Internet Censorship and the Great Firewall
Internet Censorship and the Great Firewall: Understanding the Boundaries of the Digital World
The Internet has revolutionized the way we connect, learn, and share information, but its open nature has also led to significant debates about control, privacy, and freedom.
Table of Contents
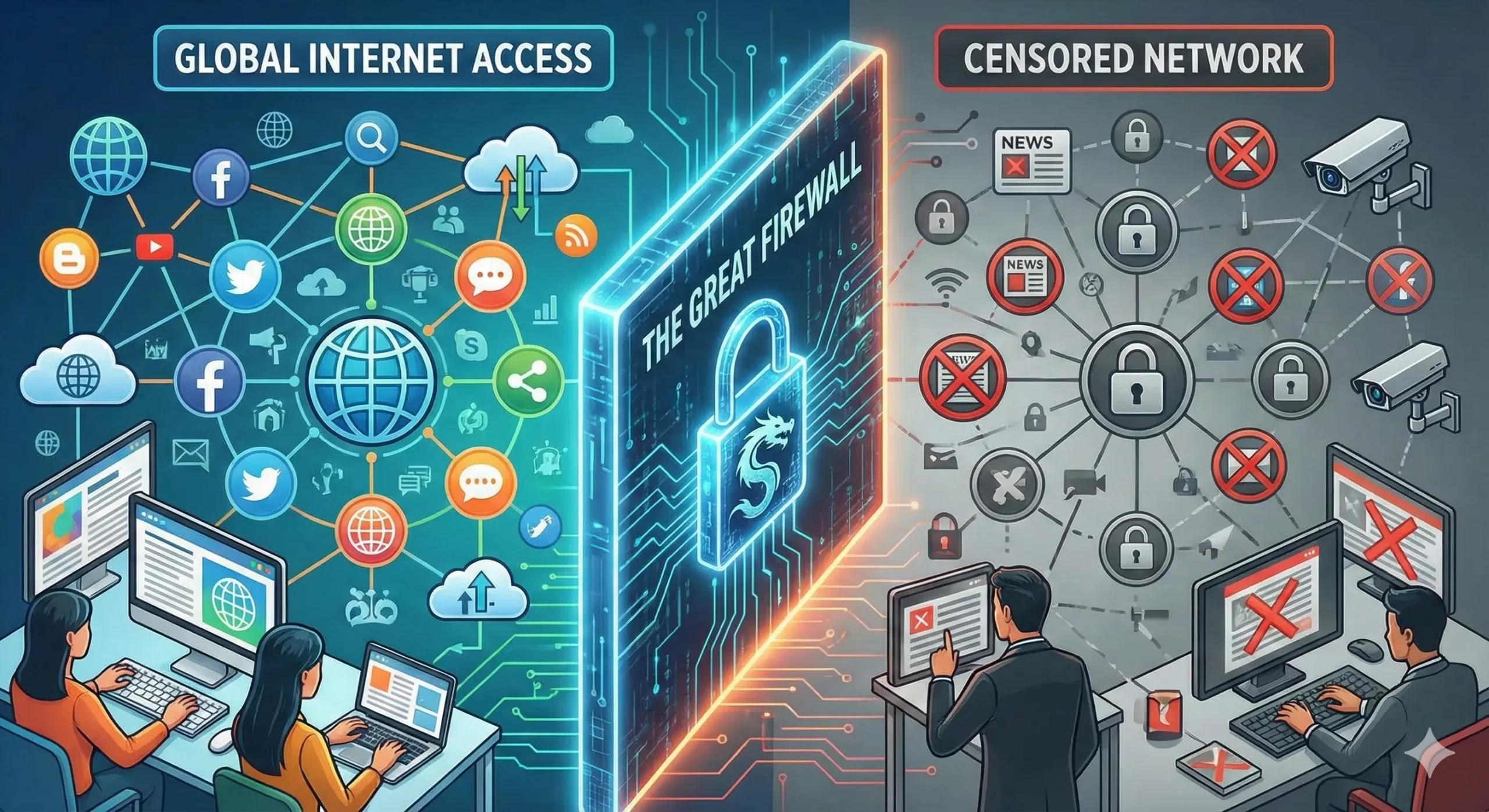
At the center of these discussions lies the concept of Internet censorship and, most notably, China’s Great Firewall (GFW). This article explores the intricacies of Internet censorship, its implementation, and the technology behind the Great Firewall.
What Is Internet Censorship?
Internet censorship refers to the control or suppression of access to information on the Internet. Governments, private organizations, or other regulatory bodies may enforce censorship to restrict the content available to users. This can range from blocking specific websites to filtering search results or monitoring online activities.
Why Is Internet Censorship Implemented?
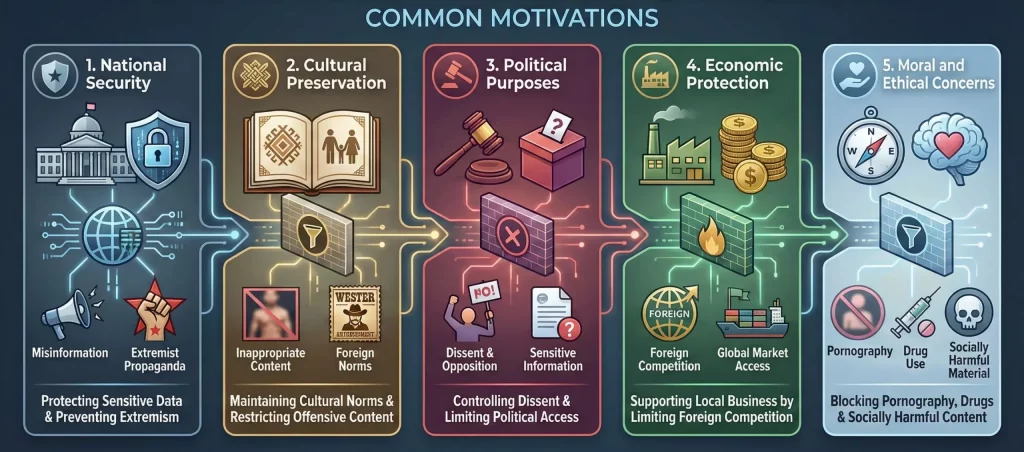
The reasons for implementing Internet censorship vary by country, ideology, and circumstance. Common motivations include:
1) National Security: Protecting sensitive government data and preventing the spread of misinformation or extremist propaganda.
2) Cultural Preservation: Maintaining cultural norms by restricting access to inappropriate or offensive content.
3) Political Purposes: Controlling dissent and opposition by limiting access to politically sensitive information.
4) Economic Protection: Supporting local businesses by limiting competition from foreign companies.
5) Moral and Ethical Concerns: Blocking content related to pornography, drug use, or other socially harmful material.
While proponents argue that censorship is essential for maintaining societal order, critics view it as a violation of free speech and access to information.
What Is the Great Firewall?
The Great Firewall, officially known as the “Golden Shield Project,” is China’s sophisticated Internet censorship system. Implemented in the early 2000s, the Great Firewall is designed to regulate the flow of information and control access to international websites and services that conflict with the government’s policies and ideologies.
Key features of the Great Firewall include:
- Blocking access to popular websites like Google, Facebook, and Twitter.
- Restricting foreign news outlets and platforms critical of the Chinese government.
- Monitoring and filtering user activities to ensure compliance with local laws.
How Is Internet Censorship Implemented?
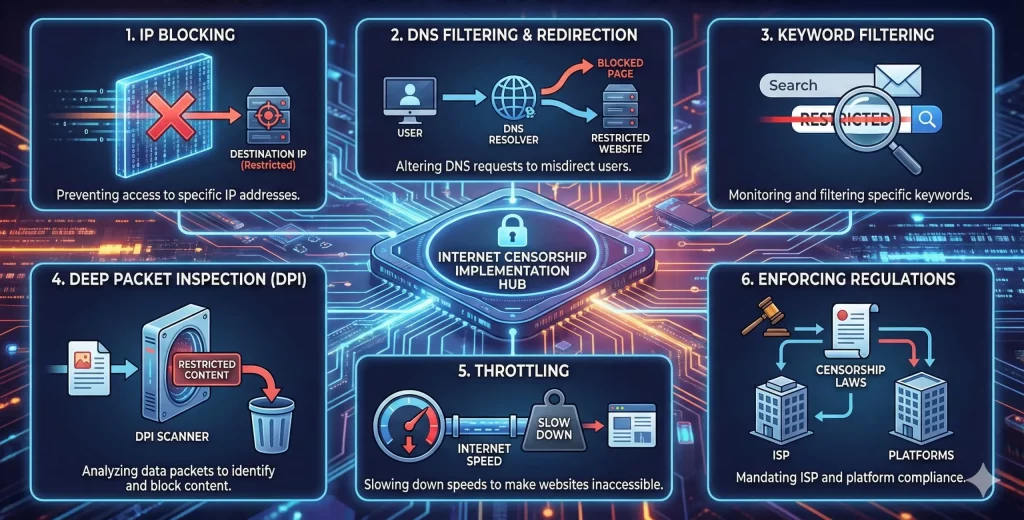
Internet censorship involves a combination of technical measures and regulatory policies. Here are the primary methods:
- IP Blocking: Preventing access to specific IP addresses linked to restricted websites.
- DNS Filtering and Redirection: Altering Domain Name System (DNS) requests to misdirect users trying to reach restricted websites.
- Keyword Filtering: Monitoring and filtering specific keywords in search queries, emails, or social media posts.
- Deep Packet Inspection (DPI): Analyzing data packets to identify and block restricted content.
- Throttling: Slowing down Internet speeds for certain websites or services to make them virtually inaccessible.
- Enforcing Regulations: Mandating that Internet service providers (ISPs) and platforms comply with censorship laws.
How Does the Great Firewall Work?
The Great Firewall employs an advanced blend of the above techniques, enhanced by artificial intelligence (AI) and machine learning technologies. Here’s how it functions:
- Network Surveillance: The Chinese government monitors traffic through DPI, allowing authorities to block or throttle connections to restricted websites.
- URL Filtering: Specific URLs or domains are blacklisted to prevent users from accessing them.
- Keyword Monitoring: Content with sensitive keywords is flagged and blocked, affecting search engines and social media platforms.
- VPN Detection and Blocking: Virtual Private Networks (VPNs), often used to bypass censorship, are detected and disabled through advanced algorithms.
- Collaboration with Local Companies: Domestic platforms like WeChat and Baidu operate under strict regulatory guidelines to enforce censorship internally.
Conclusion
Internet censorship and the Great Firewall exemplify the complexities of regulating the digital space. While censorship aims to achieve goals like national security and cultural preservation, it often raises ethical questions about freedom of expression and access to information.
The Great Firewall, in particular, showcases how technology can be leveraged to control online narratives, creating a heavily monitored and filtered Internet ecosystem.
Trusted IPv4 Leasing for Business Growth
Get enterprise-grade IPv4 space quickly, with seamless deployment and end-to-end management.
Get Started with i.leaseRelated Posts
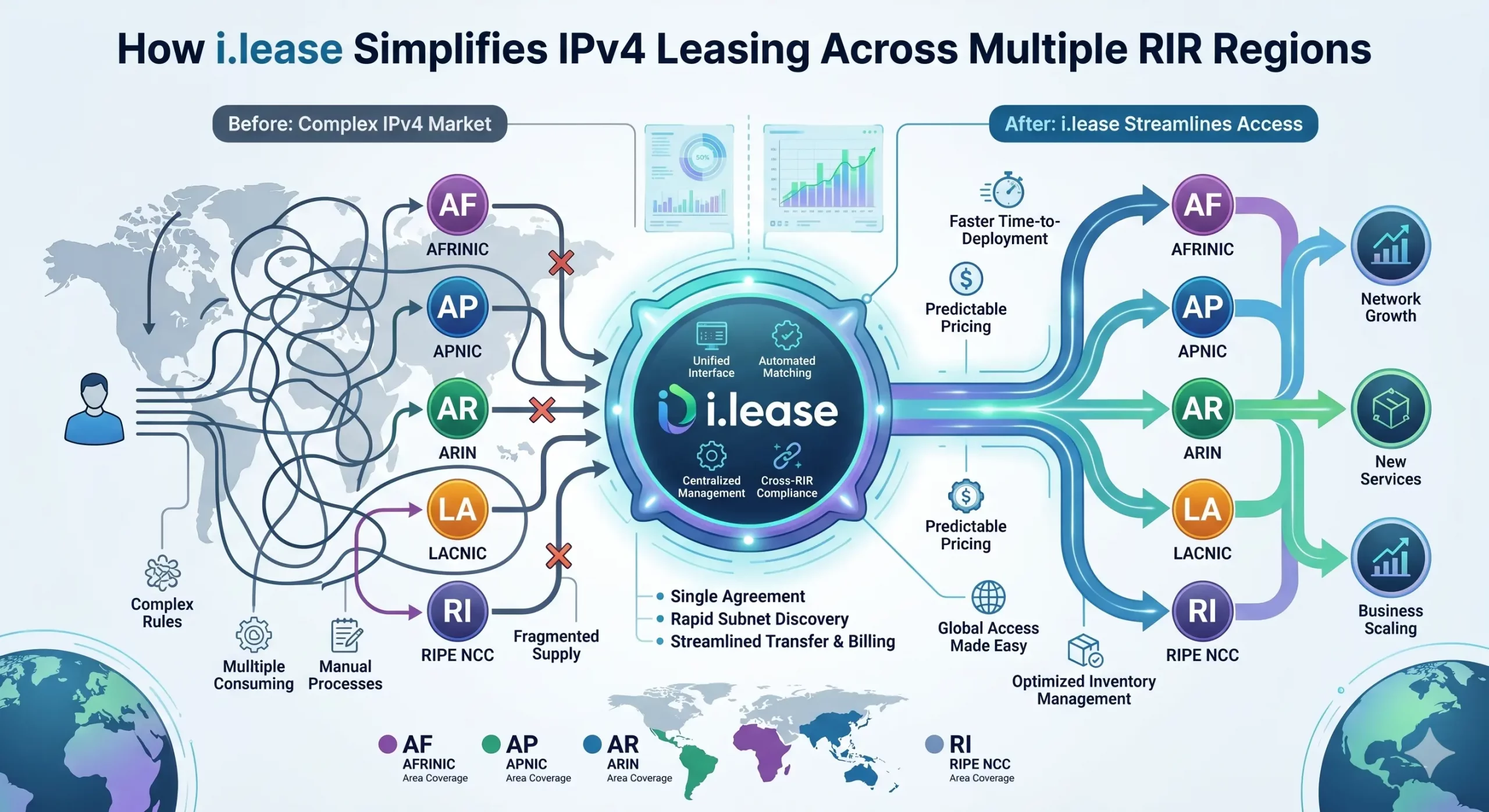
How i.lease Simplifies IPv4 Leasing Across Multiple RIR Regions
In today’s Internet infrastructure economy, IPv4 address leasing has become a critical operational strategy for enterprises, cloud providers, and network operators facing persistent address scarcity. As IPv4 exhaustion continues across all five Regional Internet Registries (RIRs)—ARIN, RIPE NCC, APNIC, LACNIC, and AFRINIC—the need for structured, compliant, and cross-regional leasing solutions has never been greater. However, beneath the surface of what appears to be a simple “supply-and-demand” market lies aRead more Related Posts Risk Placement in IPv4 Transactions: What Enterprises Should Know The IPv4 market has quietly evolved into a structured secondary asset class. As global IPv4 exhaustion continues, enterprises, ISPs, and Understanding Operational Risk in IPv4 Address Markets IPv4 has long stopped being a simple technical identifier system. It has become a constrained, priced, and operationally embedded infrastructure Por qué la mayoría de las empresas están expuestas accidentalmente al riesgo de fallo en la asignación de IPv4 La escasez de IPv4 es ampliamente comprendida. Lo que muchas empresas aún subestiman es el riesgo de continuidad relacionado con .related-post {} .related-post .post-list { text-align: left; } .related-post .post-list .item { margin: 5px; padding: 10px; } .related-post .headline { font-size: 18px !important; color: #999999 !important; } .related-post .post-list .item .post_thumb { max-height: 220px; margin: 10px 0px; padding: 0px; display: block; } .related-post .post-list .item .post_title { font-size: 16px; color: #3f3f3f; margin: 10px 0px; padding: 0px; display: block; text-decoration: none; } .related-post .post-list .item .post_excerpt { font-size: 13px; color: #3f3f3f; margin: 10px 0px; padding: 0px; display: block; text-decoration: none; } @media only screen and (min-width: 1024px) { .related-post .post-list .item { width: 30%; } } @media only screen and (min-width: 768px) and (max-width: 1023px) { .related-post .post-list .item { width: 90%; } } @media only screen and (min-width: 0px) and (max-width: 767px) { .related-post .post-list .item { width: 90%; } }
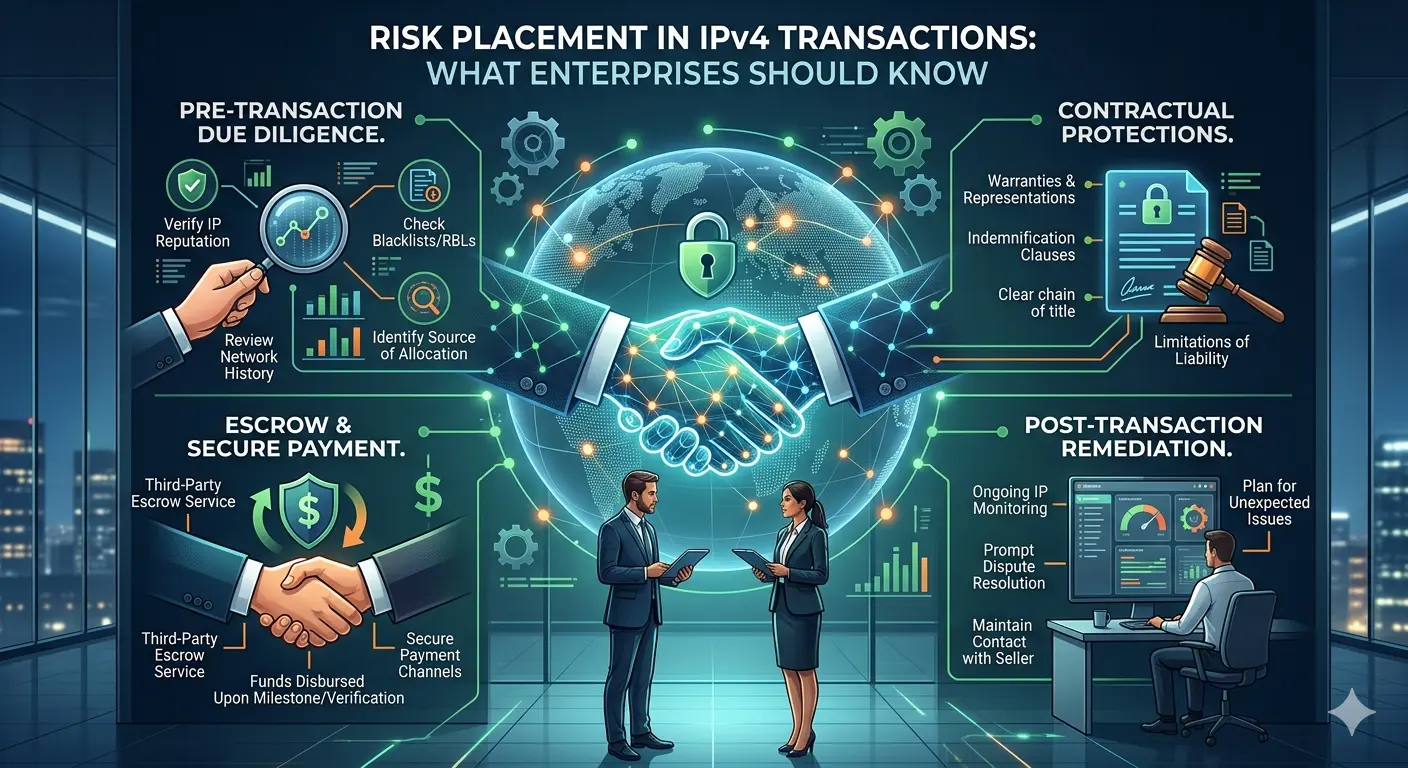
Risk Placement in IPv4 Transactions: What Enterprises Should Know
The IPv4 market has quietly evolved into a structured secondary asset class. As global IPv4 exhaustion continues, enterprises, ISPs, and brokers now routinely engage in buying, leasing, and transferring IPv4 address blocks. Alongside this growth, one topic has become increasingly important—but still under-discussed: risk placement in IPv4 transactions. For organizations participating in this market, especially through platforms such as i.lease, understanding how risk is identified, allocated, and mitigated isRead more Related Posts Risk Placement in IPv4 Transactions: What Enterprises Should Know The IPv4 market has quietly evolved into a structured secondary asset class. As global IPv4 exhaustion continues, enterprises, ISPs, and Understanding Operational Risk in IPv4 Address Markets IPv4 has long stopped being a simple technical identifier system. It has become a constrained, priced, and operationally embedded infrastructure Por qué la mayoría de las empresas están expuestas accidentalmente al riesgo de fallo en la asignación de IPv4 La escasez de IPv4 es ampliamente comprendida. Lo que muchas empresas aún subestiman es el riesgo de continuidad relacionado con .related-post {} .related-post .post-list { text-align: left; } .related-post .post-list .item { margin: 5px; padding: 10px; } .related-post .headline { font-size: 18px !important; color: #999999 !important; } .related-post .post-list .item .post_thumb { max-height: 220px; margin: 10px 0px; padding: 0px; display: block; } .related-post .post-list .item .post_title { font-size: 16px; color: #3f3f3f; margin: 10px 0px; padding: 0px; display: block; text-decoration: none; } .related-post .post-list .item .post_excerpt { font-size: 13px; color: #3f3f3f; margin: 10px 0px; padding: 0px; display: block; text-decoration: none; } @media only screen and (min-width: 1024px) { .related-post .post-list .item { width: 30%; } } @media only screen and (min-width: 768px) and (max-width: 1023px) { .related-post .post-list .item { width: 90%; } } @media only screen and (min-width: 0px) and (max-width: 767px) { .related-post .post-list .item { width: 90%; } }
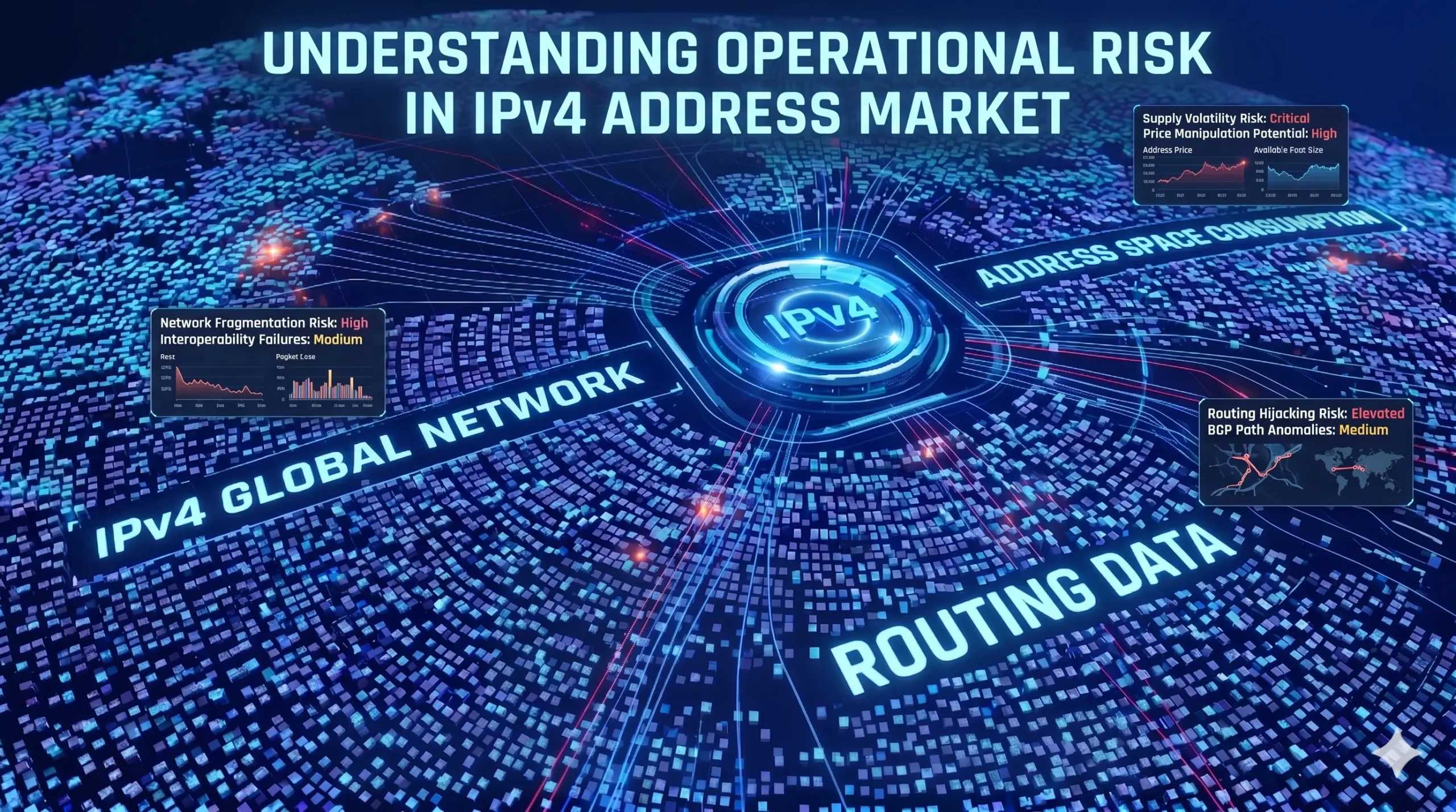
Understanding Operational Risk in IPv4 Address Markets
IPv4 has long stopped being a simple technical identifier system. It has become a constrained, priced, and operationally embedded infrastructure asset class. “In the IPv4 market, execution is not paperwork. Execution is continuity under registry-layer uncertainty.”https://heng.lu/on-why-i-lease-exists-and-why-the-broker-question-is-really-a-registry-risk-question/ Yet most of the industry still speaks about it as if it were a straightforward marketplace problem: buyers, sellers, brokers, escrow, transfer, done. That framing is increasingly outdated. The real structure of riskRead more Related Posts Risk Placement in IPv4 Transactions: What Enterprises Should Know The IPv4 market has quietly evolved into a structured secondary asset class. As global IPv4 exhaustion continues, enterprises, ISPs, and Understanding Operational Risk in IPv4 Address Markets IPv4 has long stopped being a simple technical identifier system. It has become a constrained, priced, and operationally embedded infrastructure Por qué la mayoría de las empresas están expuestas accidentalmente al riesgo de fallo en la asignación de IPv4 La escasez de IPv4 es ampliamente comprendida. Lo que muchas empresas aún subestiman es el riesgo de continuidad relacionado con .related-post {} .related-post .post-list { text-align: left; } .related-post .post-list .item { margin: 5px; padding: 10px; } .related-post .headline { font-size: 18px !important; color: #999999 !important; } .related-post .post-list .item .post_thumb { max-height: 220px; margin: 10px 0px; padding: 0px; display: block; } .related-post .post-list .item .post_title { font-size: 16px; color: #3f3f3f; margin: 10px 0px; padding: 0px; display: block; text-decoration: none; } .related-post .post-list .item .post_excerpt { font-size: 13px; color: #3f3f3f; margin: 10px 0px; padding: 0px; display: block; text-decoration: none; } @media only screen and (min-width: 1024px) { .related-post .post-list .item { width: 30%; } } @media only screen and (min-width: 768px) and (max-width: 1023px) { .related-post .post-list .item { width: 90%; } } @media only screen and (min-width: 0px) and (max-width: 767px) { .related-post .post-list .item { width: 90%; } }
