How to check the risk score of an IP block before you lease it

The current era faces IPv4 address scarcity. Organizations must verify IP block risk scores. Tools like i.lease help complete this verification. This process prevents blacklisting problems. It also ensures reliable network leasing for enterprises.
Table of Contents
-Evaluate IP reputation using available tools. Platforms like i.lease provide this capability. This approach helps avoid abuse-tainted blocks. It also maintains regulatory compliance.
-Proactive risk assessment reduces financial losses. These losses can reach multimillion-pound amounts. They stem from spam blacklists and DDoS vulnerabilities. Leased IPv4 assets often face these threats.
What is an IP block risk score?
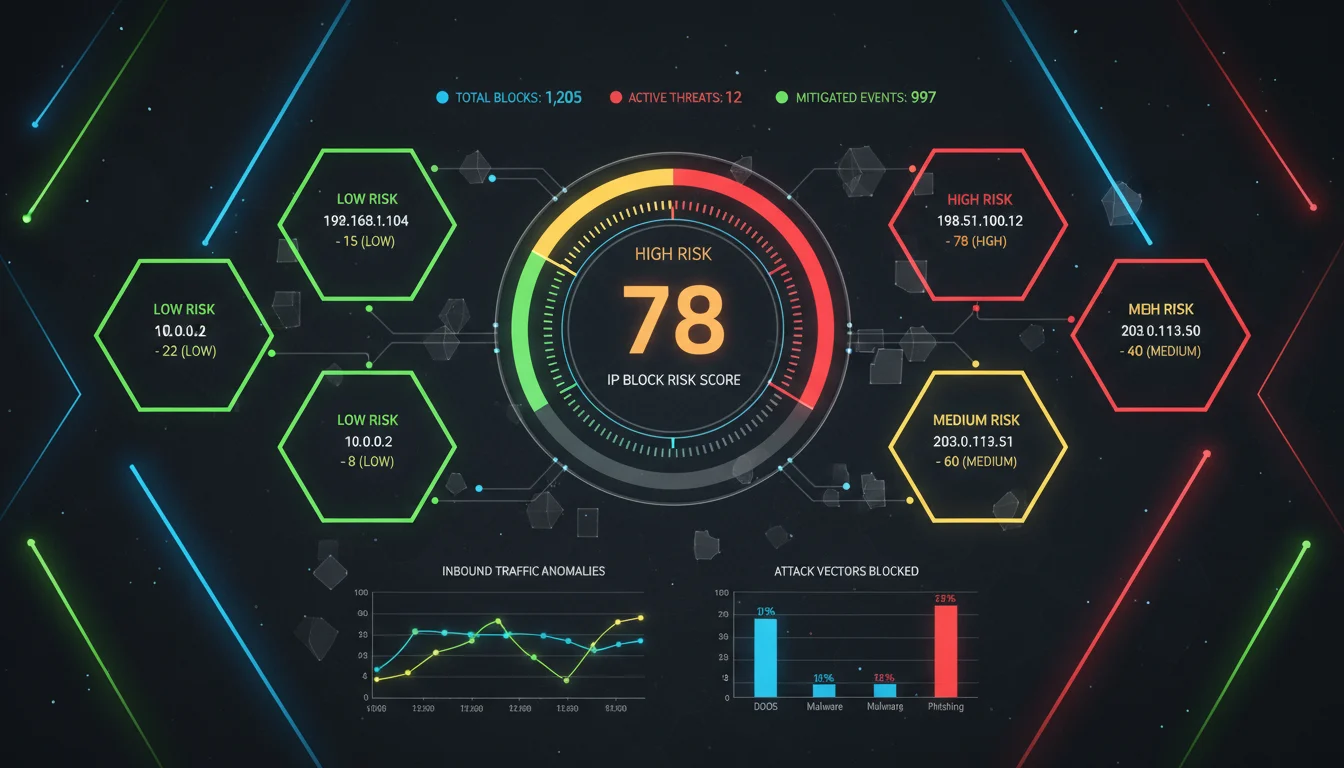
An IP block risk score measures potential threats. It evaluates ranges of IP addresses. Networks use these addresses for routing. They also enable connectivity. This numerical metric uses a 0-100 scale. It estimates involvement in malicious activities. These activities include spam operations. Phishing campaigns represent another threat. Botnet operations also affect scores.
Multiple factors influence the score. Historical abuse records provide important data. Geolocation anomalies create concerns. Connections to known threat actors matter. Overall reputation data contributes significantly. This data comes from global threat intelligence feeds.
IPv4 addresses continue to diminish. Leasing activity has increased substantially. Platforms like i.lease offer over 8 million IPs. Risk score auditing remains essential. Lessees face serious dangers without it. They might inherit compromised blocks. These blocks can reduce email delivery rates. They may also activate firewall restrictions.
Cybersecurity experts make comparisons. They describe these scores as credit ratings. This applies to digital infrastructure. Organizations can prioritize secure assets. Low scores indicate clean blocks. Scores between 0-30 show trustworthiness. High scores above 70 require avoidance.
Practical implementation involves multiple elements. Risk scoring uses blacklist data. Sources include Spamhaus and SURBL. Behavioral patterns provide additional information. Unusual traffic volumes receive attention. Leasing services like i.lease use automation. They calculate scores in real time. Historical data combines with AI predictions. This mixture forecasts future vulnerabilities.
Why check IP risk scores before leasing?
IPv4 exhaustion continues to progress. RIPE NCC forecasts deterioration by 2030. Leasing markets now reach £700 million annually. Unchecked IP blocks create network dangers. Blacklisting stops outbound email transmission. Industry standards show 60% disruption.
Risk score verification ensures regulation compliance. GDPR represents one example. Poor IP management brings financial penalties. Fines can reach 4% of global turnover.
Enterprises lease IPs for various reasons. Cloud scaling requires additional addresses. E-commerce expansions need more resources. Service level agreements must remain valid. Compromised blocks intensify DDoS attacks. Ponemon Institute studies quantify costs. Downtime expenses reach £20,000 hourly.
Platforms like i.lease emphasize pre-lease audits. Statistics show significant problems. Twenty-two percent of leased IPs receive abuse reports. This occurs within the first quarter. Vigilance protects operational integrity. It also maintains asset value long-term. Clean reputations increase resale value. Premiums reach 20-30% higher.
Threat landscapes continue evolving. AI-driven phishing attacks emerge. Dynamic scoring becomes necessary. Ignoring this step creates cascade failures. A single high-risk block causes contamination. This affects entire /24 subnets. Costly migrations become unavoidable.
The consequences of leasing high-risk IP blocks
Unvetted IP blocks create operational damage. Blacklisting incidents represent 60% of abuse cases. Email deliverability drops immediately. Marketing emails experience 90% reduction. Return Path data confirms this impact.
Financial institutions face particular challenges. They rely on IP-trusted transactions. Fraud incidents increase suddenly. A UK bank experienced £5 million in chargebacks. One tainted block caused this in 2024.
Reputation harm persists over time. ARIN documentation shows increased risk. Transferred IPs face 4-25 times more blacklisting. Trust erodes with internet service providers. Partner relationships suffer damage.
Legal consequences create additional burdens. CAN-SPAM violations bring financial penalties. Fines reach £10,000 per email. Operational demands increase significantly. High-risk blocks require continuous monitoring. IT resources shift from innovation. Remediation becomes the primary focus.
Specific examples demonstrate these problems. A European retailer experienced difficulties in 2023. Their /22 block received phishing flags. Online sales stopped for 48 hours. Financial losses reached £1.2 million. These incidents highlight critical needs. Pre-lease checks remain absolutely essential. i.lease best practices advocate this approach.
Step-by-step guide: How to check IP block risk scores
IP block risk assessment requires systematic methods. It combines free tools with professional services. WHOIS lookups provide initial information. ARIN and RIPE databases serve this purpose. They confirm ownership details. Routing history becomes visible. Frequent transfers indicate potential problems.
Blacklist scanning represents the next phase. APIVoid’s IP Reputation Check works effectively. This free tool references 50 lists. It identifies spam and malware connections. Users input CIDR notation. Example format: 192.0.2.0/24. The tool generates 0-100 scores. Values above 50 require deeper investigation.
Geolocation analysis adds another layer. IP2Location detects high-risk origins. Datacenters in sanctioned regions raise concerns. Comprehensive analysis needs advanced tools. Phonexa’s IP Fraud Score provides help. It includes proxy detection capabilities. VPN usage patterns receive evaluation.
Final validation uses threat intelligence platforms. IPQualityScore offers reliable service. API-driven scores update hourly. This multi-layered approach requires 15-30 minutes. It protects lessees from common pitfalls. i.lease users benefit particularly.
Leveraging i.lease for seamless risk assessment
Specialized platforms streamline risk evaluation. i.lease integrates scoring tools directly. Automated blacklist queries save time. Reputation monitoring occurs continuously. The dashboard accepts instant CIDR uploads. Scores derive from proprietary data feeds. Spamhaus information combines with AI predictions.
Cost structures remain reasonable. A /24 block costs £100 monthly. Pre-lease audits involve minimal fees. Abuse risks decrease by 70%.
User advantages include verified lessors. KYC procedures ensure cleaner blocks. The platform identifies high-risk assets immediately. Replacement options occur within 24 hours. Complete management helps smaller businesses. SMEs often lack internal expertise.
Performance metrics show improvements. i.lease reduces false positives by 40%. This builds trust in leasing markets. Thirty percent of leases typically fail reputation tests.
Expert insights: Voices on IP reputation in leasing
Cybersecurity experts emphasize careful checking. Dr. Eric Cole of Cyber Crisis provides analysis. He compares IP risk scoring to credit evaluation. Security teams can prioritize responses. Network protection becomes more efficient.
James Lyne from Sophos adds perspective. IP reputation enables threat prioritization. Investigation efficiency improves significantly. Incident response becomes more effective. Leasing contexts benefit from this approach. Abuse escalation prevents more easily.
Experts like Dr. Eric Cole, James Lyne, and Vincentas Grinius agree that strong IP risk scoring and strict abuse controls are essential for prioritizing threats, speeding investigations, and protecting monetization in IP leasing
— Dr. Eric Cole, James Lyne, and Vincentas Grinius
Dr. Vasileios Giotsas from Lancaster University notes statistics. IPs face 4-25 times more blacklisting after transfer. Reputations damage accordingly. These insights come from ARIN collaborations. Pre-lease diligence remains clearly necessary.
Best practices for ongoing IP monitoring post-lease
Lease completion requires continued vigilance. Automated alerts provide essential monitoring. GlockApps IP Blacklist Check serves this purpose. Weekly scanning identifies new listings. Usage policies need enforcement. Blocks should serve whitelisted applications only. High-volume spam operations must avoid.
Provider partnerships offer advantages. i.lease provides 24/7 monitoring services. They managed 22,000 abuse incidents in Q3 2022. Allocation diversification across regions helps. Single-block failures become less damaging.
Team training ensures better detection. Anomaly recognition skills develop properly. Sudden traffic spikes often precede blacklists. Budget planning should include remediation. Five to ten percent of leasing costs works adequately. Swift IP rotations become possible.

Future trends in IP leasing and risk evaluation
Artificial intelligence will transform scoring. Machine learning will analyze vast datasets. Blockchain technology will track block histories. Spoofing incidents will reduce significantly.
Sustainability considerations will grow important. Green leasing will favor low-carbon datacenters. Eco-scores will become standard measurements. i.lease predicts widespread analytics adoption. Eighty-five percent of leases will use predictive methods by 2025.
IP address resources should be evaluated not only on availability and price, but on their historical usage, governance traceability, and potential risk exposure across the network ecosystem.
— based on Heng Lu’s analysis of IP governance
Quantum computing presents new challenges. Post-quantum encryption will become essential. Scoring algorithms will require updating. Enterprises must adopt these trends. Platforms like i.lease provide necessary tools. Network future-proofing becomes achievable.
Trusted IPv4 Leasing for Business Growth
Get enterprise-grade IPv4 space quickly, with seamless deployment and end-to-end management.
Get Started with i.leaseFAQs
What factors influence an IP block's risk score?
Historical abuse records affect scores. Geolocation data contributes significantly. Threat actor connections matter. Traffic patterns provide indications. Scores range from 0 to 100. Higher numbers show greater malicious potential.
How often should you check IP risk scores before leasing?
Pre-lease checking remains mandatory. Post-lease verification should occur weekly. Tools like APIVoid provide real-time updates. Emerging threats become detectable.
Can platforms like i.lease automate risk assessments?
Yes, automation represents a key feature. Blacklist scanning occurs automatically. AI predictions flag potential issues. Clean block swaps happen instantly.
What if a leased IP block gets blacklisted?
Rotation to new allocations becomes necessary. Providers facilitate this process. Remediation costs average £5,000. Preventive checking avoids these expenses.
Is IP risk scoring relevant for IPv6 leasing too?
Relevance continues growing. IPv6 adoption increases steadily. Current focus remains on IPv4. Tools like IPQualityScore now evaluate both protocols.
Related Blogs
相关文章
企业入站与出站 IPv4 租赁完整指南
租赁 IPv4 地址可以转移部分伴随完全所有权而来的风险。例如,购买地址可能会让组织暴露于价格波动、长期贬值风险以及信誉管理责任之中。通过 i.Lease 进行租赁,企业可以降低这些风险暴露,并在明确期限内维持可预测的成本,从而支持更可靠的预算规划和风险管理实践。 这种方式也简化了基础设施管理,因为租赁供应商通常会负责滥用监控、信誉检查和注册机构协调,使承租方能够专注于核心业务功能,而不是 IP 资产管理。 IPv4 租赁并不限于单一行业。托管服务商、云平台、电信公司、SaaS 公司和网络安全企业都可以从租赁中受益。例如,托管服务商可以在无需大量前期投资的情况下扩展服务器部署,而网络安全公司则可以根据客户需求灵活增加地址空间,而无需承诺完全购买。 在销售、营销和监管测试中,租赁允许组织在特定地区试运行部署,而无需投入大量资本。这种战略灵活性支持创新,同时帮助企业在 IPv4 稀缺持续存在的市场中保持韧性。 利用 i.Lease 进行 IPv4 租赁管理的好处非常清楚:具成本效益的访问、快速部署、信誉安全、可扩展性、地理多样性和持续支持。在 IPv4 地址稀缺且直接购买成本高昂的环境中,通过值得信赖的平台进行租赁,使组织能够维持连接、按需扩展基础设施,并高效管理资源。 通过将 IPv4 租赁视为基础设施规划的重要组成部分,而不是临时替代方案,企业可以在应对 IPv4 市场现实的同时,实现运营稳定性和财务可预测性。 入站与出站 IPv4 租约:企业完整指南 在 Internet Protocol version 4(IPv4)枯竭后的时代,对于需要地址空间但不想直接拥有地址资产的组织来说,租赁已经变得非常重要。虽然 IPv6 仍在逐步采用,但由于兼容性需求、旧有基础设施以及较慢的迁移经济性,IPv4 仍然深深嵌入全球路由体系中。 对于企业而言,理解入站和出站 IPv4 租赁之间的区别,对于管理成本、安全性和运营连续性至关重要。本指南将结合实际背景解释两者,并与业界关于注册层脆弱性和连续性风险的更广泛观察保持一致。 什么是IPv4租约? IPv4 租赁是指按约定期限租用 IPv4 地址空间,而不是直接购买地址块。企业根据合同条款从出租方(拥有可用 IPv4 地址容量的组织或经纪商)租赁地址,合同条款授予其使用权。 租赁之所以被广泛使用,是因为全球 IPv4 地址池多年来一直处于枯竭状态。2011 年,互联网号码分配机构 (IANA) 将最后剩余的地址块分配给了区域互联网注册管理机构 (RIR),此后,企业再也无法按需获得大量新的地址分配。 入站 IPv4 地址租赁—引入地址 入站租赁是指企业从供应商处获取 IPv4 地址,用于自身业务使用。 企业为什么选择入站租赁 当组织现有的 IPv4 资源不足以支持以下需求时,通常会选择入站租赁: 扩展数字服务 支持新的基础设施 维持依赖 IPv4 的应用程序 Related Posts 企业入站与出站 IPv4 租赁完整指南 租赁 IPv4 地址可以转移部分伴随完全所有权而来的风险。例如,购买地址可能会让组织暴露于价格波动、长期贬值风险以及信誉管理责任之中。通过 i.Lease 进行租赁,企业可以降低这些风险暴露,并在明确期限内维持可预测的成本,从而支持更可靠的预算规划和风险管理实践。这种方式也简化了基础设施管理,因为租赁供应商通常会负责滥用监控、信誉检查和注册机构协调,使承租方能够专注于核心业务功能,而不是 IP 资产管理。IPv4 租赁并不限于单一行业。托管服务商、云平台、电信公司、SaaS 公司和网络安全企业都可以从租赁中受益。例如,托管服务商可以在无需大量前期投资的情况下扩展服务器部署,而网络安全公司则可以根据客户需求灵活增加地址空间,而无需承诺完全购买。在销售、营销和监管测试中,租赁允许组织在特定地区试运行部署,而无需投入大量资本。这种战略灵活性支持创新,同时帮助企业在 IPv4 稀缺持续存在的市场中保持韧性。利用 i.Lease 进行 IPv4 租赁管理的好处非常清楚:具成本效益的访问、快速部署、信誉安全、可扩展性、地理多样性和持续支持。在 IPv4 地址稀缺且直接购买成本高昂的环境中,通过值得信赖的平台进行租赁,使组织能够维持连接、按需扩展基础设施,并高效管理资源。通过将 IPv4 租赁视为基础设施规划的重要组成部分,而不是临时替代方案,企业可以在应对 IPv4 Understanding Operational Risk in IPv4 Address Markets IPv4 has long stopped being a simple technical identifier system. It has become a constrained, priced, and operationally embedded infrastructure Por qué la mayoría de las empresas están expuestas accidentalmente al riesgo de fallo en la asignación de IPv4 La escasez de IPv4 es ampliamente comprendida. Lo que muchas empresas aún subestiman es el riesgo de continuidad relacionado con .related-post {} .related-post .post-list { text-align: left; } .related-post .post-list .item { margin: 5px; padding: 10px; } .related-post .headline { font-size: 18px !important; color: #999999 !important; } .related-post .post-list .item .post_thumb { max-height: 220px; margin: 10px 0px; padding: 0px; display: block; } .related-post .post-list .item .post_title { font-size: 16px; color: #3f3f3f; margin: 10px 0px; padding: 0px; display: block; text-decoration: none; } .related-post .post-list .item .post_excerpt { font-size: 13px; color: #3f3f3f; margin: 10px 0px; padding: 0px; display: block; text-decoration: none; } @media only screen and (min-width: 1024px) { .related-post .post-list .item { width: 30%; } } @media only screen and (min-width: 768px) and (max-width: 1023px) { .related-post .post-list .item { width: 90%; } } @media only screen and (min-width: 0px) and (max-width: 767px) { .related-post .post-list .item { width: 90%; } }
大多数企业为何会意外面临 IPv4 地址分配失败的风险
IPv4 稀缺性已被广泛理解。许多企业仍然低估的是:地址资源如何被治理和维护所带来的连续性风险。 企业往往在持续使用 IPv4 资源的同时,并没有完全看清支撑这些分配的连续性条件。 对租赁、转让和供应商管理型基础设施的依赖不断增加,正在将 IPv4地址分配 重塑为一个长期治理问题。 IPv4地址分配已悄然成为连续性问题 对许多企业 IT 团队来说,IPv4 地址看起来仍然在运营上保持稳定。 应用程序仍然可以访问。云平台继续扩展。连接服务供应商在没有明显中断的情况下提供服务。从外部看,互联网似乎仍像过去一样运行。 然而,在这种运营稳定性之下,IPv4地址分配的结构已经发生了根本变化。 可自由分配的 IPv4 空间耗尽早已不是新闻。American Registry for Internet Numbers (ARIN) 于 2015 年耗尽其可用 IPv4 池,而 RIPE NCC 于 2019 年随后耗尽。(arin.net)(ripe.net) 取代旧分配环境的,是一个围绕以下内容建立的更分层运营模式: 转让 租赁 供应商管理型地址 回收 二级分配安排 对许多组织来说,这些变化是逐渐发生的,因此其背后连续性假设的转变很大程度上没有被注意到。因此,企业现在面临的并不只是地址稀缺,而是越来越暴露于 IPv4地址分配失败风险 ——也就是连续性、可携带性或长期运营灵活性变得比预期更不确定的情况。 问题通常是可见性,而不是即时短缺 这个问题仍然被低估的原因之一,是大多数企业并不会把 IPv4 scarcity 体验成即时宕机问题。基础设施仍在运行。 相反,风险通常会在转型时刻浮现: 云迁移 供应商整合并购 区域扩展 基础设施重组 合规驱动的迁移 在这些情况下,组织有时会发现,运营使用和连续性可见性并不是同一回事。企业可能已经在生产环境中积极使用 IPv4 资源多年,却对以下方面了解有限: 分配来源 注册机构关系 转让历史 可携带性条件 上游依赖 续期风险暴露 这并不一定表示运营实践不佳。现代基础设施环境随着时间推移变得越来越抽象。云采用和软件定义基础设施简化了部署,但也减少了企业与支撑互联网号码资源的治理层之间的直接互动。 IPv4地址分配已从采购演变为管理责任 过去,组织通常把IPv4地址分配视为直接的运营需求。额外地址空间往往可以通过 Regional Internet Registries (RIRs) Related Posts Understanding Operational Risk in IPv4 Address Markets IPv4 has long stopped being a simple technical identifier system. It has become a constrained, priced, and operationally embedded infrastructure La Running-Code Primacy: por qué el arrendamiento de IPv4 debe juzgarse mediante pruebas operativas El arrendamiento de IPv4 suele comenzar con una pregunta simple: ¿Puede este proveedor darnos las direcciones? Pero para las empresas Pourquoi la plupart des entreprises sont exposées accidentellement au risque d’échec d’attribution d’adresse IPv4 La rareté de l’IPv4 est largement comprise. Ce que de nombreuses entreprises sous-estiment encore, c’est le risque de continuité lié .related-post {} .related-post .post-list { text-align: left; } .related-post .post-list .item { margin: 5px; padding: 10px; } .related-post .headline { font-size: 18px !important; color: #999999 !important; } .related-post .post-list .item .post_thumb { max-height: 220px; margin: 10px 0px; padding: 0px; display: block; } .related-post .post-list .item .post_title { font-size: 16px; color: #3f3f3f; margin: 10px 0px; padding: 0px; display: block; text-decoration: none; } .related-post .post-list .item .post_excerpt { font-size: 13px; color: #3f3f3f; margin: 10px 0px; padding: 0px; display: block; text-decoration: none; } @media only screen and (min-width: 1024px) { .related-post .post-list .item { width: 30%; } } @media only screen and (min-width: 768px) and (max-width: 1023px) { .related-post .post-list .item { width: 90%; } } @media only screen and (min-width: 0px) and (max-width: 767px) { .related-post .post-list .item { width: 90%; } }

运行代码优先性:为什么 IPv4 租约应该以运行证明来评判
IPv4 租赁通常始于一个简单的问题: 这个供应商能不能给我们这些地址? 但对于依赖 IPv4 来支持托管、VPN、SaaS、云、电信、安全、电子邮件投递或面向客户平台的企业来说,这个问题还不够。 更好的问题是: 这个 IPv4 结构能否证明它在运营上可行? 这正是 Running-Code Primacy 重要的地方。 Running-Code Primacy 意味着,真实运行中的运营现实,应该优先于机构语言、销售说法、流程上的安心感或抽象承诺。在 IPv4 地址市场中,企业不应只通过价格、地址块大小或精美的销售页面来判断 IPv4 供应商。企业应该通过证据来判断:该地址空间是否可以路由、续期、记录、支持,并在生产环境中保持稳定。 对 i.lease 来说,商业启示很直接: IPv4 访问应该通过运营证明来评估,而不只是纸面上的可用性。 什么是 Running-Code Primacy? Running-Code Primacy 是一种理念,认为互联网治理和资源协调应始终以正在运行的网络为基础。 互联网工程传统长期重视实际实现,而不是理论设计。Running-Code Primacy 背后的原则主张,号码资源协调应通过运行中网络的技术需求来解释,而不是通过广泛的机构权威来解释。 对于 IPv4 地址市场,这一原则可以转化为商业语言: 不要只依赖说法。要寻找证明。 供应商可能会说 IPv4 地址块可用。但它能否支持路由?能否提供文件?能否说明来源控制?能否处理续期?当信誉或滥用问题出现时,它能否回应?部署之后,它能否保持客户网络稳定? Running-Code Primacy 并不意味着忽略合同、记录或治理。这些仍然重要。它意味着最终测试应该是运营现实。 如果一个 IPv4 安排无法支持正在运行的网络,那就还不够。 为什么 IPv4 买家和租户应该重视 IPv4 不只是基础设施预算中的一个项目。 对许多企业来说,IPv4 支撑着真实系统: 托管平台 云服务 VPN 网关 SaaS 应用 企业访问控制 电子邮件基础设施 电信系统 安全工具 面向客户的网站 API 端点 监控系统 Related Posts 企业入站与出站 IPv4 租赁完整指南 租赁 IPv4 地址可以转移部分伴随完全所有权而来的风险。例如,购买地址可能会让组织暴露于价格波动、长期贬值风险以及信誉管理责任之中。通过 i.Lease 进行租赁,企业可以降低这些风险暴露,并在明确期限内维持可预测的成本,从而支持更可靠的预算规划和风险管理实践。这种方式也简化了基础设施管理,因为租赁供应商通常会负责滥用监控、信誉检查和注册机构协调,使承租方能够专注于核心业务功能,而不是 IP 资产管理。IPv4 租赁并不限于单一行业。托管服务商、云平台、电信公司、SaaS 公司和网络安全企业都可以从租赁中受益。例如,托管服务商可以在无需大量前期投资的情况下扩展服务器部署,而网络安全公司则可以根据客户需求灵活增加地址空间,而无需承诺完全购买。在销售、营销和监管测试中,租赁允许组织在特定地区试运行部署,而无需投入大量资本。这种战略灵活性支持创新,同时帮助企业在 IPv4 稀缺持续存在的市场中保持韧性。利用 i.Lease 进行 IPv4 租赁管理的好处非常清楚:具成本效益的访问、快速部署、信誉安全、可扩展性、地理多样性和持续支持。在 IPv4 地址稀缺且直接购买成本高昂的环境中,通过值得信赖的平台进行租赁,使组织能够维持连接、按需扩展基础设施,并高效管理资源。通过将 IPv4 租赁视为基础设施规划的重要组成部分,而不是临时替代方案,企业可以在应对 IPv4 Risques liés au renouvellement d’IPv4 : quand le manque de responsabilisation se transforme en trahison du code en cours d’exécution La plupart des entreprises entrent sur le marché IPv4 avec un objectif simple. Elles ont besoin d’adresses. Peut-être en ont-elles 大多数企业为何会意外面临 IPv4 地址分配失败的风险 IPv4 稀缺性已被广泛理解。许多企业仍然低估的是:地址资源如何被治理和维护所带来的连续性风险。 企业往往在持续使用 IPv4 资源的同时,并没有完全看清支撑这些分配的连续性条件。 对租赁、转让和供应商管理型基础设施的依赖不断增加,正在将 IPv4地址分配 重塑为一个长期治理问题。 IPv4地址分配已悄然成为连续性问题 对许多企业 IT 团队来说,IPv4 地址看起来仍然在运营上保持稳定。 应用程序仍然可以访问。云平台继续扩展。连接服务供应商在没有明显中断的情况下提供服务。从外部看,互联网似乎仍像过去一样运行。 然而,在这种运营稳定性之下,IPv4地址分配的结构已经发生了根本变化。 可自由分配的 IPv4 空间耗尽早已不是新闻。American Registry for .related-post {} .related-post .post-list { text-align: left; } .related-post .post-list .item { margin: 5px; padding: 10px; } .related-post .headline { font-size: 18px !important; color: #999999 !important; } .related-post .post-list .item .post_thumb { max-height: 220px; margin: 10px 0px; padding: 0px; display: block; } .related-post .post-list .item .post_title { font-size: 16px; color: #3f3f3f; margin: 10px 0px; padding: 0px; display: block; text-decoration: none; } .related-post .post-list .item .post_excerpt { font-size: 13px; color: #3f3f3f; margin: 10px 0px; padding: 0px; display: block; text-decoration: none; } @media only screen and (min-width: 1024px) { .related-post .post-list .item { width: 30%; } } @media only screen and (min-width: 768px) and (max-width: 1023px) { .related-post .post-list .item { width: 90%; } } @media only screen and (min-width: 0px) and (max-width: 767px) { .related-post .post-list .item { width: 90%; } }
