IP Allocation Best Practices for Enterprises

Table of Contents
- An essential yet commonly disregarded, crucial component that influences network security and efficient operation is a well-designed IP allocation scheme.
- Scalable growth now calls for the implementation of methodologies like variable-length subnet masking (VLSM) and IPv6 integration planning.
Laying the groundwork with a logical hierarchy
IP address allocation is a more fundamental element that the typically occurs just like an afterthought in the grand architecture of an enterprise network, where debates frequently concentrate on cutting-edge firewalls, zero-trust models, and cloud migrations. The process is historical, organic, as well as chaotic for numerous organizations. Whenever a new office opens, a subnet gets established, and a new project is assigned a random block. However, this ad-hoc approach may result in an intricate network that blocks scalability, creates security policies more challenging to put into effect, and leads to administrative nightmares.
Think about your IP address space as the foundation of your entire digital operation, rather than merely an assortment of numbers. Network engineers must approach IP allocation tactically, just as a city planner would not plan roads without a map. When executed correctly, a well-designed IP scheme is invisible, enabling seamless interaction, simplifying troubleshooting, and providing an established structure for security enforcement. A poorly designed one hinders down innovation and creates risk, becoming an ongoing source of problems. Tim Winters, a senior network architect at the University of New Hampshire InterOperability Laboratory (UNH-IOL), says:
“The biggest mistake we see is companies treating their internal IP address space as an unmanaged wasteland.”
— Tim Winters, University of New Hampshire InterOperability Laboratory (UNH-IOL)
An in-depth review is the initial stage towards successful IP address management. What you do not measure, you cannot under control. This involves documenting each IP subnet which is right now in use, alongside its size, operation, location, and rate of utilization. From fundamental command-line scripts to complicated commercial IP Address Management (IPAM) solutions, there are and are many tools accessible to assist with this discovery process. Inefficiencies could be identified through this starting inventory, such as the wastage of well over 240 addresses while a /24 subnet (254 addresses) gets assigned to a faraway branch office with just ten devices. Establishing a logical hierarchy is the next step shortly after you have a clear picture of where you are now. The strategic allocation of the intellectual property depends regarding this.
The primary goal is to establish an addressing scheme that is compatible with the company’s logical structure. Large companies tend to tailor their IP approach with either geography, business function, or both. For instance, you could figure out that the continent or country code is delimited by the second octet of your private 10.0.0.0/8 space. A specifics city or campus could be represented by the third octet. Individual devices would then be recognized by the fourth octet. This results in concerning right away clarity. An engineer might quickly identify that the device is situated at the main headquarters (12) in London (84) if they observe the address 10.84.12.45. Applying security policies and efficiently routing traffic is made achievable by this hierarchical model.
At this point in time, it’s practically difficult to reach an agreement on technical best practices like Variable-Length Subnet Masking (VLSM).Using the same subnet size everywhere was an accepted method in traditional subnetting, which is highly wasteful. With VLSM, it’s possible to precisely configure subnets of different dimensions by determining the number of hosts required within one’s larger network. A wireless access point might need a /30 subnet (2 addresses) for its point-to-point link, a server rack may need a /29 subnet (6 usable addresses) for its management interfaces, and a large office might need a /23 (510 addresses) for its user devices. All of these can be distributed from a single, perpetual address block with gaps along with inefficiencies thanks to VLSM. As available addresses grow more scarce, mastering VLSM could prove to be the most essential ability for maximizing your IPv4 address space.
The role of dhcp and static assignments
Within these well-designed subnets, the assignment of addresses to individual devices must also be managed carefully. The foundation of user devices that include laptops, phones, and tablets is the Dynamic Host Configuration Protocol (DHCP). It simplifies the process, prevents human error, and enables successful address reuse. Cependant not everything ought to have a dynamic. Establishing a particular range for static assignments within each subnet is the best obviously for action in this instance. In a /24 subnet, for example, you can set separate addresses.1 to.30 for servers and network infrastructure, while DHCP handles addresses.50 to.254. This defines a transparent and consistent pattern that every one of the team’s scientists will understand.
The importance of documentation in ip management
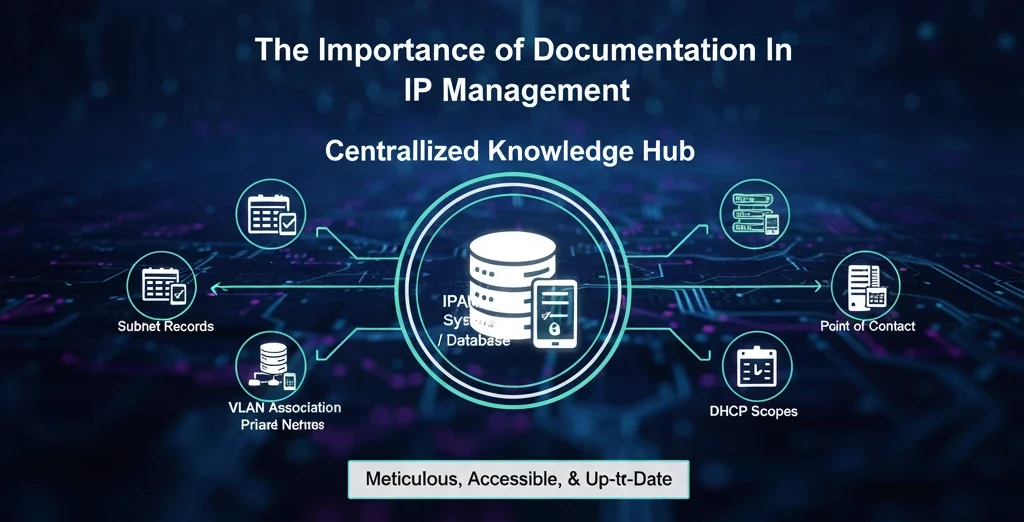
A perfect IP plan is useless if it only exists in one person’s head or in a stale spreadsheet on a forgotten server. Meticulous, accessible, and up-to-date documentation is the glue that holds everything together. The only trustworthy source of knowledge regarding the entirety of your IP address space should be your documentation. This includes an IPAM system or database that maintains records of every subnet, its VLAN association, its DHCP scope, its purpose, and its point of contact, and also detailed network diagrams that graphically depict your subnets and their relationships. The documentation needs to be updated concurrently with each change. Network management becomes transformed from a dark art into a standardized and auditable technique by this discipline.
“The gap between a good network and a great network often comes down to documentation,” notes Jennifer English, a senior analyst at IDC covering enterprise networks. “In times of crisis, when a network is under attack or a critical link has failed, the team does not have time to go on a scavenger hunt for information. Well-maintained IP documentation allows for rapid triage and resolution. It’s a force multiplier for your network operations centre.”
Establishing a robust IP address management policy
Establishing an a thorough IP Address Management (IPAM) policy is a vital—and yet commonly overlooked— component of strategic IP management. This document is your organization’s formal playbook, outlining the standards and procedures that all of your employees—from networking and security to cloud operations and development—must adhere to. Even the most meticulously planned IP plan may rapidly fall aside simply because of ad hoc exceptions, special requests, and a general lack of coordination in the lack of such a governing policy, reintroducing the network to the very state of chaos you attempted to remove. A powerful technical design has been transformed into an operational standard that is both enforceable and permanent from the policy. Clearly establishing roles and duties is the fundamental stage toward establishing an effective IPAM policy.
It ought to indicate who in the business has the right to request a block of IP addresses that remain static or a new subnet. It must additionally state who has the authority to grant these requests, who is in in charge of the technical implementation, as well as—most important of all—who is in in charge of looking after the IPAM system and central documentation. In big businesses, where different parts may have conflicting priorities and have no knowledge of the global network architecture, it is crucial to establish this clear request-and-approval workflow. The process is converted from one of unauthorized requests and tribal knowledge to an uniform, repeatable, and auditable business process by avoiding the uncontrolled proliferation of IP allocations while also making sure that every change is carefully evaluated, supported, and tracked.
The policy have to ask stringent operational standards in along with governance. Strict naming standards have to be obeyed by all network entities in light of this. As opposed to using a mysterious internal code, a subnet should have a name that accurately reflects its location and purpose, such as UK-LON-OFFICE-USER-VLAN110. An engineer are able to rapidly recognize a device from its IP address alone while device hostnames adhere to convention and include location and function codes. The following significantly reduces the mean time to resolution during an outage. Finally, a regular review and reclamation process must be defined in the policy. Projects come to an end, devices is retired, and offices are reduced; networks are natural. These retired assets’ IP addresses need to be meticulously discovered and brought once more to the pool of available addresses.
The looming shadow and bright future of IPv6
Without addressing IPv6, the elephant in the room, no discussion of present-day IP allocation is complete. Organizations are starting to get IPv6 address space from their service providers as an outcome of the concrete reality of IPv4 address exhaustion. It’s a common mistake to make decisions of IPv6 as a separate, future project that can be detached. Planning for IPv6 integration right away as you can is the best option for action. Giving away IPv6 calls for a completely different method of considering. With 340 undecillion addresses, the address space is so broad that conservation is no longer a concern. The entire a focus switches to logical structure and synthesis. Making management and dual-stack operation simple, your IPv6 plan ought to run in parallel with your IPv4 hierarchy, ideally mirroring it.
For the majority of companies, it is recommended to run IPv4 and IPv6 simultaneously (a configuration dubbed dual-stack), to ensure a smooth transition. Developing competence in IPv6 addressing now can assist the way you stay away a hasty, unprepared migration later.
Trusted IPv4 Leasing for Business Growth
Get enterprise-grade IPv4 space quickly, with seamless deployment and end-to-end management.
Get Started with i.leaseFAQs
What is the first step if our current IP allocation is a mess?
The absolute first step is to perform a comprehensive audit using network discovery tools to map out exactly what you have. Include all the networks and network subnets that are at present in use, in addition with their sizes, purposes, and usage rates. What you cannot comprehend, you are unable to fix. Following that, establish a new plan to define the logical hierarchy and start carefully adapting the moving elements of the network to this new scheme, beginning with low-risk areas.
How does good IP allocation improve network security?
A logical and consistent IP scheme allows for the creation of clear and effective security policies. Subnets may be utilized to establish firewall rules, thereby rendering it straightforward to enable or disable traffic from particular places or business units. Furthermore, it makes unusual behavior more apparent; security monitoring systems are going to recognize it right away if a device in the 10.84.0.0/16 range (London) suddenly wants to authenticate from a server subnet in a different country.
What is the difference between public and private IP addressing, and how should we use them?
Public IP addresses are globally routable on the internet and are a finite resource. Only devices that require to be easily accessible from the internet, including your mail servers or public web site, should use them as well. For the purpose to maintain your public IPs and add a layer of anonymity and security through Network Address Translation (NAT), the vast majority of your devices should use private addresses.
When should we consider using an IPAM tool?
An IPAM tool becomes highly recommended if you are in the position to manage more than certain subnets. It offers you an advanced platform for monitoring, distributing, and conserving IP address space, instead of spreadsheets that can be prone to mistakes. For entire lifecycle management of your IP resources, it commonly integrates with DNS and DHCP servers, serves as a centrally located database, and may assist in avoiding disputes.
Why can’t we just put off implementing IPv6?
While NAT and private addressing have delayed the urgency for IPv4, the industry is steadily moving towards IPv6.IPv6 has become native to many new mobile and Internet of Things devices. If you put away planning, you could have to deal with the consequences of rash, expensive, and inadequately carefully planned implementation later. A controlled, strategic dual-stack deployment that was achievable by early planning provides seamless connectivity and secures your network for several decades to come.
Related Blogs
相关文章
企业入站与出站 IPv4 租赁完整指南
租赁 IPv4 地址可以转移部分伴随完全所有权而来的风险。例如,购买地址可能会让组织暴露于价格波动、长期贬值风险以及信誉管理责任之中。通过 i.Lease 进行租赁,企业可以降低这些风险暴露,并在明确期限内维持可预测的成本,从而支持更可靠的预算规划和风险管理实践。 这种方式也简化了基础设施管理,因为租赁供应商通常会负责滥用监控、信誉检查和注册机构协调,使承租方能够专注于核心业务功能,而不是 IP 资产管理。 IPv4 租赁并不限于单一行业。托管服务商、云平台、电信公司、SaaS 公司和网络安全企业都可以从租赁中受益。例如,托管服务商可以在无需大量前期投资的情况下扩展服务器部署,而网络安全公司则可以根据客户需求灵活增加地址空间,而无需承诺完全购买。 在销售、营销和监管测试中,租赁允许组织在特定地区试运行部署,而无需投入大量资本。这种战略灵活性支持创新,同时帮助企业在 IPv4 稀缺持续存在的市场中保持韧性。 利用 i.Lease 进行 IPv4 租赁管理的好处非常清楚:具成本效益的访问、快速部署、信誉安全、可扩展性、地理多样性和持续支持。在 IPv4 地址稀缺且直接购买成本高昂的环境中,通过值得信赖的平台进行租赁,使组织能够维持连接、按需扩展基础设施,并高效管理资源。 通过将 IPv4 租赁视为基础设施规划的重要组成部分,而不是临时替代方案,企业可以在应对 IPv4 市场现实的同时,实现运营稳定性和财务可预测性。 入站与出站 IPv4 租约:企业完整指南 在 Internet Protocol version 4(IPv4)枯竭后的时代,对于需要地址空间但不想直接拥有地址资产的组织来说,租赁已经变得非常重要。虽然 IPv6 仍在逐步采用,但由于兼容性需求、旧有基础设施以及较慢的迁移经济性,IPv4 仍然深深嵌入全球路由体系中。 对于企业而言,理解入站和出站 IPv4 租赁之间的区别,对于管理成本、安全性和运营连续性至关重要。本指南将结合实际背景解释两者,并与业界关于注册层脆弱性和连续性风险的更广泛观察保持一致。 什么是IPv4租约? IPv4 租赁是指按约定期限租用 IPv4 地址空间,而不是直接购买地址块。企业根据合同条款从出租方(拥有可用 IPv4 地址容量的组织或经纪商)租赁地址,合同条款授予其使用权。 租赁之所以被广泛使用,是因为全球 IPv4 地址池多年来一直处于枯竭状态。2011 年,互联网号码分配机构 (IANA) 将最后剩余的地址块分配给了区域互联网注册管理机构 (RIR),此后,企业再也无法按需获得大量新的地址分配。 入站 IPv4 地址租赁—引入地址 入站租赁是指企业从供应商处获取 IPv4 地址,用于自身业务使用。 企业为什么选择入站租赁 当组织现有的 IPv4 资源不足以支持以下需求时,通常会选择入站租赁: 扩展数字服务 支持新的基础设施 维持依赖 IPv4 的应用程序 Related Posts 企业入站与出站 IPv4 租赁完整指南 租赁 IPv4 地址可以转移部分伴随完全所有权而来的风险。例如,购买地址可能会让组织暴露于价格波动、长期贬值风险以及信誉管理责任之中。通过 i.Lease 进行租赁,企业可以降低这些风险暴露,并在明确期限内维持可预测的成本,从而支持更可靠的预算规划和风险管理实践。这种方式也简化了基础设施管理,因为租赁供应商通常会负责滥用监控、信誉检查和注册机构协调,使承租方能够专注于核心业务功能,而不是 IP 资产管理。IPv4 租赁并不限于单一行业。托管服务商、云平台、电信公司、SaaS 公司和网络安全企业都可以从租赁中受益。例如,托管服务商可以在无需大量前期投资的情况下扩展服务器部署,而网络安全公司则可以根据客户需求灵活增加地址空间,而无需承诺完全购买。在销售、营销和监管测试中,租赁允许组织在特定地区试运行部署,而无需投入大量资本。这种战略灵活性支持创新,同时帮助企业在 IPv4 稀缺持续存在的市场中保持韧性。利用 i.Lease 进行 IPv4 租赁管理的好处非常清楚:具成本效益的访问、快速部署、信誉安全、可扩展性、地理多样性和持续支持。在 IPv4 地址稀缺且直接购买成本高昂的环境中,通过值得信赖的平台进行租赁,使组织能够维持连接、按需扩展基础设施,并高效管理资源。通过将 IPv4 租赁视为基础设施规划的重要组成部分,而不是临时替代方案,企业可以在应对 IPv4 Understanding Operational Risk in IPv4 Address Markets IPv4 has long stopped being a simple technical identifier system. It has become a constrained, priced, and operationally embedded infrastructure Por qué la mayoría de las empresas están expuestas accidentalmente al riesgo de fallo en la asignación de IPv4 La escasez de IPv4 es ampliamente comprendida. Lo que muchas empresas aún subestiman es el riesgo de continuidad relacionado con .related-post {} .related-post .post-list { text-align: left; } .related-post .post-list .item { margin: 5px; padding: 10px; } .related-post .headline { font-size: 18px !important; color: #999999 !important; } .related-post .post-list .item .post_thumb { max-height: 220px; margin: 10px 0px; padding: 0px; display: block; } .related-post .post-list .item .post_title { font-size: 16px; color: #3f3f3f; margin: 10px 0px; padding: 0px; display: block; text-decoration: none; } .related-post .post-list .item .post_excerpt { font-size: 13px; color: #3f3f3f; margin: 10px 0px; padding: 0px; display: block; text-decoration: none; } @media only screen and (min-width: 1024px) { .related-post .post-list .item { width: 30%; } } @media only screen and (min-width: 768px) and (max-width: 1023px) { .related-post .post-list .item { width: 90%; } } @media only screen and (min-width: 0px) and (max-width: 767px) { .related-post .post-list .item { width: 90%; } }
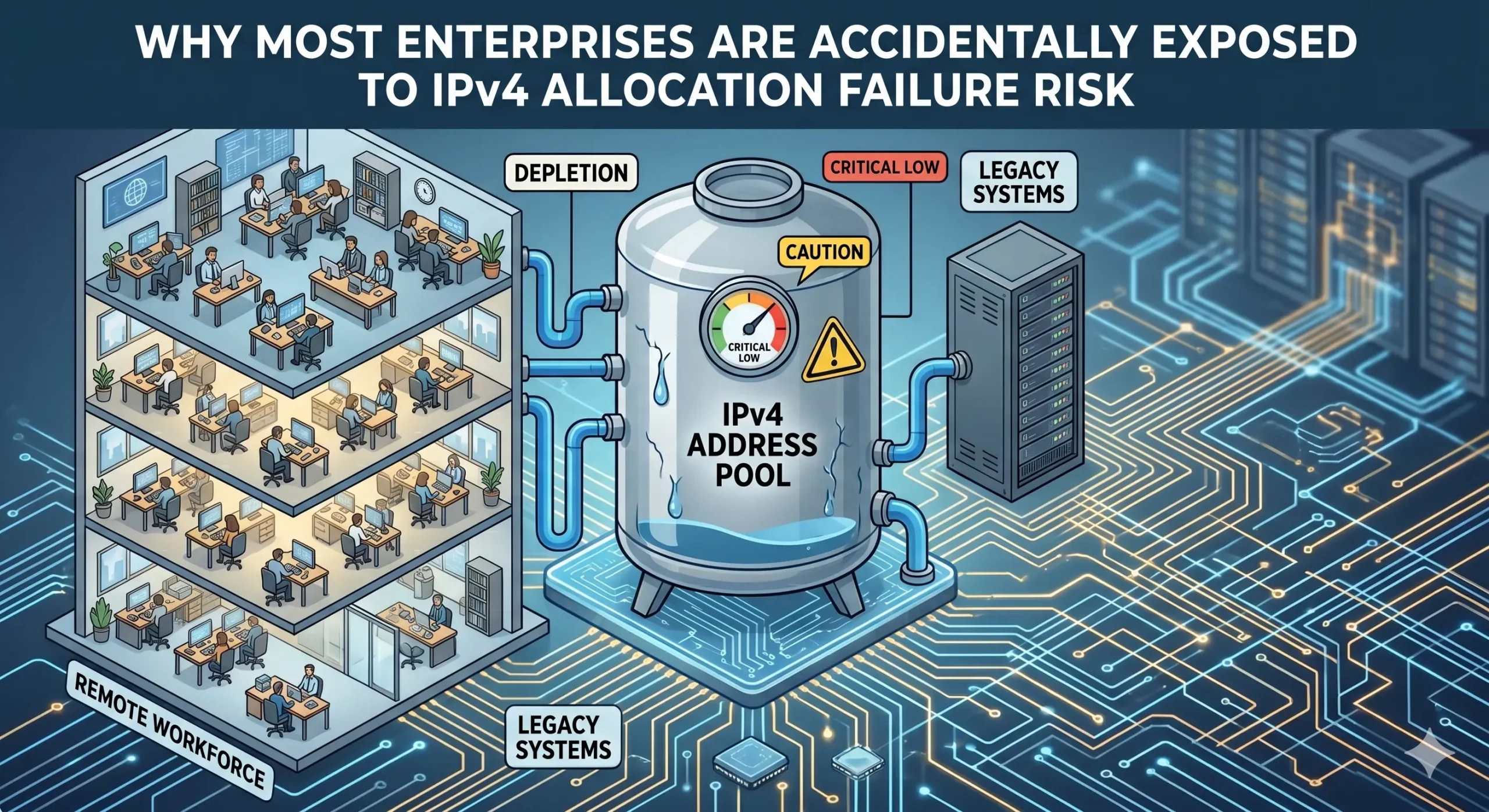
大多数企业为何会意外面临 IPv4 地址分配失败的风险
IPv4 稀缺性已被广泛理解。许多企业仍然低估的是:地址资源如何被治理和维护所带来的连续性风险。 企业往往在持续使用 IPv4 资源的同时,并没有完全看清支撑这些分配的连续性条件。 对租赁、转让和供应商管理型基础设施的依赖不断增加,正在将 IPv4地址分配 重塑为一个长期治理问题。 IPv4地址分配已悄然成为连续性问题 对许多企业 IT 团队来说,IPv4 地址看起来仍然在运营上保持稳定。 应用程序仍然可以访问。云平台继续扩展。连接服务供应商在没有明显中断的情况下提供服务。从外部看,互联网似乎仍像过去一样运行。 然而,在这种运营稳定性之下,IPv4地址分配的结构已经发生了根本变化。 可自由分配的 IPv4 空间耗尽早已不是新闻。American Registry for Internet Numbers (ARIN) 于 2015 年耗尽其可用 IPv4 池,而 RIPE NCC 于 2019 年随后耗尽。(arin.net)(ripe.net) 取代旧分配环境的,是一个围绕以下内容建立的更分层运营模式: 转让 租赁 供应商管理型地址 回收 二级分配安排 对许多组织来说,这些变化是逐渐发生的,因此其背后连续性假设的转变很大程度上没有被注意到。因此,企业现在面临的并不只是地址稀缺,而是越来越暴露于 IPv4地址分配失败风险 ——也就是连续性、可携带性或长期运营灵活性变得比预期更不确定的情况。 问题通常是可见性,而不是即时短缺 这个问题仍然被低估的原因之一,是大多数企业并不会把 IPv4 scarcity 体验成即时宕机问题。基础设施仍在运行。 相反,风险通常会在转型时刻浮现: 云迁移 供应商整合并购 区域扩展 基础设施重组 合规驱动的迁移 在这些情况下,组织有时会发现,运营使用和连续性可见性并不是同一回事。企业可能已经在生产环境中积极使用 IPv4 资源多年,却对以下方面了解有限: 分配来源 注册机构关系 转让历史 可携带性条件 上游依赖 续期风险暴露 这并不一定表示运营实践不佳。现代基础设施环境随着时间推移变得越来越抽象。云采用和软件定义基础设施简化了部署,但也减少了企业与支撑互联网号码资源的治理层之间的直接互动。 IPv4地址分配已从采购演变为管理责任 过去,组织通常把IPv4地址分配视为直接的运营需求。额外地址空间往往可以通过 Regional Internet Registries (RIRs) Related Posts Understanding Operational Risk in IPv4 Address Markets IPv4 has long stopped being a simple technical identifier system. It has become a constrained, priced, and operationally embedded infrastructure La Running-Code Primacy: por qué el arrendamiento de IPv4 debe juzgarse mediante pruebas operativas El arrendamiento de IPv4 suele comenzar con una pregunta simple: ¿Puede este proveedor darnos las direcciones? Pero para las empresas Pourquoi la plupart des entreprises sont exposées accidentellement au risque d’échec d’attribution d’adresse IPv4 La rareté de l’IPv4 est largement comprise. Ce que de nombreuses entreprises sous-estiment encore, c’est le risque de continuité lié .related-post {} .related-post .post-list { text-align: left; } .related-post .post-list .item { margin: 5px; padding: 10px; } .related-post .headline { font-size: 18px !important; color: #999999 !important; } .related-post .post-list .item .post_thumb { max-height: 220px; margin: 10px 0px; padding: 0px; display: block; } .related-post .post-list .item .post_title { font-size: 16px; color: #3f3f3f; margin: 10px 0px; padding: 0px; display: block; text-decoration: none; } .related-post .post-list .item .post_excerpt { font-size: 13px; color: #3f3f3f; margin: 10px 0px; padding: 0px; display: block; text-decoration: none; } @media only screen and (min-width: 1024px) { .related-post .post-list .item { width: 30%; } } @media only screen and (min-width: 768px) and (max-width: 1023px) { .related-post .post-list .item { width: 90%; } } @media only screen and (min-width: 0px) and (max-width: 767px) { .related-post .post-list .item { width: 90%; } }

运行代码优先性:为什么 IPv4 租约应该以运行证明来评判
IPv4 租赁通常始于一个简单的问题: 这个供应商能不能给我们这些地址? 但对于依赖 IPv4 来支持托管、VPN、SaaS、云、电信、安全、电子邮件投递或面向客户平台的企业来说,这个问题还不够。 更好的问题是: 这个 IPv4 结构能否证明它在运营上可行? 这正是 Running-Code Primacy 重要的地方。 Running-Code Primacy 意味着,真实运行中的运营现实,应该优先于机构语言、销售说法、流程上的安心感或抽象承诺。在 IPv4 地址市场中,企业不应只通过价格、地址块大小或精美的销售页面来判断 IPv4 供应商。企业应该通过证据来判断:该地址空间是否可以路由、续期、记录、支持,并在生产环境中保持稳定。 对 i.lease 来说,商业启示很直接: IPv4 访问应该通过运营证明来评估,而不只是纸面上的可用性。 什么是 Running-Code Primacy? Running-Code Primacy 是一种理念,认为互联网治理和资源协调应始终以正在运行的网络为基础。 互联网工程传统长期重视实际实现,而不是理论设计。Running-Code Primacy 背后的原则主张,号码资源协调应通过运行中网络的技术需求来解释,而不是通过广泛的机构权威来解释。 对于 IPv4 地址市场,这一原则可以转化为商业语言: 不要只依赖说法。要寻找证明。 供应商可能会说 IPv4 地址块可用。但它能否支持路由?能否提供文件?能否说明来源控制?能否处理续期?当信誉或滥用问题出现时,它能否回应?部署之后,它能否保持客户网络稳定? Running-Code Primacy 并不意味着忽略合同、记录或治理。这些仍然重要。它意味着最终测试应该是运营现实。 如果一个 IPv4 安排无法支持正在运行的网络,那就还不够。 为什么 IPv4 买家和租户应该重视 IPv4 不只是基础设施预算中的一个项目。 对许多企业来说,IPv4 支撑着真实系统: 托管平台 云服务 VPN 网关 SaaS 应用 企业访问控制 电子邮件基础设施 电信系统 安全工具 面向客户的网站 API 端点 监控系统 Related Posts 企业入站与出站 IPv4 租赁完整指南 租赁 IPv4 地址可以转移部分伴随完全所有权而来的风险。例如,购买地址可能会让组织暴露于价格波动、长期贬值风险以及信誉管理责任之中。通过 i.Lease 进行租赁,企业可以降低这些风险暴露,并在明确期限内维持可预测的成本,从而支持更可靠的预算规划和风险管理实践。这种方式也简化了基础设施管理,因为租赁供应商通常会负责滥用监控、信誉检查和注册机构协调,使承租方能够专注于核心业务功能,而不是 IP 资产管理。IPv4 租赁并不限于单一行业。托管服务商、云平台、电信公司、SaaS 公司和网络安全企业都可以从租赁中受益。例如,托管服务商可以在无需大量前期投资的情况下扩展服务器部署,而网络安全公司则可以根据客户需求灵活增加地址空间,而无需承诺完全购买。在销售、营销和监管测试中,租赁允许组织在特定地区试运行部署,而无需投入大量资本。这种战略灵活性支持创新,同时帮助企业在 IPv4 稀缺持续存在的市场中保持韧性。利用 i.Lease 进行 IPv4 租赁管理的好处非常清楚:具成本效益的访问、快速部署、信誉安全、可扩展性、地理多样性和持续支持。在 IPv4 地址稀缺且直接购买成本高昂的环境中,通过值得信赖的平台进行租赁,使组织能够维持连接、按需扩展基础设施,并高效管理资源。通过将 IPv4 租赁视为基础设施规划的重要组成部分,而不是临时替代方案,企业可以在应对 IPv4 Risques liés au renouvellement d’IPv4 : quand le manque de responsabilisation se transforme en trahison du code en cours d’exécution La plupart des entreprises entrent sur le marché IPv4 avec un objectif simple. Elles ont besoin d’adresses. Peut-être en ont-elles 大多数企业为何会意外面临 IPv4 地址分配失败的风险 IPv4 稀缺性已被广泛理解。许多企业仍然低估的是:地址资源如何被治理和维护所带来的连续性风险。 企业往往在持续使用 IPv4 资源的同时,并没有完全看清支撑这些分配的连续性条件。 对租赁、转让和供应商管理型基础设施的依赖不断增加,正在将 IPv4地址分配 重塑为一个长期治理问题。 IPv4地址分配已悄然成为连续性问题 对许多企业 IT 团队来说,IPv4 地址看起来仍然在运营上保持稳定。 应用程序仍然可以访问。云平台继续扩展。连接服务供应商在没有明显中断的情况下提供服务。从外部看,互联网似乎仍像过去一样运行。 然而,在这种运营稳定性之下,IPv4地址分配的结构已经发生了根本变化。 可自由分配的 IPv4 空间耗尽早已不是新闻。American Registry for .related-post {} .related-post .post-list { text-align: left; } .related-post .post-list .item { margin: 5px; padding: 10px; } .related-post .headline { font-size: 18px !important; color: #999999 !important; } .related-post .post-list .item .post_thumb { max-height: 220px; margin: 10px 0px; padding: 0px; display: block; } .related-post .post-list .item .post_title { font-size: 16px; color: #3f3f3f; margin: 10px 0px; padding: 0px; display: block; text-decoration: none; } .related-post .post-list .item .post_excerpt { font-size: 13px; color: #3f3f3f; margin: 10px 0px; padding: 0px; display: block; text-decoration: none; } @media only screen and (min-width: 1024px) { .related-post .post-list .item { width: 30%; } } @media only screen and (min-width: 768px) and (max-width: 1023px) { .related-post .post-list .item { width: 90%; } } @media only screen and (min-width: 0px) and (max-width: 767px) { .related-post .post-list .item { width: 90%; } }
