Meilleures pratiques pour la gestion des adresses IP élastiques
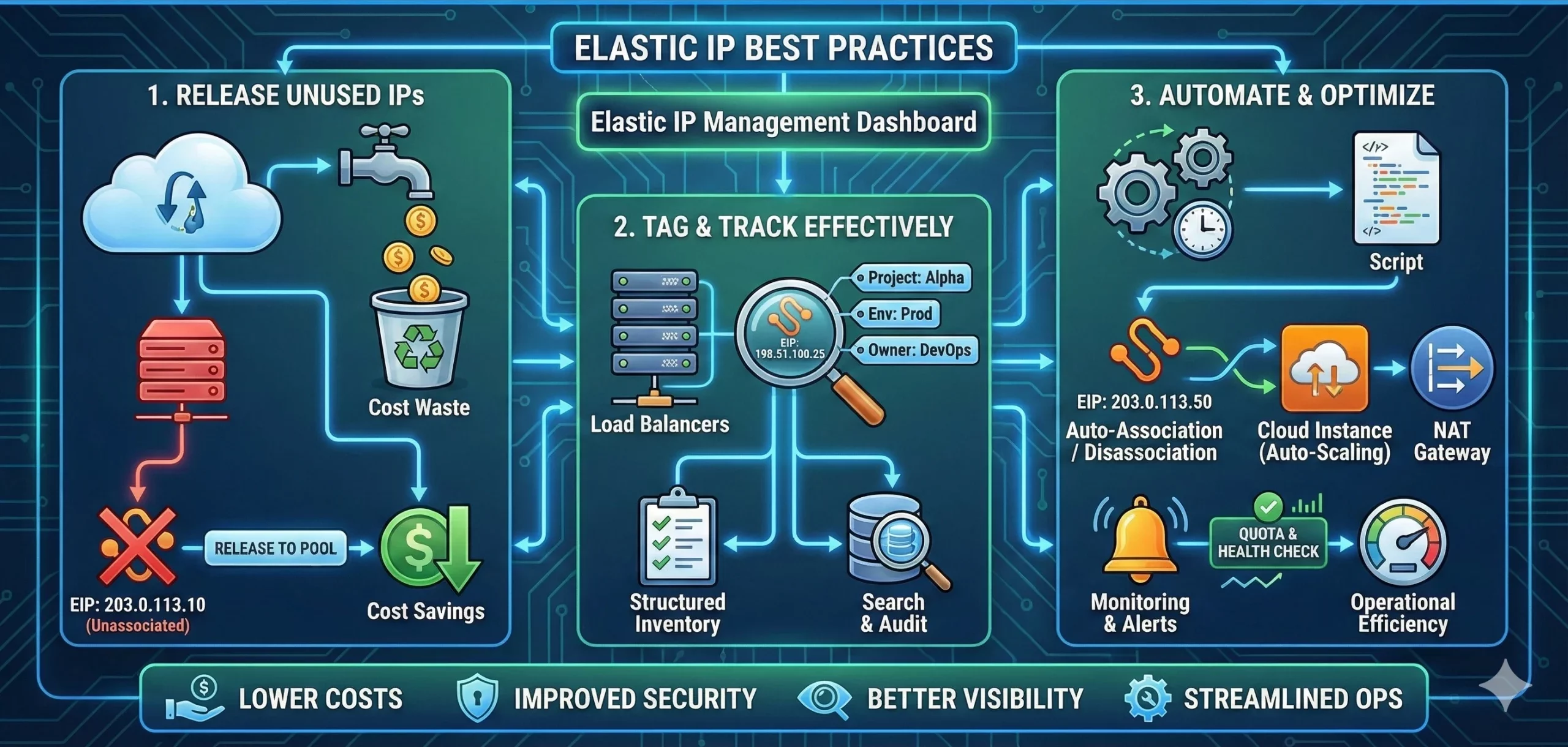
Les adresses IP élastiques (EIP) sont un élément essentiel des réseaux cloud, notamment sur Amazon Web Services (AWS). Elles fournissent une adresse IPv4 publique et statique associée à une instance, garantissant ainsi sa disponibilité même après son arrêt et son redémarrage. Cependant, une mauvaise gestion des adresses IP élastiques peut engendrer des risques de sécurité, des coûts inutiles et des pertes d’efficacité opérationnelle. Cet article présente les bonnes pratiques pour une gestion efficace des adresses IP élastiques, permettant d’optimiser les performances, de réduire les coûts et de renforcer la sécurité.
Table of Contents
1. N’attribuer et n’associer les EIP qu’en cas de nécessité.
AWS fournit un nombre limité d’adresses IP élastiques par compte, et toute adresse IP élastique inutilisée entraîne des frais supplémentaires. Pour optimiser l’utilisation des ressources :
- N’allouez une adresse IP élastique que lorsque vous avez besoin d’une adresse IP publique statique.
- Libérez les adresses IP élastiques inutilisées pour éviter des frais inutiles.
- Utilisez Elastic Load Balancer (ELB) ou AWS PrivateLink à la place des adresses IP élastiques lorsque cela est possible afin de réduire la dépendance aux adresses IP publiques.
2. Surveiller et auditer régulièrement l'utilisation de l'EIP
Un examen régulier des attributions d’EIP permet de prévenir les erreurs de gestion et les failles de sécurité.
- Utilisez AWS Cost Explorer et CloudWatch pour suivre l’utilisation des EIP et les coûts associés.
- Configurez des alertes pour informer les administrateurs des EIP non associées ou inactives.
- Vérifiez régulièrement votre compte afin de vous assurer que les EIP sont attribuées uniquement aux ressources nécessaires.
3. Sécuriser les adresses IP élastiques contre les accès non autorisés
Les adresses IP élastiques sont publiques et exposées à Internet, ce qui les rend vulnérables aux cybermenaces. Pour renforcer leur sécurité :
- Appliquez des règles de pare-feu strictes à l’aide des groupes de sécurité AWS et des listes de contrôle d’accès réseau (ACL).
- Mettez en œuvre des politiques de gestion des identités et des accès (IAM) afin de limiter les utilisateurs autorisés à allouer, associer et libérer des adresses IP élastiques.
- Utilisez AWS WAF (pare-feu d’applications web) pour protéger les applications utilisant des adresses IP élastiques contre les menaces web courantes.
4. Automatisez la gestion des EIP avec les outils AWS
L’automatisation permet de réduire les risques d’erreurs de configuration et de simplifier la gestion des EIP.
- Utilisez les fonctions AWS Lambda pour détecter et libérer automatiquement les EIP inutilisées.
- Mettez en œuvre l’infrastructure en tant que code (IaC) avec AWS CloudFormation ou Terraform pour gérer l’attribution et l’association des EIP par programmation.
- Tirez parti de l’interface de ligne de commande AWS (AWS CLI) et des kits de développement logiciel (SDK) pour automatiser les tâches de gestion des EIP et ainsi améliorer l’efficacité opérationnelle.
5. Optimiser l'utilisation de l'EIP pour une haute disponibilité
Les adresses IP élastiques permettent d’améliorer la disponibilité et les stratégies de basculement.
- Utilisez plusieurs adresses IP élastiques pour répartir le trafic entre des instances redondantes dans différentes zones de disponibilité.
- Automatisez le basculement en associant une adresse IP élastique à une instance de secours en cas de défaillance de l’instance principale.
- Utilisez Route 53 pour les solutions de basculement DNS compatibles avec les adresses IP élastiques.
6. Comprendre les limites du plan d'investissement énergétique (EIP) et demander des augmentations en cas de besoin.
AWS impose des limites au nombre d’adresses IP élastiques par région afin de prévenir les abus.
- Consultez votre quota d’adresses IP élastiques dans le tableau de bord des quotas de service AWS.
- Si votre architecture nécessite des adresses IP élastiques supplémentaires, demandez une augmentation en fournissant une justification au support AWS.
Conclusion
Une gestion efficace des adresses IP élastiques garantit la maîtrise des coûts, la sécurité et la haute disponibilité. En suivant ces bonnes pratiques, les entreprises peuvent optimiser leurs ressources cloud, éviter les dépenses inutiles et atténuer les risques de sécurité. La surveillance régulière, l’automatisation et les améliorations de sécurité sont essentielles à une gestion efficace des adresses IP élastiques sur AWS. Mettez en œuvre ces stratégies dès aujourd’hui pour rationaliser vos opérations réseau cloud.
Trusted IPv4 Leasing for Business Growth
Get enterprise-grade IPv4 space quickly, with seamless deployment and end-to-end management.
Get Started with i.leaseArticles connexes

Pourquoi utiliser IPv6? Avantages et cas d’utilisation en entreprise
Introduction L’IPv6 prend une importance croissante à mesure que les entreprises se préparent à la croissance à long terme d’Internet. Elle offre un espace d’adressage bien plus vaste que l’IPv4 et prend en charge l’expansion moderne des réseaux, notamment pour les services cloud, les réseaux mobiles, l’IoT, l’hébergement et l’infrastructure numérique mondiale. Cependant, l’adoption de l’IPv6 n’est pas encore achevée. De nombreuses entreprises dépendent encore de l’IPv4 pour desRead more Related Posts Pourquoi utiliser IPv6? Avantages et cas d’utilisation en entreprise Introduction L'IPv6 prend une importance croissante à mesure que les entreprises se préparent à la croissance à long terme d'Internet. Read more Comment louer des adresses IPv4 et combien cela coûte-t-il ? Techniquement, les adresses IPv4 sont épuisées. Mais comme elles sont absolument essentielles, les entreprises et les organisations ont trouvé des Read more Location d’adresses IPv4 entrantes et sortantes : un guide complet pour les entreprises Comprendre le système de location d'adresses IPv4 aide les entreprises à gérer un espace d'adressage limité, à réduire les risques Read more .related-post {} .related-post .post-list { text-align: left; } .related-post .post-list .item { margin: 5px; padding: 10px; } .related-post .headline { font-size: 18px !important; color: #999999 !important; } .related-post .post-list .item .post_thumb { max-height: 220px; margin: 10px 0px; padding: 0px; display: block; } .related-post .post-list .item .post_title { font-size: 16px; color: #3f3f3f; margin: 10px 0px; padding: 0px; display: block; text-decoration: none; } .related-post .post-list .item .post_excerpt { font-size: 13px; color: #3f3f3f; margin: 10px 0px; padding: 0px; display: block; text-decoration: none; } @media only screen and (min-width: 1024px) { .related-post .post-list .item { width: 30%; } } @media only screen and (min-width: 768px) and (max-width: 1023px) { .related-post .post-list .item { width: 90%; } } @media only screen and (min-width: 0px) and (max-width: 767px) { .related-post .post-list .item { width: 90%; } }
Comment louer des adresses IPv4 et combien cela coûte-t-il ?
Techniquement, les adresses IPv4 sont épuisées. Mais comme elles sont absolument essentielles, les entreprises et les organisations ont trouvé des moyens de continuer à redistribuer les adresses IPv4 existantes. 1.0 Pourquoi opter pour la location d’adresses IPv4 ? La location d’adresses IPv4 est une solution judicieuse pour les entreprises ayant besoin d’adresses IP. Elle est particulièrement avantageuse pour les petites entreprises qui nécessitent plusieurs adresses IP publiques. 2.0 Why IPv4s are SoRead more Related Posts Pourquoi utiliser IPv6? Avantages et cas d’utilisation en entreprise Introduction L'IPv6 prend une importance croissante à mesure que les entreprises se préparent à la croissance à long terme d'Internet. Read more Comment louer des adresses IPv4 et combien cela coûte-t-il ? Techniquement, les adresses IPv4 sont épuisées. Mais comme elles sont absolument essentielles, les entreprises et les organisations ont trouvé des Read more Location d’adresses IPv4 entrantes et sortantes : un guide complet pour les entreprises Comprendre le système de location d'adresses IPv4 aide les entreprises à gérer un espace d'adressage limité, à réduire les risques Read more .related-post {} .related-post .post-list { text-align: left; } .related-post .post-list .item { margin: 5px; padding: 10px; } .related-post .headline { font-size: 18px !important; color: #999999 !important; } .related-post .post-list .item .post_thumb { max-height: 220px; margin: 10px 0px; padding: 0px; display: block; } .related-post .post-list .item .post_title { font-size: 16px; color: #3f3f3f; margin: 10px 0px; padding: 0px; display: block; text-decoration: none; } .related-post .post-list .item .post_excerpt { font-size: 13px; color: #3f3f3f; margin: 10px 0px; padding: 0px; display: block; text-decoration: none; } @media only screen and (min-width: 1024px) { .related-post .post-list .item { width: 30%; } } @media only screen and (min-width: 768px) and (max-width: 1023px) { .related-post .post-list .item { width: 90%; } } @media only screen and (min-width: 0px) and (max-width: 767px) { .related-post .post-list .item { width: 90%; } }

Débloquer la croissance de votre entreprise grâce à l’évolutivité IPv4
In the early days of the internet, a team of engineers developed IPv4. However, they did not foresee the growth of the Internet (Who could have?). Now, we are at a point where we’ve practically run out of IPv4s. To deal with this issue, IPv6 was introduced. But not all devices and networks support IPv6. In response, companies seeking more IPv4 addresses turned to the open market. IP addressRead more Related Posts Pourquoi utiliser IPv6? Avantages et cas d’utilisation en entreprise Introduction L'IPv6 prend une importance croissante à mesure que les entreprises se préparent à la croissance à long terme d'Internet. Read more Comment louer des adresses IPv4 et combien cela coûte-t-il ? Techniquement, les adresses IPv4 sont épuisées. Mais comme elles sont absolument essentielles, les entreprises et les organisations ont trouvé des Read more Location d’adresses IPv4 entrantes et sortantes : un guide complet pour les entreprises Comprendre le système de location d'adresses IPv4 aide les entreprises à gérer un espace d'adressage limité, à réduire les risques Read more .related-post {} .related-post .post-list { text-align: left; } .related-post .post-list .item { margin: 5px; padding: 10px; } .related-post .headline { font-size: 18px !important; color: #999999 !important; } .related-post .post-list .item .post_thumb { max-height: 220px; margin: 10px 0px; padding: 0px; display: block; } .related-post .post-list .item .post_title { font-size: 16px; color: #3f3f3f; margin: 10px 0px; padding: 0px; display: block; text-decoration: none; } .related-post .post-list .item .post_excerpt { font-size: 13px; color: #3f3f3f; margin: 10px 0px; padding: 0px; display: block; text-decoration: none; } @media only screen and (min-width: 1024px) { .related-post .post-list .item { width: 30%; } } @media only screen and (min-width: 768px) and (max-width: 1023px) { .related-post .post-list .item { width: 90%; } } @media only screen and (min-width: 0px) and (max-width: 767px) { .related-post .post-list .item { width: 90%; } }
