Law Enforcement Access Program) and organizations such as Interpol, FBI, and Europol work together to track cybercriminals across borders.
Anti-VPN & Proxy Detection
Many hackers use VPNs, proxies, or the Tor network to mask their real IP addresses. Tools like IPQualityScore, FraudLabs Pro, and Scamalytics help detect these disguises by identifying suspicious IP patterns, VPN usage, and proxy servers. These solutions help law enforcement unmask hidden attackers.
Honeypots & Cyber Threat Intelligence
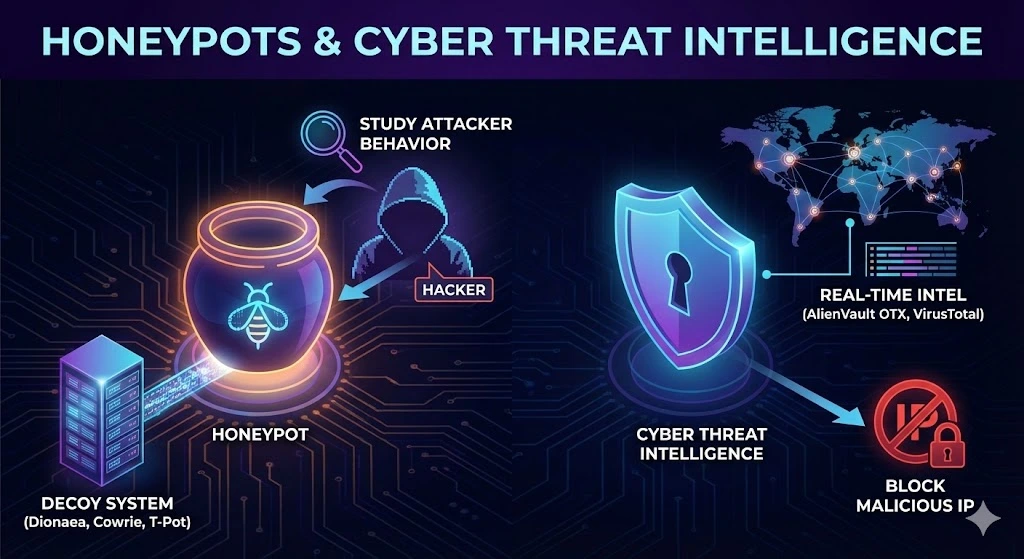
To catch cybercriminals, law enforcement deploys honeypots—decoy systems designed to lure hackers. Tools like Dionaea, Cowrie, and T-Pot simulate vulnerable systems, allowing authorities to study attacker behavior. Additionally, AlienVault OTX and VirusTotal provide real-time threat intelligence, helping to identify and block malicious IP addresses.
Advanced & Government-Level Tracking
Top intelligence agencies employ advanced surveillance programs to track cybercriminals worldwide. XKeyscore (NSA tool) and PRISM (U.S. surveillance program) collect vast amounts of internet data. Echelon, a global surveillance system, monitors communications for national security threats. Meanwhile, Palantir Gotham integrates AI-powered analytics for large-scale investigations.
How Law Enforcement Tracks Hackers & Scammers
To successfully track and apprehend cybercriminals, law enforcement follows a multi-layered approach. This includes IP geolocation tracking, ISP subpoenas, network traffic analysis, OSINT research, and social engineering tactics. Some agencies conduct undercover dark web operations to infiltrate hacking forums and identify criminal masterminds. By combining cutting-edge technology with intelligence collaboration, authorities can track and prosecute hackers effectively.
Final Thoughts
As cyber threats continue to evolve, so do the tools and techniques used by law enforcement to track and locate hackers and scammers. By leveraging IP tracking, digital forensics, OSINT, honeypots, and dark web monitoring, authorities can uncover cybercriminal networks and bring them to justice. If you’re in cybersecurity, law enforcement, or digital forensics, staying ahead of these trends is critical to combating online threats.
Trusted IPv4 Leasing for Business Growth
Get enterprise-grade IPv4 space quickly, with seamless deployment and end-to-end management.
Get Started with i.leaseRelated Posts
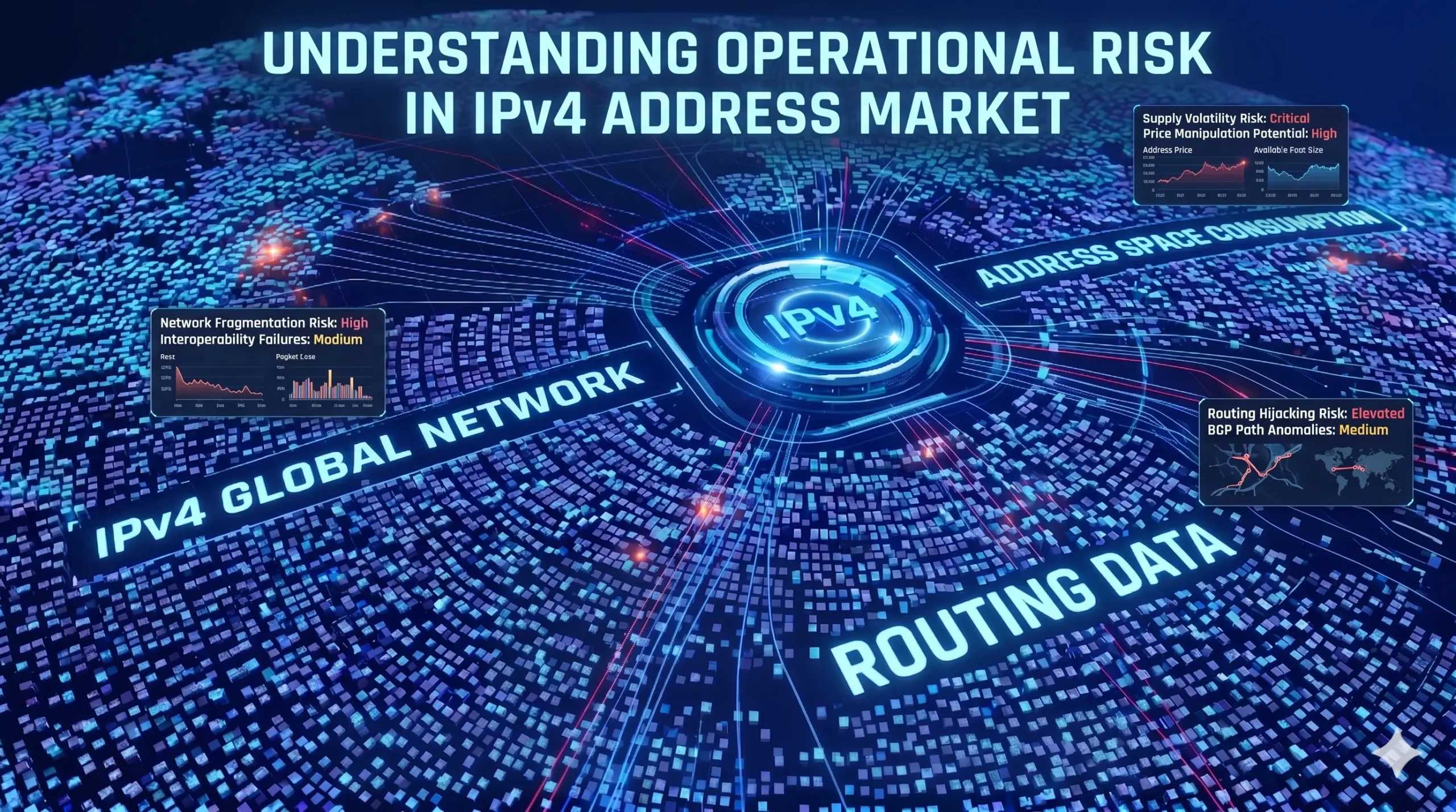
Understanding Operational Risk in IPv4 Address Markets
IPv4 has long stopped being a simple technical identifier system. It has become a constrained, priced, and operationally embedded infrastructure asset class. “In the IPv4 market, execution is not paperwork. Execution is continuity under registry-layer uncertainty.”https://heng.lu/on-why-i-lease-exists-and-why-the-broker-question-is-really-a-registry-risk-question/ Yet most of the industry still speaks about it as if it were a straightforward marketplace problem: buyers, sellers, brokers, escrow, transfer, done. That framing is increasingly outdated. The real structure of riskRead more Related Posts 企业入站与出站 IPv4 租赁完整指南 租赁 IPv4 地址可以转移部分伴随完全所有权而来的风险。例如,购买地址可能会让组织暴露于价格波动、长期贬值风险以及信誉管理责任之中。通过 i.Lease 进行租赁,企业可以降低这些风险暴露,并在明确期限内维持可预测的成本,从而支持更可靠的预算规划和风险管理实践。这种方式也简化了基础设施管理,因为租赁供应商通常会负责滥用监控、信誉检查和注册机构协调,使承租方能够专注于核心业务功能,而不是 IP 资产管理。IPv4 租赁并不限于单一行业。托管服务商、云平台、电信公司、SaaS 公司和网络安全企业都可以从租赁中受益。例如,托管服务商可以在无需大量前期投资的情况下扩展服务器部署,而网络安全公司则可以根据客户需求灵活增加地址空间,而无需承诺完全购买。在销售、营销和监管测试中,租赁允许组织在特定地区试运行部署,而无需投入大量资本。这种战略灵活性支持创新,同时帮助企业在 IPv4 稀缺持续存在的市场中保持韧性。利用 i.Lease 进行 IPv4 租赁管理的好处非常清楚:具成本效益的访问、快速部署、信誉安全、可扩展性、地理多样性和持续支持。在 IPv4 地址稀缺且直接购买成本高昂的环境中,通过值得信赖的平台进行租赁,使组织能够维持连接、按需扩展基础设施,并高效管理资源。通过将 IPv4 租赁视为基础设施规划的重要组成部分,而不是临时替代方案,企业可以在应对 IPv4 Understanding Operational Risk in IPv4 Address Markets IPv4 has long stopped being a simple technical identifier system. It has become a constrained, priced, and operationally embedded infrastructure Por qué la mayoría de las empresas están expuestas accidentalmente al riesgo de fallo en la asignación de IPv4 La escasez de IPv4 es ampliamente comprendida. Lo que muchas empresas aún subestiman es el riesgo de continuidad relacionado con .related-post {} .related-post .post-list { text-align: left; } .related-post .post-list .item { margin: 5px; padding: 10px; } .related-post .headline { font-size: 18px !important; color: #999999 !important; } .related-post .post-list .item .post_thumb { max-height: 220px; margin: 10px 0px; padding: 0px; display: block; } .related-post .post-list .item .post_title { font-size: 16px; color: #3f3f3f; margin: 10px 0px; padding: 0px; display: block; text-decoration: none; } .related-post .post-list .item .post_excerpt { font-size: 13px; color: #3f3f3f; margin: 10px 0px; padding: 0px; display: block; text-decoration: none; } @media only screen and (min-width: 1024px) { .related-post .post-list .item { width: 30%; } } @media only screen and (min-width: 768px) and (max-width: 1023px) { .related-post .post-list .item { width: 90%; } } @media only screen and (min-width: 0px) and (max-width: 767px) { .related-post .post-list .item { width: 90%; } }
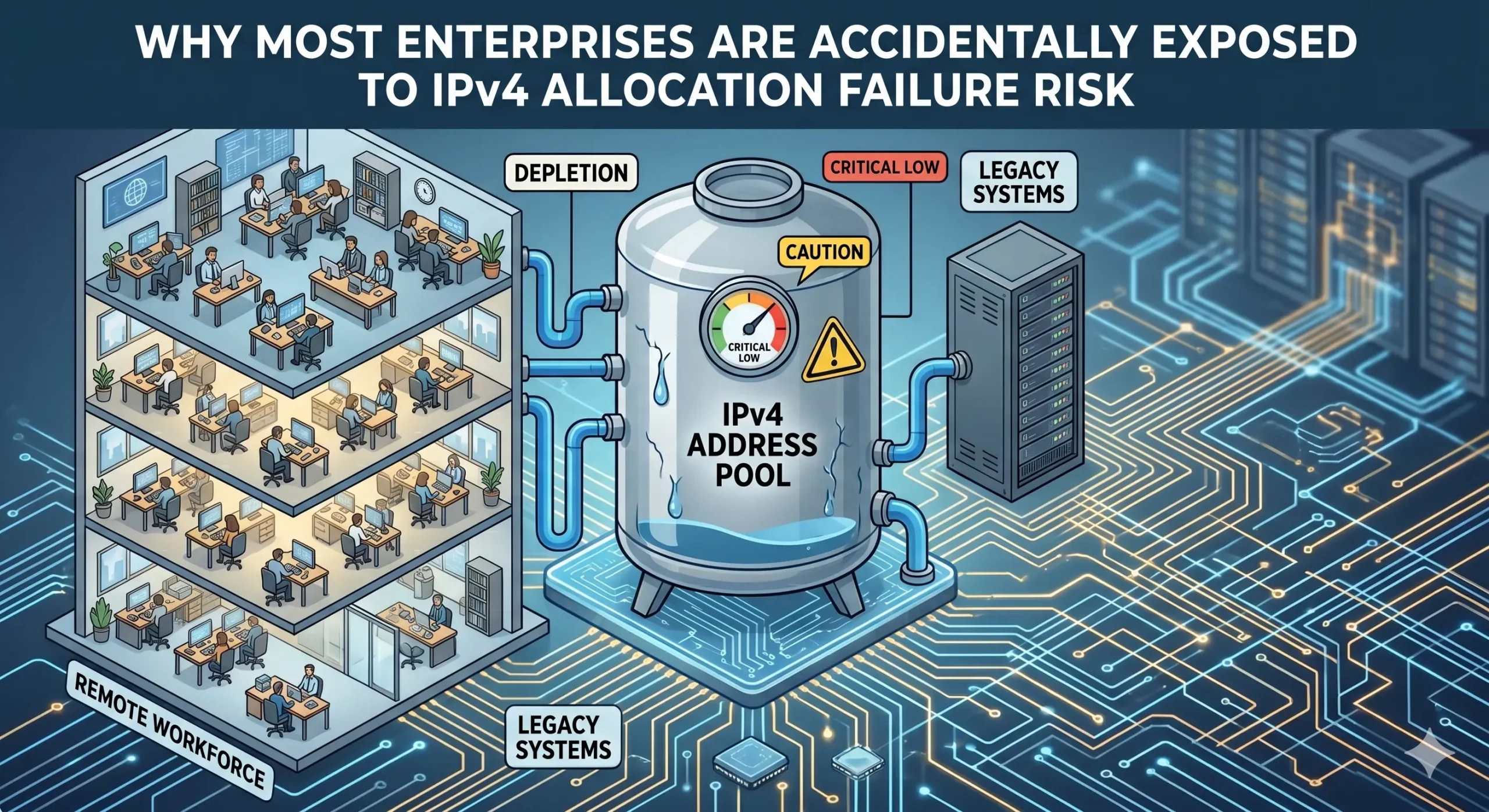
Why most enterprises are accidentally exposed to IPv4 allocation failure risk
IPv4 scarcity is widely understood. What many enterprises still underestimate is the continuity risk surrounding how address resources are governed and maintained. Enterprises often maintain operational use of IPv4 resources without full visibility into the continuity conditions supporting those allocations. The growing reliance on leasing, transfers, and provider-managed infrastructure is reshaping IPv4 Allocation into a long-term governance issue. IPv4 Allocation has quietly become a continuity issue For many enterpriseRead more Related Posts Understanding Operational Risk in IPv4 Address Markets IPv4 has long stopped being a simple technical identifier system. It has become a constrained, priced, and operationally embedded infrastructure Primauté du code en cours d’exécution : pourquoi la location d’adresses IPv4 doit être jugée sur la base de preuves opérationnelles La location IPv4 commence souvent par une question simple :Ce fournisseur peut-il nous fournir les adresses ?Mais pour les entreprises Risques liés au renouvellement d’IPv4 : quand le manque de responsabilisation se transforme en trahison du code en cours d’exécution La plupart des entreprises entrent sur le marché IPv4 avec un objectif simple. Elles ont besoin d’adresses. Peut-être en ont-elles .related-post {} .related-post .post-list { text-align: left; } .related-post .post-list .item { margin: 5px; padding: 10px; } .related-post .headline { font-size: 18px !important; color: #999999 !important; } .related-post .post-list .item .post_thumb { max-height: 220px; margin: 10px 0px; padding: 0px; display: block; } .related-post .post-list .item .post_title { font-size: 16px; color: #3f3f3f; margin: 10px 0px; padding: 0px; display: block; text-decoration: none; } .related-post .post-list .item .post_excerpt { font-size: 13px; color: #3f3f3f; margin: 10px 0px; padding: 0px; display: block; text-decoration: none; } @media only screen and (min-width: 1024px) { .related-post .post-list .item { width: 30%; } } @media only screen and (min-width: 768px) and (max-width: 1023px) { .related-post .post-list .item { width: 90%; } } @media only screen and (min-width: 0px) and (max-width: 767px) { .related-post .post-list .item { width: 90%; } }
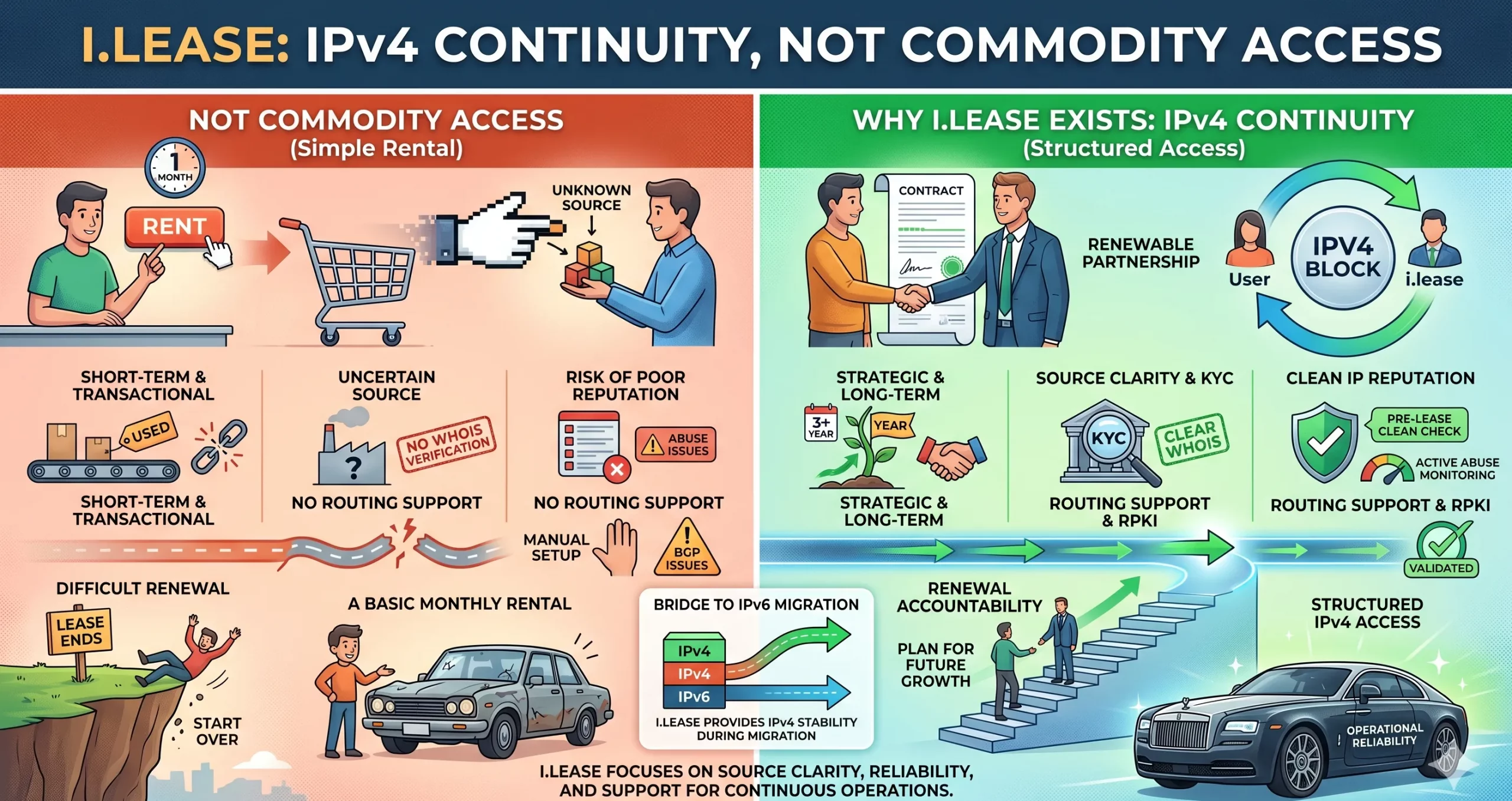
Why i.lease Exists: IPv4 Continuity Is Not Commodity Access
Most businesses enter the IPv4 market with a simple goal. They need addresses. Maybe they need them for hosting.Maybe they need them for VPN infrastructure.Maybe they need them for cloud services, SaaS platforms, telecom expansion, email systems, cybersecurity tools, or customer-facing applications. So they search for an IPv4 provider. They compare prices. They check block sizes. They ask how fast delivery can happen. They look for a seller, broker, Related Posts 企业入站与出站 IPv4 租赁完整指南 租赁 IPv4 地址可以转移部分伴随完全所有权而来的风险。例如,购买地址可能会让组织暴露于价格波动、长期贬值风险以及信誉管理责任之中。通过 i.Lease 进行租赁,企业可以降低这些风险暴露,并在明确期限内维持可预测的成本,从而支持更可靠的预算规划和风险管理实践。这种方式也简化了基础设施管理,因为租赁供应商通常会负责滥用监控、信誉检查和注册机构协调,使承租方能够专注于核心业务功能,而不是 IP 资产管理。IPv4 租赁并不限于单一行业。托管服务商、云平台、电信公司、SaaS 公司和网络安全企业都可以从租赁中受益。例如,托管服务商可以在无需大量前期投资的情况下扩展服务器部署,而网络安全公司则可以根据客户需求灵活增加地址空间,而无需承诺完全购买。在销售、营销和监管测试中,租赁允许组织在特定地区试运行部署,而无需投入大量资本。这种战略灵活性支持创新,同时帮助企业在 IPv4 稀缺持续存在的市场中保持韧性。利用 i.Lease 进行 IPv4 租赁管理的好处非常清楚:具成本效益的访问、快速部署、信誉安全、可扩展性、地理多样性和持续支持。在 IPv4 地址稀缺且直接购买成本高昂的环境中,通过值得信赖的平台进行租赁,使组织能够维持连接、按需扩展基础设施,并高效管理资源。通过将 IPv4 租赁视为基础设施规划的重要组成部分,而不是临时替代方案,企业可以在应对 IPv4 Risques liés au renouvellement d’IPv4 : quand le manque de responsabilisation se transforme en trahison du code en cours d’exécution La plupart des entreprises entrent sur le marché IPv4 avec un objectif simple. Elles ont besoin d’adresses. Peut-être en ont-elles 大多数企业为何会意外面临 IPv4 地址分配失败的风险 IPv4 稀缺性已被广泛理解。许多企业仍然低估的是:地址资源如何被治理和维护所带来的连续性风险。 企业往往在持续使用 IPv4 资源的同时,并没有完全看清支撑这些分配的连续性条件。 对租赁、转让和供应商管理型基础设施的依赖不断增加,正在将 IPv4地址分配 重塑为一个长期治理问题。 IPv4地址分配已悄然成为连续性问题 对许多企业 IT 团队来说,IPv4 地址看起来仍然在运营上保持稳定。 应用程序仍然可以访问。云平台继续扩展。连接服务供应商在没有明显中断的情况下提供服务。从外部看,互联网似乎仍像过去一样运行。 然而,在这种运营稳定性之下,IPv4地址分配的结构已经发生了根本变化。 可自由分配的 IPv4 空间耗尽早已不是新闻。American Registry for .related-post {} .related-post .post-list { text-align: left; } .related-post .post-list .item { margin: 5px; padding: 10px; } .related-post .headline { font-size: 18px !important; color: #999999 !important; } .related-post .post-list .item .post_thumb { max-height: 220px; margin: 10px 0px; padding: 0px; display: block; } .related-post .post-list .item .post_title { font-size: 16px; color: #3f3f3f; margin: 10px 0px; padding: 0px; display: block; text-decoration: none; } .related-post .post-list .item .post_excerpt { font-size: 13px; color: #3f3f3f; margin: 10px 0px; padding: 0px; display: block; text-decoration: none; } @media only screen and (min-width: 1024px) { .related-post .post-list .item { width: 30%; } } @media only screen and (min-width: 768px) and (max-width: 1023px) { .related-post .post-list .item { width: 90%; } } @media only screen and (min-width: 0px) and (max-width: 767px) { .related-post .post-list .item { width: 90%; } }
