IP Reputation vs. IP Risk Score: What’s the Difference
A clear comprehension of the discrepancies between IP reputation and IP risk score constitutes a critical prerequisite for effective cybersecurity governance — the former encapsulates historical trustworthiness, while the latter forecasts potential threat vulnerabilities.
Table of Contents
Key Points
- IP reputation embodies the historical trustworthiness and past behavioural patterns of an IP address, exerting a direct influence on email deliverability and network access permissions.
- IP risk score integrates a broader spectrum of threat indicators and behavioural metrics to quantify the probability of malicious activity, with applications in fraud prevention, intrusion detection, and dynamic security screening protocols.
What is IP Reputation?
IP reputation can be formally defined as a quantitative and qualitative assessment of an IP address’s “trustworthiness” predicated on its historical behavioural patterns and operational track record.
This concept operates analogously to a credit scoring mechanism: an IP address with an unblemished history — characterized by the absence of spam dissemination, malware distribution, or abuse reports — attains a positive reputation. Conversely, involvement in suspicious or malicious activities such as spam propagation, phishing campaigns, or malware dissemination results in a degradation of reputation.
For instance, numerous email service providers, network security systems, and firewall solutions leverage IP reputation as a core criterion for filtering incoming traffic or email communications: IP addresses with compromised reputations may be subjected to blocking, quarantining, or flagging.
Owing to its focus on historical performance, IP reputation tends to exhibit relative stability (albeit with the potential for temporal changes). Adherence to cybersecurity hygiene practices — including the avoidance of spam, compliance with email sending best practices, and the prevention of abusive behaviours — is instrumental in sustaining a favourable reputation.
What is IP Risk Score?
An IP risk score — alternatively termed an IP risk rating or IP fraud score — represents a dynamic and comprehensive evaluative framework designed to estimate the likelihood that an IP address is currently engaged in, or will imminently undertake, malicious activity, fraudulent behaviour, or other unwanted operational conduct.
In contrast to the retrospective focus of IP reputation, IP risk scoring systems aggregate a multifaceted set of variables: geolocation data, associations with proxy servers or virtual private networks (VPNs), entries in known blacklists, anomalous behavioural patterns (e.g., abrupt traffic surges, unauthorized login attempts, port scanning activities), and IP usage classification (e.g., residential IP, data-centre IP).
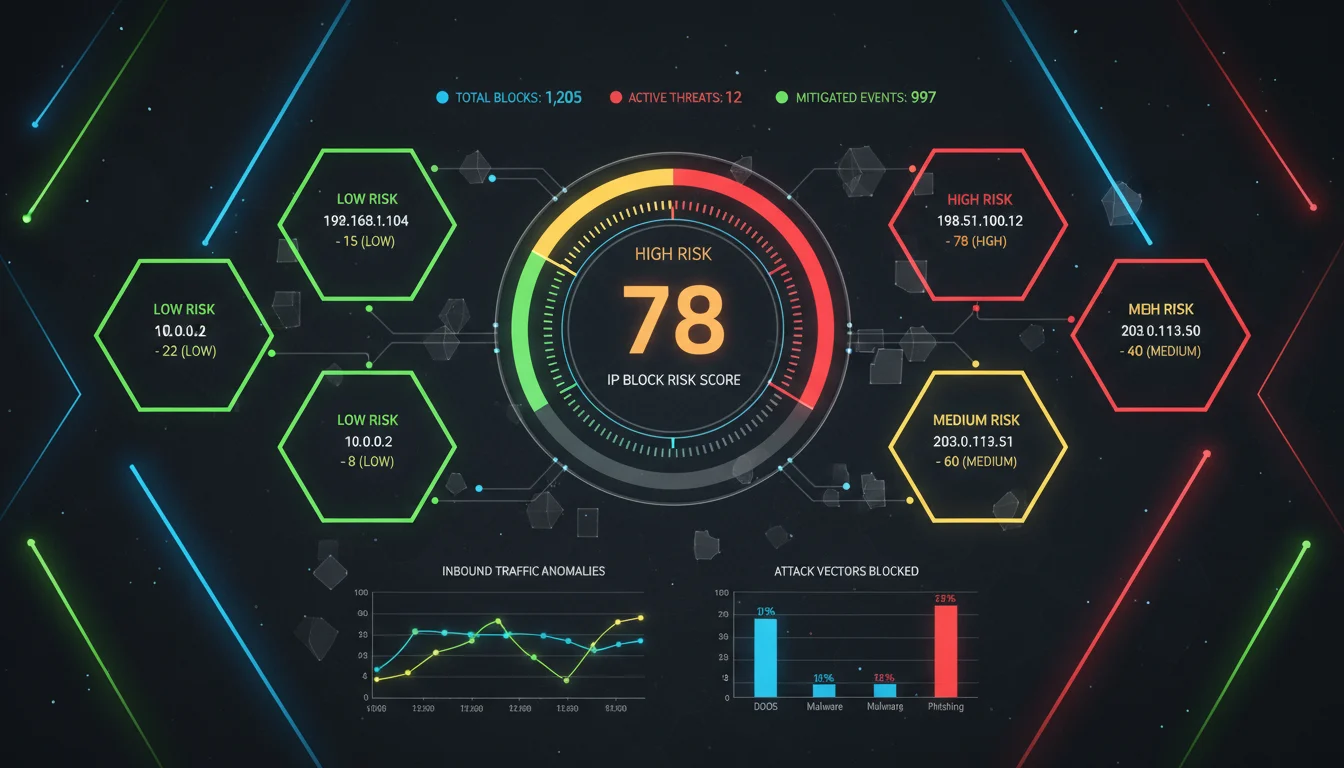
These scores are typically presented within predefined numerical ranges — for example, certain service providers employ scales of 0–100 or analogous gradients — wherein higher scores correspond to elevated risk levels or an increased probability of malicious intent.
IP risk scores are extensively deployed in real-time security contexts: e-commerce platforms utilize them to detect fraudulent transactions, financial institutions employ them for screening suspicious login attempts or monetary operations, online services leverage them to block bot or proxy traffic, and network security personnel utilize them to trigger enhanced scrutiny or proactive blocking measures.
Why the Distinction Matters
While IP reputation and IP risk score share conceptual overlaps, conflating these two constructs can lead to erroneous security judgments and suboptimal decision-making.
- Static vs. Dynamic Perspectives: IP reputation offers a retrospective analytical lens, documenting the historical actions of an IP address. In contrast, IP risk score provides a predictive or contextual assessment, forecasting potential future behaviours based on real-time signals and environmental factors.
- Divergent Use Cases: Reputation metrics are predominantly utilized for long-term trust evaluation, such as email deliverability optimization or the establishment of general network allow-lists. Risk scores, by contrast, are applied in real-time scenarios, including fraud detection, context-sensitive access control, and behavioural anomaly identification.
- Granularity and Nuance: Risk scoring frameworks incorporate transient behavioural indicators (e.g., sudden login attempts, proxy utilization) and environmental contextual data (e.g., geolocation, internet service provider type), dimensions that may not be fully captured by reputation-based assessments alone.
For organizations engaged in the development of secure systems — encompassing email servers, online platforms, and security-critical services — the synergistic application of both metrics can significantly enhance the reliability and robustness of security architectures.
How IP Reputation is Calculated: Typical Signals
IP reputation assessment services derive their evaluations from a diverse array of data sources:
- Historical email transmission patterns, spam or abuse complaint records, and entries in blacklist databases.
- Evidence of prior malicious activities, including malware distribution, botnet participation, and phishing campaigns.
- Email authentication verification and compliance adherence (for email-sending IPs): validation of proper Sender Policy Framework (SPF), DomainKeys Identified Mail (DKIM), and Domain-based Message Authentication, Reporting, and Conformance (DMARC) configurations, as well as maintenance of low bounce rates and complaint ratios.
Given its reliance on historical and aggregated data, the classification resulting from IP reputation analysis tends to be stable, with changes typically triggered by the occurrence of new negative events.
How IP Risk Score is Calculated: More Dynamic Signals
Risk scoring systems incorporate a broader and more dynamically updated set of evaluative criteria, including:
- Geolocation anomalies (e.g., IP addresses originating from high-risk regions, frequent geographic location shifts, or utilization of VPN/proxy services).
- IP type and internet service provider (ISP) classification: differentiation between data-centre, hosting provider, residential ISP, or proxy network-assigned IPs, with data-centre and proxy IPs often associated with elevated risk profiles.
- Behavioural patterns: irregular login frequencies, rapid sequential requests, port scanning activities, brute-force attack attempts, or other indicators of automated or bot-driven behaviour.
- Blacklist status: presence in known abuse repositories, spam/malware blacklists, or records of prior fraud or attack-related activities.
- Contextual data: integration with device fingerprinting information, session history, user-agent identifiers, or other metadata. Within fraud-prevention workflows, IP risk metrics may be combined with behavioural, transactional, or identity-related signals to enhance predictive accuracy.
As a consequence of this multifaceted data integration, IP risk scores can undergo rapid fluctuations: an IP address previously classified as “clean” based on reputation may be flagged as high-risk if it exhibits suspicious usage patterns, and vice versa.
IP-based indicators are noisy and prone to false positives, so they should be used cautiously as only one component of a broader risk-assessment strategy
-Sarabi, Karir & Liu, “Scoring the Unscorables: Cyber Risk Assessment Beyond Internet Scans.
Use Cases: When to Rely on Reputation, When on Risk Score
Email and Deliverability Systems
Organizations operating email service providers, marketing platforms, or transactional email services frequently rely on IP reputation to determine the routing of incoming mail or to filter unwanted content. A positive reputation is critical for ensuring message delivery to recipient inboxes, while a compromised reputation may result in blocking, quarantining, or deliverability impairments.
Real-Time Security and Fraud Prevention
Platforms facilitating user logins, financial transactions, or access to sensitive data commonly employ IP risk scores as integral components of fraud detection or intrusion prevention systems. Suspicious IP addresses may be flagged for additional verification, subjected to access restrictions, or blocked outright.
Zero-Trust and Adaptive Security Architectures
Within zero-trust security frameworks — which operate on the principle of “never trust, always verify” — every connection, login attempt, or data access request is subject to dynamic evaluation. In this context, IP reputation serves as a baseline trust indicator, while IP risk scores (reflecting real-time contextual data) trigger adaptive security controls in response to detected high-risk signals.
External Attack Surface and Threat-Intelligence Monitoring
Organizations engaged in monitoring their external digital attack surfaces utilize reputation data to maintain “clean” IP address pools, while simultaneously applying risk scoring methodologies to preempt emerging threats or vulnerabilities.

Why Using Both Matters: Layered Security and Trust
Exclusive reliance on IP reputation can create security vulnerabilities: an IP address with a positive historical record may be compromised at a later stage, rendering reputation-based assessments obsolete. Conversely, overreliance on IP risk scores may result in the over-flagging of benign IP addresses, leading to unnecessary disruptions.
By integrating both metrics — historical trustworthiness (reputation) and real-time risk context (risk score) — organizations can implement a nuanced, layered security approach:
- Leverage reputation metrics for long-term allow-list configurations, baseline trust evaluations, and email deliverability decisions.
- Utilize risk scores for real-time decision-making processes, including adaptive security protocols (e.g., login risk assessment, fraud detection, content filtering).
This hybrid strategy achieves a balance between operational reliability and security resilience, enabling organizations to trust legitimate actors while maintaining vigilance against emerging threats.
IP risk scoring is now a core defence layer in an era where threats hide inside trusted infrastructures
—Alex Morgan, Cybersecurity Strategist
Challenges and Limitations
Data Quality and Coverage
Reputation databases are contingent upon the accuracy and timeliness of historical activity records. For IP addresses with insufficient monitoring (e.g., newly allocated IPs, dynamically assigned addresses, shared IP pools), reputation assessments may be incomplete or misleading.
Risk scoring systems depend on the integration of multiple data sources and heuristic algorithms, which inherently introduce the potential for false positives and false negatives — particularly in edge cases involving legitimate users utilizing VPNs or proxy services.
Dynamic IP Allocation and Shared Hosting Environments
Modern cloud hosting, shared hosting, and VPN services frequently reuse IP addresses across multiple clients. This practice means that an IP address classified as “clean” at one point may subsequently be utilized for malicious purposes, thereby compromising both reputation and risk assessments.
Transparency and Interpretability
IP risk scores are often generated by proprietary algorithms incorporating numerous variables, making it challenging for organizations to interpret the specific factors contributing to a given IP’s classification. This lack of transparency can hinder the implementation of targeted corrective actions.
Over-Blocking and Business Impact
Excessive reliance on risk scores may result in the blocking or challenging of legitimate users, negatively impacting user experience — particularly among privacy-conscious individuals, VPN users, or legitimate users accessing services via proxy servers.
Expert Perspective
Security analysts emphasize that “IP reputation serves as a foundational component of modern spam and threat filtering mechanisms, providing a framework for identifying trustworthy IP addresses.”
Concurrently, within zero-trust security environments, “reputation alone is insufficient to govern access decisions — real-time risk signals must be integrated to enable dynamic security responses.”
Industry practitioners consistently advocate that “robust cybersecurity requires a layered approach to metrics, combining historical reputation data with real-time risk scoring to adapt to the evolving threat landscape.”
Best Practices for Organisations
Dual Monitoring of Reputation and Risk
Avoid treating IP reputation and IP risk score as interchangeable metrics; each fulfills distinct functions within security and deliverability infrastructure.
Prioritize Risk Scoring for High-Sensitivity Events
Deploy IP risk scores for critical operations such as user logins, financial transactions, registration processes, and access to sensitive data.
Leverage Reputation for Baseline Trust and Long-Term Decisions
Utilize IP reputation for email sending optimization, general firewall whitelisting, and the management of low-risk traffic flows.
Regular Re-evaluation of IP Pools
Conduct periodic assessments of IP address pools — especially those associated with shared hosting or cloud services — to identify reputation degradation or sudden risk spikes.
Integrate IP Signals with Multifactor Authentication Combine IP-based metrics with device fingerprinting, behavioural monitoring, and user authentication protocols to enhance overall security posture.
Trusted IPv4 Leasing for Business Growth
Get enterprise-grade IPv4 space quickly, with seamless deployment and end-to-end management.
Get Started with i.leaseFrequently Asked Questions
Q1: Can an IP Address Possess a Good Reputation but a High Risk Score?
Yes. An IP address may maintain a clean historical record (positive reputation) while exhibiting current risky behaviours or operating within a high-risk environment (e.g., VPN usage, shared data-centre infrastructure), resulting in a elevated risk score.
Q2: Is IP Risk Score More Effective Than IP Reputation for Fraud Prevention?
Generally, yes. IP risk scores incorporate dynamic environmental factors (e.g., proxy utilization, geolocation anomalies, suspicious activity patterns) beyond the scope of historical reputation, rendering them more suitable for fraud detection and real-time security decision-making.
Q3: Can an IP Address’s Reputation Improve Over Time?
Yes. An IP address previously associated with abusive behaviours can gradually restore its reputation if it maintains a sustained period of compliant operation — characterized by the absence of spam, malicious activity, or abuse reports — as recognized by reputation assessment services.
Q4: Are There Standardized Ranges for IP Risk Scores, or Are They Vendor-Specific?
IP risk score ranges are predominantly vendor-specific. Different service providers employ varying scales (e.g., 0–100, 0–10, or custom risk categorizations) based on their proprietary algorithms and data models.
Q5: Should Organisations Rely Exclusively on One Metric (Reputation or Risk Score)?
No. Best practice mandates the combined utilization of both metrics: reputation for baseline trust evaluation and long-term reliability assessments, and risk score for dynamic, context-aware security and fraud prevention.
Related Blogs
相关文章

运行代码优先性:为什么 IPv4 租约应该以运行证明来评判
IPv4 租赁通常始于一个简单的问题: 这个供应商能不能给我们这些地址? 但对于依赖 IPv4 来支持托管、VPN、SaaS、云、电信、安全、电子邮件投递或面向客户平台的企业来说,这个问题还不够。 更好的问题是: 这个 IPv4 结构能否证明它在运营上可行? 这正是 Running-Code Primacy 重要的地方。 Running-Code Primacy 意味着,真实运行中的运营现实,应该优先于机构语言、销售说法、流程上的安心感或抽象承诺。在 IPv4 地址市场中,企业不应只通过价格、地址块大小或精美的销售页面来判断 IPv4 供应商。企业应该通过证据来判断:该地址空间是否可以路由、续期、记录、支持,并在生产环境中保持稳定。 对 i.lease 来说,商业启示很直接: IPv4 访问应该通过运营证明来评估,而不只是纸面上的可用性。 什么是 Running-Code Primacy? Running-Code Primacy 是一种理念,认为互联网治理和资源协调应始终以正在运行的网络为基础。 互联网工程传统长期重视实际实现,而不是理论设计。Running-Code Primacy 背后的原则主张,号码资源协调应通过运行中网络的技术需求来解释,而不是通过广泛的机构权威来解释。 对于 IPv4 地址市场,这一原则可以转化为商业语言: 不要只依赖说法。要寻找证明。 供应商可能会说 IPv4 地址块可用。但它能否支持路由?能否提供文件?能否说明来源控制?能否处理续期?当信誉或滥用问题出现时,它能否回应?部署之后,它能否保持客户网络稳定? Running-Code Primacy 并不意味着忽略合同、记录或治理。这些仍然重要。它意味着最终测试应该是运营现实。 如果一个 IPv4 安排无法支持正在运行的网络,那就还不够。 为什么 IPv4 买家和租户应该重视 IPv4 不只是基础设施预算中的一个项目。 对许多企业来说,IPv4 支撑着真实系统: 托管平台 云服务 VPN 网关 SaaS 应用 企业访问控制 电子邮件基础设施 电信系统 安全工具 面向客户的网站 API 端点 监控系统Read more Related Posts Why most enterprises are accidentally exposed to IPv4 allocation failure risk IPv4 scarcity is widely understood. What many enterprises still underestimate is the continuity risk surrounding how address resources are governed Read more Why i.lease Exists: IPv4 Continuity Is Not Commodity Access Most businesses enter the IPv4 market with a simple goal. They need addresses. Maybe they need them for hosting.Maybe they Read more Running-Code Primacy: Why IPv4 Leasing Should Be Judged by Operational Proof IPv4 leasing often begins with a simple question:Can this provider give us the addresses?But for businesses that depend on IPv4 Read more .related-post {} .related-post .post-list { text-align: left; } .related-post .post-list .item { margin: 5px; padding: 10px; } .related-post .headline { font-size: 18px !important; color: #999999 !important; } .related-post .post-list .item .post_thumb { max-height: 220px; margin: 10px 0px; padding: 0px; display: block; } .related-post .post-list .item .post_title { font-size: 16px; color: #3f3f3f; margin: 10px 0px; padding: 0px; display: block; text-decoration: none; } .related-post .post-list .item .post_excerpt { font-size: 13px; color: #3f3f3f; margin: 10px 0px; padding: 0px; display: block; text-decoration: none; } @media only screen and (min-width: 1024px) { .related-post .post-list .item { width: 30%; } } @media only screen and (min-width: 768px) and (max-width: 1023px) { .related-post .post-list .item { width: 90%; } } @media only screen and (min-width: 0px) and (max-width: 767px) { .related-post .post-list .item { width: 90%; } }
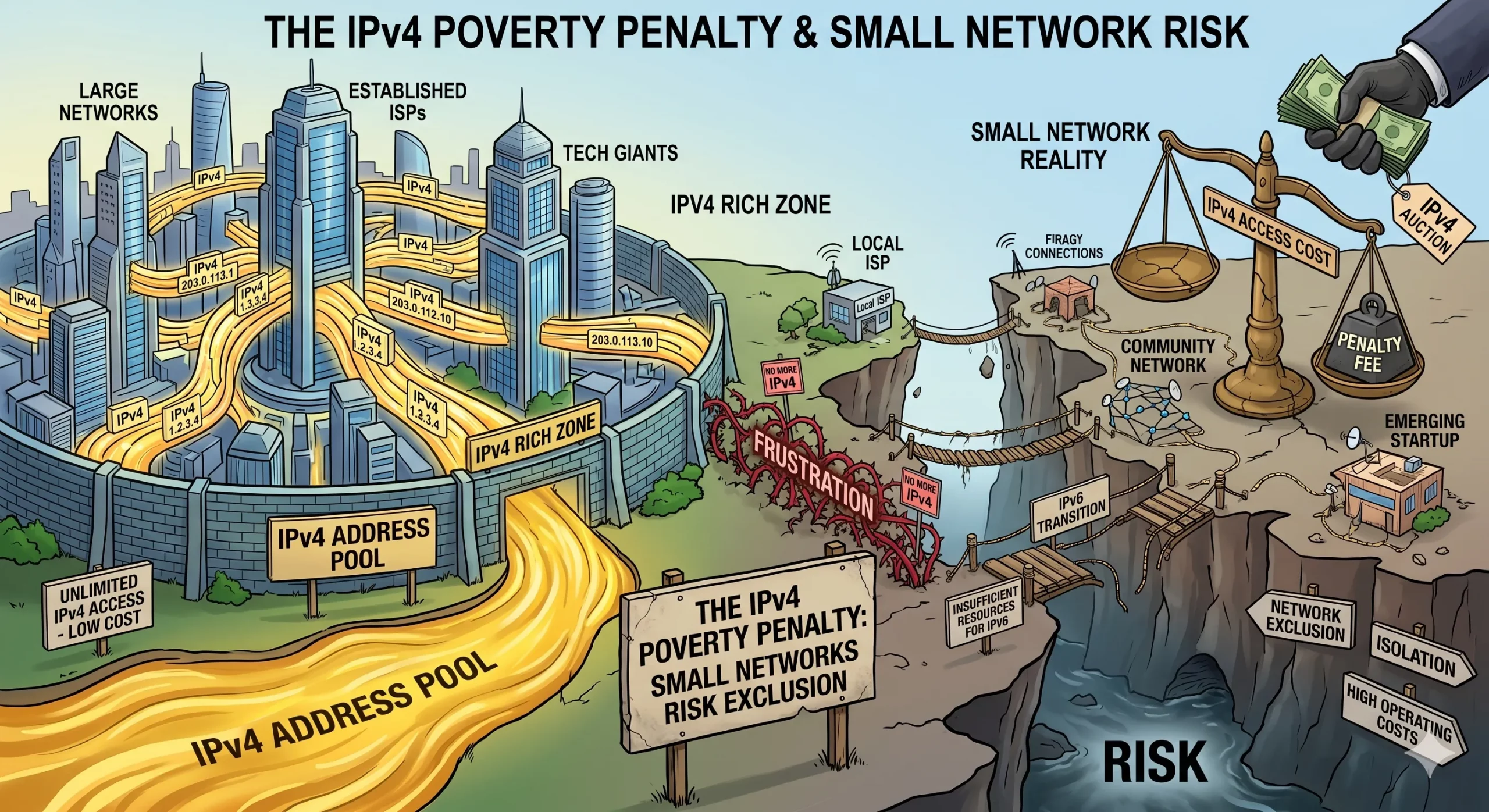
IPv4 贫困惩罚:为什么小型网络需要支付更多费用
IPv4 访问在纸面上可能看起来是一样的。 相同的注册机构表格。相同的转让规则。相同的供应商合同。相同的合规语言。相同的续期流程。 但相同的文件,并不总是带来相同的结果。 对于大型运营商来说,IPv4 摩擦可能是可以管理的。他们可能拥有法律团队、政策人员、网络工程师、合规支持、资本储备,以及足够多的客户来把延迟成本分摊到更大的业务规模中。 但对于较小的运营商来说,同样的摩擦可能变得危险。 IPv4 转让延迟可能拖慢扩张。文件问题可能阻碍部署。续期问题可能带来面向客户的风险。薄弱的供应商链条可能迫使紧急迁移。注册机构或政策争议可能消耗企业无法承受的资金。 这就是 IPv4 访问中 贫困惩罚 的实际含义:更贫困、更小型或利润率更薄的运营商,往往会为同样的不确定性付出更高代价,因为它们吸收延迟、流程和自由裁量风险的能力更弱。 危险不只是 IPv4 的价格。 危险在于它周围隐藏的成本。 什么是 IPv4 贫困惩罚? IPv4 贫困惩罚,是指较小型运营商在 IPv4 访问受到流程、延迟、不确定性、文件负担、供应商链条薄弱或注册层风险影响时所面对的隐藏成本。 这并不意味着小企业总是支付更高的每 IP 标价。有时会,有时不会。 更深层的问题是,较小型运营商往往支付更多间接成本。 它们没有足够资本来承受延迟。 它们没有足够人员来处理文件。 它们与供应商谈判的能力较弱。 如果出现争议,它们的法律承受能力较低。 如果地址块无法使用,它们的备用选择更少。 如果部署延迟,它们可能更快失去客户。 大型运营商可以把 IPv4 摩擦视为行政上的不便。较小型运营商却可能把同样的摩擦体验为对增长、服务交付或生存的直接威胁。 这就是为什么贫困惩罚不只是一个社会性说法。在 IPv4 访问中,它会变成运营现实。 为什么相同规则会产生不平等风险 许多系统声称自己是平等的,因为相同规则适用于所有人。 但在商业基础设施中,相同规则仍然可能产生不平等风险。 大型网络可能拥有了解转让要求的政策团队。较小型 ISP 可能只有一名工程师同时处理路由、客户支持、账单和合规。 云平台可能可以承受数周延迟,因为它有资本储备和备用容量。较小型托管服务商如果本月无法开始部署,可能就会失去客户。 跨国买家可能可以谈判更强的条款。较小型买家可能因为选择较少,而接受薄弱的供应商条件。 规则可能相同。 负担并不相同。 这就是为什么可见的 IPv4 价格只是实际成本的一部分。对小型企业来说,不确定性的隐藏成本可能比月租费或购买价差更大。 小型网络承担的隐藏成本 贫困惩罚会通过一些容易被忽视、直到直接冲击业务时才显现的成本出现。 1. 合规成本 较小型运营商可能需要准备文件、解释使用场景、验证记录、更新联系人、回应供应商问题,或满足转让要求,但它们通常没有专门的合规团队。 2. 延迟成本 延迟可能阻止新客户上线、推迟服务器部署、拖慢区域扩张,或阻碍服务按时上线。 3. 法律成本 如果出现争议,大型运营商可能可以吸收法律审查成本。较小型运营商可能因为成本太高而避免维护自身立场。 4. 工程成本 薄弱的供应商文件、不清晰的路由授权,或突然更换 IP,都可能消耗小团队难以轻易承担的工程时间。Read more Related Posts 运行代码优先性:为什么 IPv4 租约应该以运行证明来评判 IPv4 租赁通常始于一个简单的问题:这个供应商能不能给我们这些地址?但对于依赖 IPv4 来支持托管、VPN、SaaS、云、电信、安全、电子邮件投递或面向客户平台的企业来说,这个问题还不够。更好的问题是:这个 IPv4 结构能否证明它在运营上可行?这正是 Running-Code Primacy 重要的地方。Running-Code Primacy 意味着,真实运行中的运营现实,应该优先于机构语言、销售说法、流程上的安心感或抽象承诺。在 IPv4 地址市场中,企业不应只通过价格、地址块大小或精美的销售页面来判断 IPv4 供应商。企业应该通过证据来判断:该地址空间是否可以路由、续期、记录、支持,并在生产环境中保持稳定。对 i.lease 来说,商业启示很直接:IPv4 访问应该通过运营证明来评估,而不只是纸面上的可用性。什么是 Running-Code Primacy?Running-Code Read more Penalización por pobreza de IPv4: ¿Por qué las redes pequeñas pagan más? El acceso IPv4 puede parecer igual sobre el papel. Los mismos formularios de registro. Las mismas reglas de transferencia. Los Read more Pénalité liée à la pauvreté sur IPv4 : pourquoi les petits réseaux paient plus cher L’accès IPv4 peut sembler égal sur le papier.Les mêmes formulaires de registre.Les mêmes règles de transfert.Les mêmes contrats fournisseurs.Le même Read more .related-post {} .related-post .post-list { text-align: left; } .related-post .post-list .item { margin: 5px; padding: 10px; } .related-post .headline { font-size: 18px !important; color: #999999 !important; } .related-post .post-list .item .post_thumb { max-height: 220px; margin: 10px 0px; padding: 0px; display: block; } .related-post .post-list .item .post_title { font-size: 16px; color: #3f3f3f; margin: 10px 0px; padding: 0px; display: block; text-decoration: none; } .related-post .post-list .item .post_excerpt { font-size: 13px; color: #3f3f3f; margin: 10px 0px; padding: 0px; display: block; text-decoration: none; } @media only screen and (min-width: 1024px) { .related-post .post-list .item { width: 30%; } } @media only screen and (min-width: 768px) and (max-width: 1023px) { .related-post .post-list .item { width: 90%; } } @media only screen and (min-width: 0px) and (max-width: 767px) { .related-post .post-list .item { width: 90%; } }
如果无人承担续约风险,您的 IPv4 租约就不安全。
谁才是真正负责维持这个 IPv4 访问持续可用的人? 不是卖给你的人。不是介绍给你的人。不是开出发票的人。也不是发送第一份 LOA 的人。 当合作关系变得紧张、上游来源改变立场、文件受到质疑,或者供应商链条不再回应时,谁承担续期风险? 对于依赖 IPv4 来支持托管、SaaS、VPN、电信、云、安全、电子邮件投递或客户访问的企业来说,这不是一个小小的行政问题。 这是一个连续性问题。 当续期责任不清晰时,你的 IPv4 租赁可能会变成一个隐藏的倒计时。 为什么 IPv4 续期风险容易被忽视 大多数公司只会检查一个 IPv4 地址块今天是否可用。 他们检查 IP 是否可以路由。 他们检查地址块是否干净。 他们检查价格是否可以接受。 他们检查供应商是否能够快速交付。 这些检查都很重要。 但还不够。 IPv4 风险通常会在之后才出现,也就是企业已经围绕这些地址建立服务之后。到那时,这些 IP 可能已经绑定到客户账户、防火墙规则、邮件信誉、白名单、DNS 记录、应用基础设施、合规记录和内部运营流程。 到了那个阶段,更换 IP 就不再简单。 它可能意味着宕机、客户投诉、信誉损失、工程工作量增加,以及合同中断。 这就是为什么续期很重要。 IPv4 租赁的第一个月,只能证明访问已经被安排好。续期阶段,才能证明这个结构是否可靠。 一个薄弱的供应商在初期接入时可能看起来很强。真正的考验,是当租赁必须续期、被维护、被证明、被延长或被升级处理时。 访问与连续性之间的危险差异 IPv4 访问意味着你现在可以使用这些地址。 IPv4 连续性意味着你可以有信心继续使用这些地址。 许多公司混淆了这两者。 访问是短期的。连续性是结构性的。 访问回答的是: 我今天可以路由这些 IP 吗? 我现在可以部署服务器吗? 我可以收到 LOA 吗? 我可以开始使用这个地址块吗? 连续性提出的是更深层的问题: 谁控制来源关系? 谁负责续期责任? 谁支持路由变更? 如果文件受到质疑,谁来回应? 谁在压力到达客户之前吸收上游压力? 谁具备法律、运营和注册机构相关能力来保护连续性? 这种差异很重要,因为 IPv4 已经不再是随意的技术输入。它支撑着真实的业务活动、客户访问、收入、基础设施和运营连续性。注册层和认可层可能位于有价值的网络资源之上,而一旦连续性中断,运营商和客户承担的是真正的业务后果。 这就是为什么最便宜的 IPv4Read more Related Posts Why i.lease Exists: IPv4 Continuity Is Not Commodity Access Most businesses enter the IPv4 market with a simple goal. They need addresses. Maybe they need them for hosting.Maybe they Read more Running-Code Primacy: Why IPv4 Leasing Should Be Judged by Operational Proof IPv4 leasing often begins with a simple question:Can this provider give us the addresses?But for businesses that depend on IPv4 Read more IPv4 Poverty Penalty: Why Small Networks Pay More IPv4 access can look equal on paper.The same registry forms.The same transfer rules.The same provider contracts.The same compliance language.The same Read more .related-post {} .related-post .post-list { text-align: left; } .related-post .post-list .item { margin: 5px; padding: 10px; } .related-post .headline { font-size: 18px !important; color: #999999 !important; } .related-post .post-list .item .post_thumb { max-height: 220px; margin: 10px 0px; padding: 0px; display: block; } .related-post .post-list .item .post_title { font-size: 16px; color: #3f3f3f; margin: 10px 0px; padding: 0px; display: block; text-decoration: none; } .related-post .post-list .item .post_excerpt { font-size: 13px; color: #3f3f3f; margin: 10px 0px; padding: 0px; display: block; text-decoration: none; } @media only screen and (min-width: 1024px) { .related-post .post-list .item { width: 30%; } } @media only screen and (min-width: 768px) and (max-width: 1023px) { .related-post .post-list .item { width: 90%; } } @media only screen and (min-width: 0px) and (max-width: 767px) { .related-post .post-list .item { width: 90%; } }
